Professional Documents
Culture Documents
Firewalls: (Tool For Information
Firewalls: (Tool For Information
Uploaded by
dhruvvinayak100%(1)100% found this document useful (1 vote)
16 views24 pagesThis document discusses firewalls as a tool for information security. It defines a firewall as a barrier placed between a trusted and untrusted network that controls and monitors network traffic by imposing restrictions based on rules set by the network administrator. It then describes four main types of firewalls: packet filtering firewalls, circuit level gateways, application level gateways, and stateful multilayer inspection firewalls. Packet filtering firewalls inspect individual packets for allowed source/destination addresses and ports, while circuit level gateways monitor entire TCP sessions. Application level gateways act as a proxy for all network traffic. Stateful multilayer inspection firewalls provide the strongest security by deeply inspecting traffic at multiple levels.
Original Description:
Original Title
FIREWALLS
Copyright
© Attribution Non-Commercial (BY-NC)
Available Formats
PPT, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document discusses firewalls as a tool for information security. It defines a firewall as a barrier placed between a trusted and untrusted network that controls and monitors network traffic by imposing restrictions based on rules set by the network administrator. It then describes four main types of firewalls: packet filtering firewalls, circuit level gateways, application level gateways, and stateful multilayer inspection firewalls. Packet filtering firewalls inspect individual packets for allowed source/destination addresses and ports, while circuit level gateways monitor entire TCP sessions. Application level gateways act as a proxy for all network traffic. Stateful multilayer inspection firewalls provide the strongest security by deeply inspecting traffic at multiple levels.
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PPT, PDF, TXT or read online from Scribd
Download as ppt, pdf, or txt
100%(1)100% found this document useful (1 vote)
16 views24 pagesFirewalls: (Tool For Information
Firewalls: (Tool For Information
Uploaded by
dhruvvinayakThis document discusses firewalls as a tool for information security. It defines a firewall as a barrier placed between a trusted and untrusted network that controls and monitors network traffic by imposing restrictions based on rules set by the network administrator. It then describes four main types of firewalls: packet filtering firewalls, circuit level gateways, application level gateways, and stateful multilayer inspection firewalls. Packet filtering firewalls inspect individual packets for allowed source/destination addresses and ports, while circuit level gateways monitor entire TCP sessions. Application level gateways act as a proxy for all network traffic. Stateful multilayer inspection firewalls provide the strongest security by deeply inspecting traffic at multiple levels.
Copyright:
Attribution Non-Commercial (BY-NC)
Available Formats
Download as PPT, PDF, TXT or read online from Scribd
Download as ppt, pdf, or txt
You are on page 1of 24
FIREWALLS
[TOOL FOR INFORMATION
SECURITY]
OUTLINE
What is a Firewall..??
Firewall Design Principles
Firewall characteristics
Firewall Types
Configurations
Illustration of a Firewall
What is a Firewall..???
A firewall is a “choke point/guard box” of controlling and
monitoring the network traffic.
It is a barrier placed between a trusted and an untrusted
network.
It imposes restrictions on network services.
Using rules set up by the Network Administrator, the
firewall either permits or denies access.
A firewall will also gather evidence of attacks,
potentially allowing an organization to pursue legal
action.
Firewall..
An effective means of protecting a local system
or network of systems from network-based
security threats.
Firewall Example
FIREWALL DESIGN PRINCIPLES
Firewall Types
Firewall Types
Packet Filtering Firewalls
Circuit Level Gateways
Application Level Gateways
Stateful Multilayer Inspection
Firewalls
Firewall Types
Receive, inspect, and make decisions about all incoming
packets before they reach the protected parts of a
network.
1. Packet filters
A packet is a small file that contains the
following:
the data, acknowledgment, request or
command from the originating system;
the source IP address and port;
the destination IP address and port;
information about the “protocol” by which
the packet is to be handled;
information for detecting errors;
information on the type and status of the
data being sent; and….
Packet filtering takes place at the lowest layer
in the hierarchy of network processes. It
allows, or disallows, packets based on their:
source IP address;
destination port number;
Protocol;
Packet Filters diagram1
Packet Filters diagram2
Circuit Level Gateways (or Circuit
Relays)
monitor TCP handshaking between packets to determine whether a
requested session is legitimate.
Information passed to a remote computer through a circuit level
gateway appears to have originated from the gateway.
useful for hiding information about protected networks.
Circuit level gateways are relatively inexpensive and have the
advantage of hiding information about the private network they
protect. On the other hand, they do not filter individual packets.
The firewall then checks to see if the sending host has permission to
send to the destination, and that the receiving host has permission to
receive from the sender.
Circuit Level Gateways diagram1
Circuit Level Gateways diagram2
Application Gateways
Application level gateways or proxy firewalls are
software applications with two primary modes.
This method ensures that all incoming
connections are always made with the proxy
client, while outgoing connections are always
made with the proxy server.
Application Gateways diagram1
Application Gateways diagram2
Stateful Multilayer Inspection
Firewalls
Stateful multilayer inspection firewalls provide the best
security of the four firewall types by monitoring the
data being communicated at application socket or port
layer as well as the protocol and address level to verify
that the request is functioning as expected.
Firewall would not permit changes, the connection
will discontinue.
Stateful inspection systems can dynamically open and
close ports for each session
Stateful Multilayer Inspection
diagram
Firewall Limitations:
The firewall cannot protect against attacks that bypass
the firewall
The firewall does not protect against internal threats,
such as a disgruntled employee or an employee who
unwittingly cooperates with an external attacker.
The firewall cannot protect against the transfer of
virus-infected programs or files.
Finally, firewalls do not run themselves; they need to
be actively managed.
Conclusion
One of the best things about a firewall from a
security standpoint is that it stops anyone on
the outside from logging onto a computer in
your private network.
While this is a big deal for businesses, most
home networks will probably not be threatened
in this manner. Still, putting a firewall in place
provides some peace of mind.
THANK YOU
You might also like
- (SA22-7683-12) (V1R10) zOS - Security Server RACF Security Administrator's GuideDocument848 pages(SA22-7683-12) (V1R10) zOS - Security Server RACF Security Administrator's GuideJosé Antonio Osorio RodríguezNo ratings yet
- Redbook - IBM Personal Communications and IBM zOS TTLS Enablement - Technical Enablement SeriesDocument42 pagesRedbook - IBM Personal Communications and IBM zOS TTLS Enablement - Technical Enablement Seriesgborja8881331No ratings yet
- Network Security: Lecturer: Guled Yusuf MihileDocument38 pagesNetwork Security: Lecturer: Guled Yusuf MihileOsmanicNo ratings yet
- Firewall & It's TypesDocument10 pagesFirewall & It's TypesArslan Kamran JuttNo ratings yet
- On Firewall ReportDocument12 pagesOn Firewall ReportPrincess Yashika0% (1)
- Firewall 86 SlidesDocument86 pagesFirewall 86 SlidesHarneet Singh ChuggaNo ratings yet
- What Is A Firewall?: Network-Level FirewallsDocument3 pagesWhat Is A Firewall?: Network-Level Firewallsgaurav sharmaNo ratings yet
- 5 PowerShell RemotingDocument5 pages5 PowerShell RemotingĐình HoàngNo ratings yet
- Infoprint Pro C900afp PDFDocument418 pagesInfoprint Pro C900afp PDFSunny SaahilNo ratings yet
- RACFDocument55 pagesRACFpablo romeoNo ratings yet
- Hercules - Installation Guide: Hercules System/370, ESA/390, Z/architecture EmulatorDocument127 pagesHercules - Installation Guide: Hercules System/370, ESA/390, Z/architecture EmulatorAbhay Mishra100% (1)
- Zos JCL Advanced v3 PDFDocument2 pagesZos JCL Advanced v3 PDFLakshmi NarayanaNo ratings yet
- Assembler Input-Output Files PDFDocument10 pagesAssembler Input-Output Files PDFrhinowar99No ratings yet
- Deployment Guide Series IBM Tivoli Application Dependency Discovery Manager V7.1 Sg247616Document472 pagesDeployment Guide Series IBM Tivoli Application Dependency Discovery Manager V7.1 Sg247616bupbechanhNo ratings yet
- Advantage CA-Easytrieve Plus Report Generator: User GuideDocument169 pagesAdvantage CA-Easytrieve Plus Report Generator: User Guideapi-3760779No ratings yet
- Administration ReferenceDocument616 pagesAdministration ReferenceanonNo ratings yet
- Easytrieve Substr Function MacroDocument3 pagesEasytrieve Substr Function MacromukeshNo ratings yet
- QMFDocument63 pagesQMFskh_1987100% (1)
- RACF V1.10 Command Syntax BookletDocument68 pagesRACF V1.10 Command Syntax Booklets4l4d3No ratings yet
- IBM Printer and PrintingDocument254 pagesIBM Printer and PrintingadnanbwNo ratings yet
- DSL Network ArchitecturesDocument16 pagesDSL Network Architecturesdeetz13No ratings yet
- Restructured Executor Extended Language Is A Highly Versatile ProgrammingDocument13 pagesRestructured Executor Extended Language Is A Highly Versatile ProgrammingPrasenjit ChatterjeeNo ratings yet
- Hibernate Reference3.2Document232 pagesHibernate Reference3.2vextor80No ratings yet
- Introduction To REXXDocument9 pagesIntroduction To REXXFauzanAkhyarNo ratings yet
- Customization GuideDocument222 pagesCustomization GuideanonNo ratings yet
- Displaying and Changing Command PropertiesDocument13 pagesDisplaying and Changing Command PropertiesENDLURI DEEPAK KUMARNo ratings yet
- Ispf Dialog Tag Language Guide and ReferenceDocument562 pagesIspf Dialog Tag Language Guide and Referenceapi-3736472No ratings yet
- SOC-security Operations CenterDocument43 pagesSOC-security Operations CenterMhmd FnnNo ratings yet
- CL19Document9 pagesCL19ENDLURI DEEPAK KUMARNo ratings yet
- Types of FirewallDocument10 pagesTypes of FirewallsanjeevNo ratings yet
- z114 System OverviewDocument198 pagesz114 System OverviewEdith Velázquez GómezNo ratings yet
- Cobol User's GuideDocument360 pagesCobol User's GuidePreethi CoolNo ratings yet
- IBM Content Manager OnDemand and FileNet-4Document88 pagesIBM Content Manager OnDemand and FileNet-4David ResendizNo ratings yet
- Admin GuideDocument560 pagesAdmin GuideRaul PaezNo ratings yet
- HCL's Mainframe Services - System Administration On Z/VM and Z/Linux - Hands-OnDocument57 pagesHCL's Mainframe Services - System Administration On Z/VM and Z/Linux - Hands-OnMIhir Ranjan DasNo ratings yet
- IBM Global Services - Training Center - Hortolândia: Communications Server: Concepts - TCP/IP For Mainframe and SNADocument44 pagesIBM Global Services - Training Center - Hortolândia: Communications Server: Concepts - TCP/IP For Mainframe and SNADie001100% (2)
- IPSECDocument23 pagesIPSECAkhilendraNo ratings yet
- ISPF User's Guide Volume I PDFDocument260 pagesISPF User's Guide Volume I PDFDenazareth JesusNo ratings yet
- Get-Eventlog Get-Process Start-Process Stop-Process Get-ACL Set-ACL Restart-Computer Stop-ComputerDocument4 pagesGet-Eventlog Get-Process Start-Process Stop-Process Get-ACL Set-ACL Restart-Computer Stop-Computerabdul shahidNo ratings yet
- CA7 33 DBMaintDocument418 pagesCA7 33 DBMaintTerence Swartz-GlancyNo ratings yet
- 1 - Definitions & Challenges of Security, Attacks & ServicesDocument31 pages1 - Definitions & Challenges of Security, Attacks & ServicesNilaa RaghunathanNo ratings yet
- Tuning Linux OS On Ibm Sg247338Document494 pagesTuning Linux OS On Ibm Sg247338gabjonesNo ratings yet
- HMC SecurityDocument20 pagesHMC Securityi14065No ratings yet
- Chapter07 Batch and JES SlidesDocument27 pagesChapter07 Batch and JES SlidesSteve Petersen100% (1)
- Network CommandsDocument67 pagesNetwork CommandsPriya KansalNo ratings yet
- CA 7 HandbookDocument418 pagesCA 7 HandbookIvo Veselinov DimitrovNo ratings yet
- PDF Printing Using InfoPrint ServerDocument16 pagesPDF Printing Using InfoPrint ServerBishnujit BanerjeeNo ratings yet
- 04 Z OS REXX Scripting Advanced CH01Document33 pages04 Z OS REXX Scripting Advanced CH01fasfgasNo ratings yet
- DEFCON 23 Bart Kulach Hack The Legacy IBMi Revealed PDFDocument20 pagesDEFCON 23 Bart Kulach Hack The Legacy IBMi Revealed PDFyalokeraNo ratings yet
- RACF2 Ichza2c0Document442 pagesRACF2 Ichza2c0Siranjeevi Mohanaraja100% (1)
- Zosmf User ExpDocument64 pagesZosmf User ExpniharapatilNo ratings yet
- week13-FIREWALL IPTABLESDocument54 pagesweek13-FIREWALL IPTABLESПашаNo ratings yet
- Rexx/Vm User's Guide: 5 Release 2Document235 pagesRexx/Vm User's Guide: 5 Release 2prakasavi100% (1)
- Power Handling PDFDocument32 pagesPower Handling PDFBhasker ReddyNo ratings yet
- IP Telephony: Deploying VoIP Protocols and IMS InfrastructureFrom EverandIP Telephony: Deploying VoIP Protocols and IMS InfrastructureNo ratings yet
- WAN TECHNOLOGY FRAME-RELAY: An Expert's Handbook of Navigating Frame Relay NetworksFrom EverandWAN TECHNOLOGY FRAME-RELAY: An Expert's Handbook of Navigating Frame Relay NetworksNo ratings yet
- COL100 Assignment 2Document4 pagesCOL100 Assignment 2ManikyaMayankNo ratings yet
- Datasheet Optris CX LTDocument2 pagesDatasheet Optris CX LTMahmoud Abd ElhamidNo ratings yet
- HCIA-Datacom V1.0 Lab GuideDocument181 pagesHCIA-Datacom V1.0 Lab GuideMoulaye KoureichNo ratings yet
- Fundamentals of ML - Pre Quiz - Attempt ReviewDocument4 pagesFundamentals of ML - Pre Quiz - Attempt Reviewvinay MurakambattuNo ratings yet
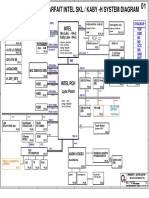
- Power Pavilion Parfait Intel SKL / Kaby - H System DiagramDocument51 pagesPower Pavilion Parfait Intel SKL / Kaby - H System Diagramcompu centerNo ratings yet
- Lecture1-Microprocessors, Microcontroller Assembly LanguageDocument59 pagesLecture1-Microprocessors, Microcontroller Assembly LanguageSaurabh BhiseNo ratings yet
- 24.2 CAD System Hardware: Output Devices Digital Computer Secondary StorageDocument7 pages24.2 CAD System Hardware: Output Devices Digital Computer Secondary StorageAlberto OreaNo ratings yet
- Veeam Rental Licensing Usage Reporting GuideDocument49 pagesVeeam Rental Licensing Usage Reporting Guideaylbul123No ratings yet
- Acc 242amDocument101 pagesAcc 242amLéptons Wine TechNo ratings yet
- Yuzu Installer2Document2 pagesYuzu Installer2Alexander GaticaNo ratings yet
- Syllabus TMC 102Document1 pageSyllabus TMC 102Harsh JainNo ratings yet
- Ramirez Farkle SpecDocument3 pagesRamirez Farkle Specapi-526462626No ratings yet
- Panw 5 Best IoT Security SolutionsDocument16 pagesPanw 5 Best IoT Security Solutionsw.meloNo ratings yet
- PracDocument18 pagesPracAyush KumarNo ratings yet
- Module1 UPDDocument72 pagesModule1 UPDZhanzhi LiuNo ratings yet
- ProspectousDocument62 pagesProspectousSimarjeet MattuNo ratings yet
- 02 ARM Processor FundamentalsDocument65 pages02 ARM Processor Fundamentalsbengaltiger100% (2)
- 700-0179 Rev SDocument62 pages700-0179 Rev SrijuvanaeroNo ratings yet
- XVL Product Silent Installation Manual: For Product Support, Please Contact Your Sales AgentDocument12 pagesXVL Product Silent Installation Manual: For Product Support, Please Contact Your Sales AgentKAUR DISPARIPORANo ratings yet
- Smalltalk Programming Language: Modified By: Richelle Joy A. ReyesDocument15 pagesSmalltalk Programming Language: Modified By: Richelle Joy A. ReyesRichelle AlanoNo ratings yet
- Blockchain For IoT (9826)Document13 pagesBlockchain For IoT (9826)Blather skiteNo ratings yet
- Et200sp Di 8xnamur HF Manual en-US en-USDocument37 pagesEt200sp Di 8xnamur HF Manual en-US en-USSaravana Kumar JNo ratings yet
- Int To CS and ProgrammingDocument7 pagesInt To CS and ProgrammingHenok ZerihunNo ratings yet
- Ec8551 Communication NetworksDocument53 pagesEc8551 Communication NetworksShamia SathishNo ratings yet
- Ubuntu Mate Desktop Uninstall & Re InstallDocument6 pagesUbuntu Mate Desktop Uninstall & Re InstallVelan ChandrasekarNo ratings yet
- String Matching With Finite Automata: Submitted To: Mam Maimoona Submitted By: Iqra Munir Anmol HamidDocument58 pagesString Matching With Finite Automata: Submitted To: Mam Maimoona Submitted By: Iqra Munir Anmol HamidAnmol HamidNo ratings yet
- Assignment-1 Q-1 Write A Short Note On Operating System? Ans: DefinitionDocument5 pagesAssignment-1 Q-1 Write A Short Note On Operating System? Ans: DefinitionParth ChavhanNo ratings yet
- Midterm Study Sheet For CS3719 Regular Languages and Finite AutomataDocument4 pagesMidterm Study Sheet For CS3719 Regular Languages and Finite AutomataAmitesh AroraNo ratings yet
- CCNA Exploration 3 LAN Switching and Wireless - Chapter 5 ExamDocument6 pagesCCNA Exploration 3 LAN Switching and Wireless - Chapter 5 ExamcretufiNo ratings yet
- Resume VisAIDocument1 pageResume VisAITechnetNo ratings yet