Professional Documents
Culture Documents
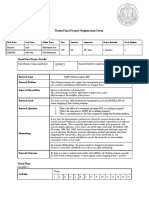
Kabul University Computer Science Faculty Information Systems Department
Kabul University Computer Science Faculty Information Systems Department
Uploaded by
abdulsattarOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Kabul University Computer Science Faculty Information Systems Department
Kabul University Computer Science Faculty Information Systems Department
Uploaded by
abdulsattarCopyright:
Available Formats
Kabul University
Computer Science Faculty
Information Systems Department
1. Overview of Computer Security
Adapted from:
Introduction to Computer Security, Matt Bishop
Hedayat Lodin | Sunday, November 01, 2020
OUTLINE
Security
Information Security
Security Basic Components(Sec. Requirements)
Confidentiality
Integrity
Availability
Accountability
Vulnerability, Threat, Attack
Common Security Attacks
Saturday, January 02, 2021 Information Systems Department 2
Computer Science Faculty
Kabul University
OUTLINE
Threat
Security policy
Security Measures
Useful information?
Essential Securities for Orgs
Information System Components
Saturday, January 02, 2021 Information Systems Department 3
Computer Science Faculty
Kabul University
SECURITY
The ability of a system to protect itself from accidental or
deliberate attacks.
Information Security:
The protection of information and its critical elements,
including the systems and hardware that use, store, and
transmit that information.
Saturday, January 02, 2021 Information Systems Department 4
Computer Science Faculty
Kabul University
INFORMATION SECURITY
Information Security is defending digital information from
unauthorized:
Access
Use
Recording
Disruption / Interference
Modification
Destruction / Damage
Saturday, January 02, 2021 Information Systems Department 5
Computer Science Faculty
Kabul University
THE BASIC COMPONENTS
Computer security rests on:
Confidentiality
Integrity
Availability
Accountability
Saturday, January 02, 2021 Information Systems Department 6
Computer Science Faculty
Kabul University
THE BASIC COMPONENTS
Computer security rests on:
Confidentiality
Integrity
Availability
Accountability
Also called Security Attributes/Security Goals/Security
Requirements.
These attributes form the main objective of any security
system.
Saturday, January 02, 2021 Information Systems Department 7
Computer Science Faculty
Kabul University
THE BASIC COMPONENTS
All security policies, controls, mechanisms, and safeguards
are implemented to provide one or more of these attributes.
All risks, threats, and vulnerabilities are measured for their
potential capability to compromise one or all of the
attributes.
Saturday, January 02, 2021 Information Systems Department 8
Computer Science Faculty
Kabul University
THE BASIC COMPONENTS [Confidentiality]
The concealment of information or resources.
The need for keeping information secret arises from the use of
computers in sensitive fields.
keeping information secret from all but those who are authorized
to see it.
Also called secrecy or privacy
Saturday, January 02, 2021 Information Systems Department 9
Computer Science Faculty
Kabul University
THE BASIC COMPONENTS [Confidentiality]
Access control mechanisms support confidentiality.
One access control mechanism confidentiality is
cryptography.
A cryptographic key controls access to the unscrambled /
decoded data, but then the cryptographic key itself becomes
another datum to be protected.
Saturday, January 02, 2021 Information Systems Department 10
Computer Science Faculty
Kabul University
THE BASIC COMPONENTS [Integrity]
Preventing improper or unauthorized change.
Refers to the trustworthiness of data or resources.
Ensuring information has not been altered by
unauthorized or unknown means.
Integrity mechanisms fall into two classes:
Prevention mechanisms
Detection mechanisms
Saturday, January 02, 2021 Information Systems Department 11
Computer Science Faculty
Kabul University
THE BASIC COMPONENTS [Integrity]
Prevention mechanisms:
Block unauthorized attempts to change the data.
Detection mechanisms:
Report that the data’s integrity is no longer trustworthy.
Analyze system events to detect problems.
Saturday, January 02, 2021 Information Systems Department 12
Computer Science Faculty
Kabul University
THE BASIC COMPONENTS [Integrity]
Working with integrity is very different from working with
confidentiality.
With confidentiality, the data is either compromised or it is
not, but integrity includes both the correctness and the
trustworthiness of the data.
Saturday, January 02, 2021 Information Systems Department 13
Computer Science Faculty
Kabul University
THE BASIC COMPONENTS [Availability]
Refers to the ability to use the information.
The aspect of availability that is relevant to security is that
someone may deliberately arrange to deny access to data
or to a service by making it unavailable (Denial of Service
Attacks).
keeping information accessible by authorized users when
required.
Saturday, January 02, 2021 Information Systems Department 14
Computer Science Faculty
Kabul University
THE BASIC COMPONENTS [Accountability]
Refers to the availability and integrity of the identity of the
person who performed an operation.
Accountability requires a clear definition of roles and
responsibilities for each team member.
The requirements of accountability are detection and
separation.
Saturday, January 02, 2021 Information Systems Department 15
Computer Science Faculty
Kabul University
VULNERABILITY, THREAT, AND ATTACK
A vulnerability: is a weakness in system design or
implementation and can be in hardware or software.
Example: a software bug exists in the OS, or no password rules are
set.
Saturday, January 02, 2021 Information Systems Department 16
Computer Science Faculty
Kabul University
VULNERABILITY, THREAT, AND ATTACK
A Threat is a set of circumstances that has the potential to
cause loss or harm
Is an indication of potential undesirable event
It refers to a situation in which
A person could do something undesirable (an attacker
initiating a denial-of service attack against an organization's email
server), or
A natural occurrence could cause an undesirable outcome (a
fire damaging an organization's information technology hardware).
Saturday, January 02, 2021 Information Systems Department 17
Computer Science Faculty
Kabul University
VULNERABILITY, THREAT, AND ATTACK
A Risk is the possibility of suffering harm or loss.
An attack: is a realization of a threat
An attacker: is a person who exploit a vulnerability
An attacker must have means, opportunity, and motive.
Synonyms: enemy, adversary, opponent, eavesdropper, intruder.
Saturday, January 02, 2021 Information Systems Department 18
Computer Science Faculty
Kabul University
VULNERABILITY, THREAT, AND ATTACK
Hacker: A person who have advanced knowledge of operating
systems and programming languages
Might discover holes within systems and the reasons for such
holes
Share what they discover but never intentionally damage data
Cracker: The one who breaks into or violates the system
integrity of remote machines with the malicious intent, i.e.,
gaining unauthorized access
Might destroy vital data, deny legitimate users services
Saturday, January 02, 2021 Information Systems Department 19
Computer Science Faculty
Kabul University
VULNERABILITY, THREAT, AND ATTACK
A passive adversary is an adversary who is capable only of
reading from an unsecured channel
An active adversary is an adversary who may also transmit,
alter, or delete information on an unsecured channel
Saturday, January 02, 2021 Information Systems Department 20
Computer Science Faculty
Kabul University
COMMON SECURITY ATTACKS
Interruption, delay, denial of receipt or denial of service
System assets or information become unavailable or are rendered
unavailable
Interception or snooping
Unauthorized party gains access to information by browsing
through files or reading communications.
Modification or alteration
Unauthorized party changes information in transit or information
stored for subsequent access.
Saturday, January 02, 2021 Information Systems Department 21
Computer Science Faculty
Kabul University
COMMON SECURITY ATTACKS
Masquerade or spoofing
Spurious information is inserted into the system or network by
making it appears as if it is from a legitimate entity.
Saturday, January 02, 2021 Information Systems Department 22
Computer Science Faculty
Kabul University
THREATS
A potential violation of security.
The actions that could cause violation.
Those actions are called attacks.
Those who execute such actions are called attackers.
The security services, confidentiality, integrity,
availability, and accountability hostage threats to the
security of a system.
Saturday, January 02, 2021 Information Systems Department 23
Computer Science Faculty
Kabul University
THREATS
Threats are divided into four classes:
Disclosure
Deception
Disruption
Repudiation
Saturday, January 02, 2021 Information Systems Department 24
Computer Science Faculty
Kabul University
THREATS
Given a security policy’s specification of “secure” and “non-
secure” actions, these security mechanisms can:
Prevent the attack
Detect the attack
Recover from the attack
Saturday, January 02, 2021 Information Systems Department 25
Computer Science Faculty
Kabul University
THREATS [PREVENTION]
Means that an attack will fail.
Involves implementation of mechanisms that users cannot
override such as passwords have become widely accepted.
Saturday, January 02, 2021 Information Systems Department 26
Computer Science Faculty
Kabul University
THREATS [DETECTION]
Most useful when an attack cannot be prevented.
Accept that an attack will occur; the goal is to determine that
an attack is under way, or has occurred, and report it.
For example, give a warning when a user enters an incorrect
password three times.
Saturday, January 02, 2021 Information Systems Department 27
Computer Science Faculty
Kabul University
THREATS [RECOVERY]
Recovery has two forms.
The first is to stop an attack and to assess and repair any
damage caused by that attack.
As an example, if the attacker deletes a file, one recovery
mechanism would be to restore the file from backup tapes.
Saturday, January 02, 2021 Information Systems Department 28
Computer Science Faculty
Kabul University
THREATS [RECOVERY]
In a second form of recovery, the system continues to
function correctly while an attack is under way.
This type of recovery is quite difficult to implement because
of the complexity of computer systems.
It draws on techniques of fault tolerance as well as
techniques of security and is typically used in safety-critical
systems.
Saturday, January 02, 2021 Information Systems Department 29
Computer Science Faculty
Kabul University
SECURITY POLICY
A security policy states what is, and is not, allowed
Is a document describing a company’s security controls and
activities.
Does not specify technologies
Examples:
Policy: Password construction Account names must not be used
in passwords.
Policy: Confidentiality of Personal information all personal
information must be treated as confidential.
A security Policy is a guideline for implementing security
measures.
Saturday, January 02, 2021 Information Systems Department 30
Computer Science Faculty
Kabul University
SECURITY MEASURES
Security measures include techniques for ensuring:
Prevention: such as encryption, user authentication, one
time password, anti-virus, firewall, etc.
Detection: such as IDS (Intrusion Detection Systems),
Monitoring tools, Firewall log, digital signature, etc.
Reaction (or recovery): Such as Backup systems, OS’s recovery
points, etc.
Encryption, Digital Signature, User Authentication, Antivirus, IDS
and firewalls, Database Security, Web Security, etc.
Saturday, January 02, 2021 Information Systems Department 31
Computer Science Faculty
Kabul University
THE USEFUL INFORMATION?
Data
Information
What characteristics should information possess to be useful? It
should be: accurate, timely, complete, verifiable, consistent,
available.
Saturday, January 02, 2021 Information Systems Department 32
Computer Science Faculty
Kabul University
ESSENTIAL SECURITIES FOR ORGANIZATIONS
A successful organization should have the following multiple
layers of security in place to protect its operations:
Physical security
Personnel security
Operations security
Communications security
Saturday, January 02, 2021 Information Systems Department 33
Computer Science Faculty
Kabul University
INFORMATION SYSTEM COMPONENTS
Entire set of:
Data,
Software,
Hardware,
Networks,
People,
Procedures and
Policies
Saturday, January 02, 2021 Information Systems Department 34
Computer Science Faculty
Kabul University
INFORMATION SYSTEM COMPONENTS
These critical components enable information to be:
Input,
Processed,
Output, and
Stored.
Saturday, January 02, 2021 Information Systems Department 35
Computer Science Faculty
Kabul University
INFORMATION SYSTEM COMPONENTS
Each of these IS components has its own strengths and
weaknesses, as well as its own characteristics and uses.
Each component of the information system also has its own
security requirements.
Saturday, January 02, 2021 Information Systems Department 36
Computer Science Faculty
Kabul University
INFORMATION SYSTEM COMPONENTS
Software
Software is perhaps the most difficult IS component to
secure.
The information technology industry reports warning of
holes, bugs, weaknesses, or other fundamental problems in
software.
Software programs become an easy target of accidental or
intentional attacks.
Saturday, January 02, 2021 Information Systems Department 37
Computer Science Faculty
Kabul University
INFORMATION SYSTEM COMPONENTS
Hardware
Hardware is the physical technology that houses and
executes the software, stores and transports the data,
and provides interfaces.
Physical security policies deal with hardware as a
physical asset and with the protection of physical assets
from harm or theft.
Saturday, January 02, 2021 Information Systems Department 38
Computer Science Faculty
Kabul University
INFORMATION SYSTEM COMPONENTS
Data
Data stored, processed, and transmitted by a computer
system must be protected.
Data is often the most valuable asset and the main target of
intentional attacks.
Saturday, January 02, 2021 Information Systems Department 39
Computer Science Faculty
Kabul University
INFORMATION SYSTEM COMPONENTS
People
Though often ignored in computer security
considerations, people have always been a threat to
information security.
Saturday, January 02, 2021 Information Systems Department 40
Computer Science Faculty
Kabul University
INFORMATION SYSTEM COMPONENTS
Procedures
Another frequently overlooked component of an information
system is procedures.
Procedures are written instructions for accomplishing a
specific task.
When an unauthorized user obtains an organization’s
procedures, this poses a threat to the integrity of the
information.
Saturday, January 02, 2021 Information Systems Department 41
Computer Science Faculty
Kabul University
INFORMATION SYSTEM COMPONENTS
Networks
The IS component that need for increased computer and
information security is networking.
When information systems are connected to each other to form
local area networks (LANs), and these LANs are connected to
other networks such as the Internet, new security challenges
rapidly emerge.
Saturday, January 02, 2021 Information Systems Department 42
Computer Science Faculty
Kabul University
QUESTIONS
Saturday, January 02, 2021 Information Systems Department 43
Computer Science Faculty
Kabul University
You might also like
- CEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021From EverandCEH: Certified Ethical Hacker v11 : Exam Cram Notes - First Edition - 2021No ratings yet
- CONSUMER PRODUCTS AND RETAIL COMPANY A - ITGC Internal Audit ReportDocument44 pagesCONSUMER PRODUCTS AND RETAIL COMPANY A - ITGC Internal Audit ReportHimabindu Arigela100% (2)
- Ethical Hacking and Network DefenseDocument4 pagesEthical Hacking and Network DefenseCristian RamirezNo ratings yet
- 12-Standard Operating ProceduresDocument17 pages12-Standard Operating Proceduresterrinda67% (3)
- Database Security PDFDocument23 pagesDatabase Security PDFUmesh Hengaju0% (1)
- Chapter 2 Lecture01Document42 pagesChapter 2 Lecture01Tomas AgonaferNo ratings yet
- 22 136 1 PBDocument10 pages22 136 1 PBAndika NugrahaNo ratings yet
- A Machine Learning ProposalDocument5 pagesA Machine Learning ProposalFeddy Micheal FeddyNo ratings yet
- Arba Minch University Institute of Technology Faculty of Computing & Software EngineeringDocument65 pagesArba Minch University Institute of Technology Faculty of Computing & Software Engineeringjemu mamedNo ratings yet
- Database Security - Threats & Prevention: Business Intelligence Architect, Alpha Clinical Systems Inc., NJ, USADocument8 pagesDatabase Security - Threats & Prevention: Business Intelligence Architect, Alpha Clinical Systems Inc., NJ, USAMohammad Mizanur RahmanNo ratings yet
- Essiential Terminology: Elements of InfosecDocument3 pagesEssiential Terminology: Elements of InfosecDeandryn RussellNo ratings yet
- Machine Learning and Deep LearningDocument6 pagesMachine Learning and Deep Learningsatya sriNo ratings yet
- A Survey of Security Attacks Defenses and SecurityDocument9 pagesA Survey of Security Attacks Defenses and SecurityNikita NawleNo ratings yet
- 02 Information Assurance and SecurityDocument46 pages02 Information Assurance and SecurityPius VirtNo ratings yet
- Lecture 01 Computer VulnerabilitiesDocument37 pagesLecture 01 Computer VulnerabilitiesAndrew LiberationNo ratings yet
- Tech ReportDocument20 pagesTech ReportArunNo ratings yet
- Database Integrity & SecurityDocument31 pagesDatabase Integrity & Securitysirage zeynuNo ratings yet
- IDEA: Intrusion Detection Through Electromagnetic-Signal Analysis For Critical Embedded and Cyber-Physical SystemsDocument14 pagesIDEA: Intrusion Detection Through Electromagnetic-Signal Analysis For Critical Embedded and Cyber-Physical Systemsjohnjs8766No ratings yet
- AJCST Vol.8 No.2 April-June, 2019, Pp. 105-110Document6 pagesAJCST Vol.8 No.2 April-June, 2019, Pp. 105-110irin solomonNo ratings yet
- Chapter 1 - Computer Security ConceptsDocument20 pagesChapter 1 - Computer Security ConceptsPham Van LuongNo ratings yet
- A Security Model For Distributed Computing: November 2001Document8 pagesA Security Model For Distributed Computing: November 2001jyotiNo ratings yet
- Paper 16Document13 pagesPaper 16anushka chaubeyNo ratings yet
- Computer System Security (KNC 301) : Ver. No.: 1.1Document20 pagesComputer System Security (KNC 301) : Ver. No.: 1.1Ansh AroraNo ratings yet
- Chapter 1fundamental of Software SecurityDocument7 pagesChapter 1fundamental of Software SecurityhaileNo ratings yet
- IDS MachineLearningDocument9 pagesIDS MachineLearningLeón ValeriaNo ratings yet
- Cyber Security Basics For Industry (ITOT)Document7 pagesCyber Security Basics For Industry (ITOT)badrNo ratings yet
- Machine Learning Assisted Snort and Zeek in Detecting Ddos Attacks in Software Defined NetworkingDocument17 pagesMachine Learning Assisted Snort and Zeek in Detecting Ddos Attacks in Software Defined Networkingkawthar EsawiNo ratings yet
- Computer Security: Introduction: January 3, 2020Document24 pagesComputer Security: Introduction: January 3, 2020Rakesh MatamNo ratings yet
- Nota Kuliah 1Document6 pagesNota Kuliah 1joezanderNo ratings yet
- CCS113-Week-1-5 (Prelim)Document33 pagesCCS113-Week-1-5 (Prelim)Raincel EstebanNo ratings yet
- Electronics 12 04182Document17 pagesElectronics 12 04182XXX DedeNo ratings yet
- Materi - Presentasi - Kegiatan - Bimtek - Kesiapsiagaan - Teknis - PenangananDocument30 pagesMateri - Presentasi - Kegiatan - Bimtek - Kesiapsiagaan - Teknis - Penangananportal datanyaNo ratings yet
- Level of Defenses in Network Security-A Case Study of Geetanjali Institute of Technical Studies, DabokDocument6 pagesLevel of Defenses in Network Security-A Case Study of Geetanjali Institute of Technical Studies, DabokKunal SinghviNo ratings yet
- Guidelines On Maritime Cyber Risk Management 2022Document30 pagesGuidelines On Maritime Cyber Risk Management 2022Fernando pazNo ratings yet
- Software Vulnerabilities Banking ThreatsDocument6 pagesSoftware Vulnerabilities Banking ThreatsvivekNo ratings yet
- Course Outline NewDocument2 pagesCourse Outline NewsamuelNo ratings yet
- Deep Learning Network Anomaly-Based Intrusion Detection Ensemble For Predictive Intelligence To Curb Malicious Connections: An Empirical EvidenceDocument13 pagesDeep Learning Network Anomaly-Based Intrusion Detection Ensemble For Predictive Intelligence To Curb Malicious Connections: An Empirical EvidenceVelumani sNo ratings yet
- Risk Assessment For Industrial Control SystemsDocument15 pagesRisk Assessment For Industrial Control Systemsramesh subburajNo ratings yet
- An Investigation On Biometric Internet SecurityDocument10 pagesAn Investigation On Biometric Internet SecurityShiro KumaNo ratings yet
- Machine Learning For Intrusion Detection in Cyber Security: Applications, Challenges, and RecommendationsDocument24 pagesMachine Learning For Intrusion Detection in Cyber Security: Applications, Challenges, and RecommendationsINNOVATIVE COMPUTING REVIEWNo ratings yet
- Chapter 2 Fundamentals of Information Systems SecurityDocument50 pagesChapter 2 Fundamentals of Information Systems SecurityIbsa GemechuNo ratings yet
- Cyber Security Seminar ProjectDocument29 pagesCyber Security Seminar ProjectSolomon SeyoumNo ratings yet
- Cyber Security FinalDocument6 pagesCyber Security FinalDivyasriNo ratings yet
- Vulnerability Assessment of Cybersecurity For SCADA Systems Using Attack TreesDocument8 pagesVulnerability Assessment of Cybersecurity For SCADA Systems Using Attack TreeslerebiNo ratings yet
- Information Assurance and Security: Mangahas, Teresita S. Antonio, LilibethDocument72 pagesInformation Assurance and Security: Mangahas, Teresita S. Antonio, Lilibeth9gag HAHANo ratings yet
- Cyber Security - Iot: 4. Unauthorized Access or ControlDocument4 pagesCyber Security - Iot: 4. Unauthorized Access or ControlKhushal SinghNo ratings yet
- MCS-054 Block-4Document87 pagesMCS-054 Block-4Kamal TiwariNo ratings yet
- LepraDocument18 pagesLepraMiuki Kanade JhonsonNo ratings yet
- Computer Security Module@2022 - 23Document51 pagesComputer Security Module@2022 - 23senawagari07fNo ratings yet
- BC ProjectReport 9368 9400 9414Document11 pagesBC ProjectReport 9368 9400 9414aidenNo ratings yet
- Week 1 - Module 1Document53 pagesWeek 1 - Module 1lefanoy196zNo ratings yet
- ABB Process Automation Reference Architecture - Public Presentation June 2021 - 9AKK107992A4568Document31 pagesABB Process Automation Reference Architecture - Public Presentation June 2021 - 9AKK107992A4568Achraf ElectricNo ratings yet
- Network SecurityDocument54 pagesNetwork SecurityfiromsaNo ratings yet
- Introduction - Cont'd: Computer Network SecurityDocument36 pagesIntroduction - Cont'd: Computer Network SecurityTimo AlexNo ratings yet
- ASSIGNMENTDocument1 pageASSIGNMENTAbdiaziiz MuhumedNo ratings yet
- Activity AXE3 Computer Security Management SystemsDocument9 pagesActivity AXE3 Computer Security Management SystemsScribdTranslationsNo ratings yet
- FCoDS - W02 - Threats and AttacksDocument42 pagesFCoDS - W02 - Threats and AttacksTrần Lưu Hồng PhươngNo ratings yet
- ADB Chapter OneDocument48 pagesADB Chapter OneNathnael MesfinNo ratings yet
- Advanced OS PresentationDocument22 pagesAdvanced OS PresentationMd Zahid HossainNo ratings yet
- Intrusion Detection Techniques in Mobile NetworksDocument8 pagesIntrusion Detection Techniques in Mobile NetworksInternational Organization of Scientific Research (IOSR)No ratings yet
- Safe and Secure Cyber-Physical Systems and Internet-of-Things SystemsFrom EverandSafe and Secure Cyber-Physical Systems and Internet-of-Things SystemsNo ratings yet
- Adroid StorageDocument31 pagesAdroid StorageabdulsattarNo ratings yet
- Array01 PDFDocument13 pagesArray01 PDFabdulsattarNo ratings yet
- Android Layout: By: Ziaullah MomandDocument17 pagesAndroid Layout: By: Ziaullah MomandabdulsattarNo ratings yet
- Recommender Systems: An Overview: Robin Burke, Alexander Felfernig, Mehmet H. GökerDocument6 pagesRecommender Systems: An Overview: Robin Burke, Alexander Felfernig, Mehmet H. GökerabdulsattarNo ratings yet
- Online Book Recommendation System Using Collaborative FilteringDocument2 pagesOnline Book Recommendation System Using Collaborative FilteringabdulsattarNo ratings yet
- Online Book Recommendation System Using Collaborative Filtering (With Jaccard Similarity)Document9 pagesOnline Book Recommendation System Using Collaborative Filtering (With Jaccard Similarity)abdulsattarNo ratings yet
- Thesis/Final Project Registration Form: Student(s) Personal DetailsDocument3 pagesThesis/Final Project Registration Form: Student(s) Personal DetailsabdulsattarNo ratings yet
- Online Faculty Staff Directory For Multi University: Modules and Their DescriptionDocument3 pagesOnline Faculty Staff Directory For Multi University: Modules and Their DescriptionabdulsattarNo ratings yet
- DBMS Arch 99 2ndDocument121 pagesDBMS Arch 99 2ndabdulsattarNo ratings yet
- Software Requirements Specification For Online ShoppingDocument12 pagesSoftware Requirements Specification For Online ShoppingabdulsattarNo ratings yet
- Thesis/Final Project Registration Form: Student(s) Personal DetailsDocument3 pagesThesis/Final Project Registration Form: Student(s) Personal DetailsabdulsattarNo ratings yet
- Mtconnect Challenge: Machine Monitoring & Big DataDocument4 pagesMtconnect Challenge: Machine Monitoring & Big DataabdulsattarNo ratings yet
- Case Study On Kle HospitalDocument6 pagesCase Study On Kle HospitalStany D'melloNo ratings yet
- Epas Grade 8 Q3 Mod 3Document24 pagesEpas Grade 8 Q3 Mod 3villarosacatheeeNo ratings yet
- l1 - Connecting To The Lab Environment PDFDocument6 pagesl1 - Connecting To The Lab Environment PDFCarlos Enrique Cardenas UrreaNo ratings yet
- UserGuideGP2v2 (Spanish)Document63 pagesUserGuideGP2v2 (Spanish)Ricardo SegoviaNo ratings yet
- CISSP Summary V1.1Document25 pagesCISSP Summary V1.1marutidivekar50% (2)
- Active Directory Replication TroubleshooterDocument37 pagesActive Directory Replication TroubleshooterontherigNo ratings yet
- Creating Password Protected Zip Files Under LinuxDocument1 pageCreating Password Protected Zip Files Under LinuxKartuun X.No ratings yet
- Istartek VT600 Vehicle Tracker USER MANUALDocument22 pagesIstartek VT600 Vehicle Tracker USER MANUALIstartek Vehicle Gps TrackerNo ratings yet
- Web Attack Cheat SheetDocument42 pagesWeb Attack Cheat Sheetsetyahangga3No ratings yet
- ST-IIIB User ManualDocument46 pagesST-IIIB User ManualderbalijalelNo ratings yet
- PC Advisor - June 2014 UKDocument148 pagesPC Advisor - June 2014 UKrakyatmarhaenNo ratings yet
- AGNI Energy Inc IP Theft Conspiracy Lawsuit Amended Answer and Counter by DeLeeuw DocumentDocument71 pagesAGNI Energy Inc IP Theft Conspiracy Lawsuit Amended Answer and Counter by DeLeeuw DocumentTruthLawFndNo ratings yet
- ALL MTK USB Driver 2013 - by GSM HOQUE - GSM-Forum PDFDocument8 pagesALL MTK USB Driver 2013 - by GSM HOQUE - GSM-Forum PDFManuDiazNo ratings yet
- OWK Modernization Supplier User Manual Oct 2020 Ver 1-0Document153 pagesOWK Modernization Supplier User Manual Oct 2020 Ver 1-0Gerente IngenieriaNo ratings yet
- SF PLT SF-IAS Integration Admin enDocument110 pagesSF PLT SF-IAS Integration Admin enmopachameNo ratings yet
- Inbound 6131335985266360711Document17 pagesInbound 6131335985266360711Dgham wajdiNo ratings yet
- KMCH Annual Report 2017 18Document232 pagesKMCH Annual Report 2017 18selvaprpcNo ratings yet
- TDS Recon. Getting StartedDocument32 pagesTDS Recon. Getting StartedGcmarshall82No ratings yet
- Issuance of Personal Customs Code FAQ For ForeignerDocument15 pagesIssuance of Personal Customs Code FAQ For ForeignerHassan AsgharNo ratings yet
- CHAPTER 1: Introduction To Information and Communications Technology (ICT)Document18 pagesCHAPTER 1: Introduction To Information and Communications Technology (ICT)Karyll EreneaNo ratings yet
- D800017X062 (OperatorBasic)Document40 pagesD800017X062 (OperatorBasic)azkharNo ratings yet
- Oracle Database 12c: Administration Workshop Student Guide Volume 2 D78846GC10 - sg2Document374 pagesOracle Database 12c: Administration Workshop Student Guide Volume 2 D78846GC10 - sg2Nelson NelsonNo ratings yet
- Online Textbooks PDFDocument3 pagesOnline Textbooks PDFAnne SebastianNo ratings yet
- User Manual (E-Tendering) : Online Tender Management ModuleDocument49 pagesUser Manual (E-Tendering) : Online Tender Management ModuleShubham KhandelwalNo ratings yet
- VAMP 260: Power Monitoring UnitDocument156 pagesVAMP 260: Power Monitoring UnitAli HassanNo ratings yet
- 4d Ch2 Data Collector QSG (Ed5) 2 - 1Document7 pages4d Ch2 Data Collector QSG (Ed5) 2 - 1Eliseo García RamírezNo ratings yet
- Neos Epabx 3s - Usermanual PDFDocument41 pagesNeos Epabx 3s - Usermanual PDFJEETENDRANo ratings yet
- Rotar Plus 30 STC - 00 - GBDocument16 pagesRotar Plus 30 STC - 00 - GBsebastianNo ratings yet