Professional Documents
Culture Documents
EE Fin 7 - Final
EE Fin 7 - Final
Uploaded by
sadia santa0 ratings0% found this document useful (0 votes)
15 views17 pagesThis document discusses computer ethics and issues related to software. It covers four primary issues in computer ethics: privacy, accuracy, property, and access. It also discusses different types of software licenses including public domain, freeware, shareware, and all rights reserved. The document outlines computer crime such as software piracy, damage to systems, and theft. It concludes with discussing measures to protect computer security such as restricting access, backups, anti-virus software and hiring practices.
Original Description:
Original Title
EE Fin 7_final
Copyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThis document discusses computer ethics and issues related to software. It covers four primary issues in computer ethics: privacy, accuracy, property, and access. It also discusses different types of software licenses including public domain, freeware, shareware, and all rights reserved. The document outlines computer crime such as software piracy, damage to systems, and theft. It concludes with discussing measures to protect computer security such as restricting access, backups, anti-virus software and hiring practices.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
0 ratings0% found this document useful (0 votes)
15 views17 pagesEE Fin 7 - Final
EE Fin 7 - Final
Uploaded by
sadia santaThis document discusses computer ethics and issues related to software. It covers four primary issues in computer ethics: privacy, accuracy, property, and access. It also discusses different types of software licenses including public domain, freeware, shareware, and all rights reserved. The document outlines computer crime such as software piracy, damage to systems, and theft. It concludes with discussing measures to protect computer security such as restricting access, backups, anti-virus software and hiring practices.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
You are on page 1of 17
Engineering Ethics
Lecture 7
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /1
Computer Ethics
• Computers are involved to some extent in
almost every aspect of our lives
– They often perform life-critical tasks
• Therefore, we need to carefully consider the
issues of ethics
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /2
Computer Ethics
• Computer ethics are morally acceptable use of
computers
– i.e. using computers appropriately
• Standards or guidelines are important in this
industry, because technology changes are
outstripping the legal system’s ability to keep
up
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /3
Computer Ethics
Computers have become the technological backbone of society.
Computers raise a host of difficult moral issues, many of them connected with
basic moral concerns such as free speech, privacy, respect for property,
informed consent, and harm.
The Internet has magnified all issues in computer ethics.
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /4
Computer Ethics
• Four primary issues
– Privacy – responsibility to protect data about
individuals
– Accuracy - responsibility of data collectors to
authenticate information and ensure its accuracy
– Property - who owns information and software and
how can they be sold and exchanged
– Access - responsibility of data collectors to control
access and determine what information a person
has the right to obtain about others and how the
information can be used
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /5
Data and Software
Computer hardware is protected by patent laws.
Software can be protected by trade secret laws or by copyrights.
Trade secret laws permit employers to require their employees not to tell
owner information.
Obviously, trade secrets are useless once software is made publicly available
as a marketed product. Here copyright laws offer the best protection.
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /6
Copyright Laws
Software developers (or the companies they
work for) own their programs.
Software buyers only own the right to use the
software according to the license agreement.
No copying, reselling, lending, renting, leasing,
or distributing is legal without the software
owner’s permission.
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /7
Software Licenses
There are four types of software licenses:
Public Domain
Freeware
Shareware
All Rights Reserved
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /8
Public Domain License
Public domain software has no owner and is
not protected by copyright law.
It was either created with public funds, or the
ownership was forfeited by the creator.
Can be copied, sold, and/or modified
Often is of poor quality/unreliable
• ELIZA (1966), FFTPACK (1985)
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /9
Freeware License
Freeware is copyrighted software that is
licensed to be copied and distributed without
charge.
Freeware is free, but it’s still under the owner’s
control.
Examples:
Windows
Mozilla
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /10
Shareware License
• A shareware software license allows you to use
the software for a trial period, but you must pay a
registration fee to the owner for permanent use.
– Some shareware trials expire on a certain date
– Payment depends on the honor system
• Purchasing (the right to use) the software may
also get you a version with more powerful
features and published documentation.
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /11
All Rights Reserved License
May be used by the purchaser according
the exact details spelled out in the license
agreement.
You can’t legally use it--or even possess it--
without the owner’s permission.
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /12
Software Piracy
SPA (Software Publishers Association) polices
software piracy and mainly targets:
Illegal duplication
Sale of copyrighted software
Companies that purchase single copies and load
the software on multiple computers or networks
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /13
Computer Crime
• Computer criminals -using a computer to
commit an illegal act
• Who are computer criminals?
– Employees – disgruntled or dishonest --the
largest category
– Outside users - customers or suppliers
– “Hackers” and “crackers” - hackers do it “for fun”
but crackers have malicious intent
– Organized crime - tracking illegal enterprises,
forgery, counterfeiting
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /14
Types of Computer Crime
• Damage to computers, programs or files
– Viruses - migrate through systems attached to
files and programs
– Worms - continuously self-replicate
• Theft
– Of hardware, software, data, computer time
– unauthorized copies of copyrighted material
• View/Manipulation
– “Unauthorized entry” and “harmless message”
still illegal
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /15
Computer Security
• Computer security involves protecting:
– information, hardware and software
– from unauthorized use and damage and
– from sabotage and natural disasters
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /16
Measures to Protect Computer Security
• Restricting access both to the hardware locations
(physical access) and into the system itself (over the
network) using firewalls
• Changing passwords frequently
• Making backup copies
• Using anti-virus software
• Hiring trustworthy employees
AIUB Dr M Tanseer Ali Eng Ethics Lec 7 /17
You might also like
- Aerodynamics For EngineersDocument53 pagesAerodynamics For Engineerssgatus100% (3)
- EE Fin 7 - FinalDocument17 pagesEE Fin 7 - Finalsadia santaNo ratings yet
- Engineering Ethics: Aiub DR M Tanseer Ali Eng Ethics Lec 7 /1Document30 pagesEngineering Ethics: Aiub DR M Tanseer Ali Eng Ethics Lec 7 /1World StationNo ratings yet
- 1.7 Ethics & OwnershipDocument7 pages1.7 Ethics & OwnershipPrince FaNo ratings yet
- Ethics & OwnershipDocument19 pagesEthics & OwnershipRajesh TivrekarNo ratings yet
- Computer EthicsDocument31 pagesComputer EthicsAnsh LodhaNo ratings yet
- Computer EthicsDocument37 pagesComputer EthicsMichael Jordan AdrianoNo ratings yet
- Computing and Ethics: by B.S.srimathyDocument20 pagesComputing and Ethics: by B.S.srimathyB.S.AthishNo ratings yet
- Computer Ethics, Privacy and SecurityDocument38 pagesComputer Ethics, Privacy and SecurityDevansh GoelNo ratings yet
- Computer Ethics, Privacy and Security: Vilchor G. PerdidoDocument38 pagesComputer Ethics, Privacy and Security: Vilchor G. PerdidoMary Joy BernasolNo ratings yet
- Chap 011Document70 pagesChap 011Princess Arasnav MNo ratings yet
- Cyber EthicsDocument41 pagesCyber EthicsEmma Warne100% (1)
- Use of ComputersDocument33 pagesUse of ComputersF.Ramesh DhanaseelanNo ratings yet
- Grade 10 Unit 3Document23 pagesGrade 10 Unit 3ahlam100% (1)
- EthicalLegalUseofTechno EdTechDocument23 pagesEthicalLegalUseofTechno EdTechPearly LucesNo ratings yet
- Ethics Lect1 IntroductionDocument11 pagesEthics Lect1 Introductionomarnader16No ratings yet
- Computer and Internet Ethics and CrimesDocument9 pagesComputer and Internet Ethics and Crimesmark anthony sorianoNo ratings yet
- Chapter 11 - Society, Law and Ethics: Ethical IssuesDocument17 pagesChapter 11 - Society, Law and Ethics: Ethical IssuesVishal SinghNo ratings yet
- Cyber Law and EthicsDocument50 pagesCyber Law and EthicsVanshita PathareNo ratings yet
- PED 411.lesson 8Document33 pagesPED 411.lesson 8Mary Cres Deguma OtazaNo ratings yet
- EthicsDocument2 pagesEthicsdavieNo ratings yet
- Management Information System: Unit-7: Management Challenges - Security, Ethical and Societal ChallengesDocument40 pagesManagement Information System: Unit-7: Management Challenges - Security, Ethical and Societal ChallengesVidhi MaheshwariNo ratings yet
- Dinesh A Unit 3Document13 pagesDinesh A Unit 3DineshNo ratings yet
- Computer UseDocument8 pagesComputer UseAbdul-Muizz Yussif Adu AdamNo ratings yet
- Society Law and EthicsDocument45 pagesSociety Law and Ethicssagar salalNo ratings yet
- Case Study - Should I Copy Software?Document6 pagesCase Study - Should I Copy Software?Mikee TamonanNo ratings yet
- CS 1B Lecture 3 1Document14 pagesCS 1B Lecture 3 1Val PaladoNo ratings yet
- Lecture4 - IELegal IssuesDocument28 pagesLecture4 - IELegal IssuesAnurag KumarNo ratings yet
- Society Law and Ethics NotesDocument12 pagesSociety Law and Ethics NotesTanishka100% (1)
- Summary Chapter 6 ComEthicsDocument7 pagesSummary Chapter 6 ComEthicsmohamedabdulkadir767No ratings yet
- Software Engineering Code of EthicsDocument33 pagesSoftware Engineering Code of EthicsShafiq Ul UmarNo ratings yet
- EthicsDocument16 pagesEthicsatitnepal.thsNo ratings yet
- ComputersDocument22 pagesComputersJhaye BautistaNo ratings yet
- 6 Computer EthicsDocument9 pages6 Computer EthicsTooba AkhtarNo ratings yet
- Cyber EthicsDocument3 pagesCyber EthicsAgastya AbhishekNo ratings yet
- Software PiracyDocument67 pagesSoftware PiracyShivendra Singh100% (1)
- A Level CS CH 10 9618Document6 pagesA Level CS CH 10 9618calvin esauNo ratings yet
- SDD HSC NotesDocument29 pagesSDD HSC NotesHarrison HuNo ratings yet
- Sub-Strand 3: Information Security Data ThreatDocument4 pagesSub-Strand 3: Information Security Data Threatsamuel dogbeyNo ratings yet
- Legal & Ethical Technology: SchoolDocument37 pagesLegal & Ethical Technology: SchoolChristian EarlNo ratings yet
- Computer EthicsDocument20 pagesComputer EthicsAmir SaeedNo ratings yet
- Educ Tech 2 Chapter 8Document2 pagesEduc Tech 2 Chapter 8SerryAlbercaNo ratings yet
- Chapter 1 EXDocument3 pagesChapter 1 EXhosam hasanNo ratings yet
- Cyber EthicsDocument6 pagesCyber Ethicsdharap0311No ratings yet
- Business Plug-In B4 Enterprise Architectures: Learning OutcomesDocument8 pagesBusiness Plug-In B4 Enterprise Architectures: Learning OutcomesThao TrungNo ratings yet
- Social ImpactsDocument23 pagesSocial ImpactsShubham KumarNo ratings yet
- Ethical Issues in Information TechnologyDocument3 pagesEthical Issues in Information Technologybysschearthur123No ratings yet
- Ch-17 - SOCIETY, LAW AND ETHICSDocument16 pagesCh-17 - SOCIETY, LAW AND ETHICSARJUN AGGARWALNo ratings yet
- Lec4 - IntellectualProperty IIDocument34 pagesLec4 - IntellectualProperty IIyyyNo ratings yet
- Open Source and Free SoftwareDocument5 pagesOpen Source and Free SoftwareaxlzekeNo ratings yet
- Module - 8 Security and Ethical ChallengesDocument62 pagesModule - 8 Security and Ethical Challengesfriendly4ualwaysNo ratings yet
- Ethical Issues in Computing and Information TechnologyDocument20 pagesEthical Issues in Computing and Information TechnologyJeysie ClarksonNo ratings yet
- Computer Ethics and Legal IssuesDocument19 pagesComputer Ethics and Legal IssuesKen Chai NgNo ratings yet
- Stvep Icf 9 q4 Las7-8 For-PrintingDocument10 pagesStvep Icf 9 q4 Las7-8 For-PrintingKhyzere GepanagaNo ratings yet
- Societal Impacts 1Document6 pagesSocietal Impacts 1lecifo3741No ratings yet
- Ict Competency LU8 Computer Security Privacy and EthicsDocument29 pagesIct Competency LU8 Computer Security Privacy and EthicsLi YuNo ratings yet
- Copyrights Q1UOj1gRzVclFFUyDocument8 pagesCopyrights Q1UOj1gRzVclFFUysaifdeenmofoloNo ratings yet
- Last Minute Revision For IP Exam - Societal ImpactsDocument4 pagesLast Minute Revision For IP Exam - Societal ImpactsWhiteNo ratings yet
- Protection of Property Rights in Computer SoftwareDocument4 pagesProtection of Property Rights in Computer SoftwareBruhNo ratings yet
- Hacking: 10 Easy Beginners Tutorials on How to Hack Plus Basic Security TipsFrom EverandHacking: 10 Easy Beginners Tutorials on How to Hack Plus Basic Security TipsNo ratings yet
- EE Fin 7 - FinalDocument17 pagesEE Fin 7 - Finalsadia santaNo ratings yet
- Engineering Ethics: Aiub DR M Tanseer Ai Eng Ethics Lec 5 /1Document7 pagesEngineering Ethics: Aiub DR M Tanseer Ai Eng Ethics Lec 5 /1sadia santaNo ratings yet
- Engineering Ethics: Aiub DR M Tanseer Ai Eng Ethics Lec 5 /1Document7 pagesEngineering Ethics: Aiub DR M Tanseer Ai Eng Ethics Lec 5 /1sadia santaNo ratings yet
- Lecture 8 - Combinational Circuit DesignDocument57 pagesLecture 8 - Combinational Circuit Designsadia santaNo ratings yet
- Lecture 7 - CMOS DC - Transient ResponseDocument40 pagesLecture 7 - CMOS DC - Transient Responsesadia santaNo ratings yet
- Lecture 4 - Implementing Logic in CMOSDocument32 pagesLecture 4 - Implementing Logic in CMOSsadia santaNo ratings yet
- Lecture 5 - CMOS Transistor TheoryDocument44 pagesLecture 5 - CMOS Transistor Theorysadia santaNo ratings yet
- Lecture 2 - CMOS FabricationDocument39 pagesLecture 2 - CMOS Fabricationsadia santaNo ratings yet
- The Heisman Trophy Trust v. Heisman WatchDocument20 pagesThe Heisman Trophy Trust v. Heisman WatchDarren Adam HeitnerNo ratings yet
- ManoDocument15 pagesManoraaziqNo ratings yet
- Barbecue Blues Melody - Lyrics - ChordsDocument1 pageBarbecue Blues Melody - Lyrics - Chordsc westonNo ratings yet
- Egyptian Arabic Primer IDocument109 pagesEgyptian Arabic Primer IgueushiNo ratings yet
- Devil Doesn't Bargain - C Minor - MN0260991Document6 pagesDevil Doesn't Bargain - C Minor - MN0260991gabeyelliotNo ratings yet
- ReadMe KMSpico PortableDocument4 pagesReadMe KMSpico PortableSyedNo ratings yet
- I B.tech 2016 Roll ListDocument147 pagesI B.tech 2016 Roll ListPhani PitchikaNo ratings yet
- Allotted Under Category Opening Rank Closing RankDocument6 pagesAllotted Under Category Opening Rank Closing RanknilayNo ratings yet
- C-4 Kernel 4 V 2 7 Final PDFDocument173 pagesC-4 Kernel 4 V 2 7 Final PDFMD Belal RashidNo ratings yet
- Eng Hira5 NaDocument1 pageEng Hira5 NaWolfgangRamírezNo ratings yet
- Project Title: Phase 1. AnalysisDocument8 pagesProject Title: Phase 1. Analysismahendar kagithalaNo ratings yet
- Iec 62305-3 2010 - Material and CorrosionDocument1 pageIec 62305-3 2010 - Material and CorrosionSandeep SinghNo ratings yet
- Calculus For Engineers Fourth Edition Instructors Solutions Manual PDFDocument1,104 pagesCalculus For Engineers Fourth Edition Instructors Solutions Manual PDFRalph AraujoNo ratings yet
- Avast Antivirus: See AlsoDocument2 pagesAvast Antivirus: See AlsoJay MesaNo ratings yet
- Kernelope Holdings v. DMD Prods. - ComplaintDocument17 pagesKernelope Holdings v. DMD Prods. - ComplaintSarah BursteinNo ratings yet
- Unit Testing Node - Js PDFDocument33 pagesUnit Testing Node - Js PDFRitesh Kumar100% (1)
- 09 Req480 06 Define SystemDocument32 pages09 Req480 06 Define SystemjoycmercadoNo ratings yet
- Filipino 6 TGDocument142 pagesFilipino 6 TGDiyonata Kortez88% (33)
- A Presentation On "Patent Drafting" by Ms. Vinita RadhakrishnanDocument75 pagesA Presentation On "Patent Drafting" by Ms. Vinita RadhakrishnanBrain League100% (2)
- Kate Bernheimer - Fairy Tale Review, The White Issue (2009)Document146 pagesKate Bernheimer - Fairy Tale Review, The White Issue (2009)Stacy HardyNo ratings yet
- Cabide Ui 5th Edition Plug in Installation and Whats New Guide v1 1 enDocument3 pagesCabide Ui 5th Edition Plug in Installation and Whats New Guide v1 1 enしんじ まもるNo ratings yet
- Industrial Training Form Harshit LastDocument1 pageIndustrial Training Form Harshit LastAshish GuptaNo ratings yet
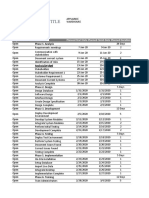
- Property Plant and Equipment Schedule TemplateDocument3 pagesProperty Plant and Equipment Schedule TemplateKabile MwitaNo ratings yet
- History of San Mateo County (1916)Document291 pagesHistory of San Mateo County (1916)peninsulastoryNo ratings yet
- Change The Product Key On Windows XPDocument4 pagesChange The Product Key On Windows XPIndrajit Banerjee100% (7)
- Prince V United LabDocument5 pagesPrince V United LabJVMNo ratings yet
- Instant Download Chemistry 8th Edition Zumdahl Test Bank PDF Full ChapterDocument10 pagesInstant Download Chemistry 8th Edition Zumdahl Test Bank PDF Full Chaptertortrixintonate6rmbc100% (12)
- Maintenance and Reengineering Project 1Document12 pagesMaintenance and Reengineering Project 1Mudabir TahiriNo ratings yet
- Class 10 Science Notes in Hindi Magnetic Effects of Electric CurrentDocument19 pagesClass 10 Science Notes in Hindi Magnetic Effects of Electric CurrentVinnie SinghNo ratings yet