Professional Documents
Culture Documents
Database Management System: MIS 520 - Database Theory Fall 2001 (Day)
Database Management System: MIS 520 - Database Theory Fall 2001 (Day)
Uploaded by
wani wani0 ratings0% found this document useful (0 votes)
4 views15 pagesOriginal Title
dbms
Copyright
© © All Rights Reserved
Available Formats
PPT, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
© All Rights Reserved
Available Formats
Download as PPT, PDF, TXT or read online from Scribd
Download as ppt, pdf, or txt
0 ratings0% found this document useful (0 votes)
4 views15 pagesDatabase Management System: MIS 520 - Database Theory Fall 2001 (Day)
Database Management System: MIS 520 - Database Theory Fall 2001 (Day)
Uploaded by
wani waniCopyright:
© All Rights Reserved
Available Formats
Download as PPT, PDF, TXT or read online from Scribd
Download as ppt, pdf, or txt
You are on page 1of 15
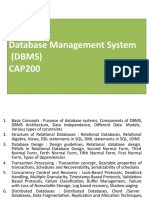
Database Management System
MIS 520 – Database Theory
Fall 2001 (Day)
Lecture 13
Database Management System
Database: A collection of related data. It should support
– Definition
– Construction
– Manipulation
Database Management System: A collection of programs
that enable the users to create and maintain a database.
Features of DBMS
1. Data storage, retrieval, and update: The ability to store, retrieve,
and update the data that are in the database.
2. User-accessible catalog: where descriptions of database
components are stored and are accessible to the users
3. Shared update support: A mechanism to ensure accuracy when
several users are updating the database at the same time
4. Backup and Recovery Services: Mechanisms for recovering the
database in the event that a database is damaged somehow.
5. Security Services: Mechanisms to ensure that certain rules are
followed with regard to data in the database and any changes that
are made in the data
Features of DBMS
5. Integrity services: Mechanisms to ensure that certain rules are
followed with regard to data in the database and any changes
that are made in the data.
6. Data Independence: Facilities to support the independence of
programs from the structure of the database.
7. Replication support: A facility to manage copies of the same
data at multiple locations.
8. Utility Services: DBMS provided services that assist in the
general maintenance of the database.
Shared Updates
• Multiple users are making updates to the database at
the same time.
Problem:
– Multiple people updating the database simultaneously can override
each other
Example:
– Agents T1 & T2 simultaneously read the seats reserved on Flight 890
i.e. 80
– T1 cancels 5 seats updating the seats reserved on Flight 890 to 75
– T2 reserves 4 additional seats on the flight and updates the seats
reserved on Flight 890 to 84.
– If T1 updates the database before T2. T2 will override T1’s change and
make reservations to 84 rather than getting the correct value of 79.
– Similarly if T2 updates before T1 the seats reserved will be 75
Shared Updates: Solution
• Batch Processing
– Allow multiple users to retrieve data simultaneously
– Updates are added to a batch file which does the
appropriate processing
– Does not work for real time situations
• Locking
– Restrict access to the record being updated by a user till
the transaction is complete.
Two Phase Lock
• Required when multiple records are updated as a
result of a user action (e.g. filling form etc.)
• All the records accessed are locked progressively till
the required updates are completed
– Growing Phase: More and more locks are added without
releasing locks
– After all locks are placed the database is updated
– Shrinking Phase: All locks are removed and no new ones
are added
Deadlock
• When two transactions require a common set
of records.
• Both of them are in growing phase and each
locks some of the records
• None of the records are released and they wait
for each other to release the locked records
They will wait forever!!!
Breaking Deadlock
Facilities
• Programs can lock entire tables or an individual row
• Programs can release any or all of the locks they currently hold
• Programs can inquire whether a given row or table is locked
Rules
• If more than one row is required then the entire table must be
locked
• Limit the amount of wait for a lock to be released beyond
which a transaction is aborted
• A well designed transaction should lock all the rows and tables
before starting the transaction
• Users should release locks as soon as possible to improve the
efficiency of the database
Security
• Protection against unauthorized access: either
intentional or accidental.
• Three main features for protection
– Passwords: Allows only authorized users to
access the database. Access privileges can be
provided based on access needs
– Encryption: Encodes data to non-decipherable.
Data decoded on demand to prevent hackers from
accessing data
– Views: Different snapshot of the data ensures that
users only get access to data they need
Integrity
• Integrity Constraints are the conditions that data
must satisfy during initial input & updates.
• There are four categories of constraints
– Data Type
– Legal Values
– Format
– Key Constraints
• Entity Integrity Constraints (Primary Key)
– Enforces the uniqueness of the primary key
• Referential Integrity Constraints (Foreign Key)
– Value of foreign key must match the value of primary key for
some row in another table
Integrity: Solutions
• Ignore constraint
– Undesirable as it can lead to inconsistent data
• Let user enforce the constraint
– Undesirable since user mistakes can be disastrous
• Let programmer build the logic of constraints in
the programs
– Makes programs complex: harder to write, harder to
maintain, and expensive
• Place burden on the DBMS.
– Preferred way: Cost of DBMS development
amortized over large user base, hence economical
Replication
• Duplication of data at multiple physical
locations
• Each replica of the data can be changed
independently
• Periodically the replicas update their data to
the master database – this process is called
synchronization
Disaster Planning: Backup & Recovery
• Database can be damaged in a number of ways
– Power outage, disk crashes, floods, user errors
• Periodic backups limit the loss due to sudden
failures
• Data can be recovered from the latest backup
and the changes since the backup need to be
done in either of two ways
– Manually
– From a catalog (if exists) recording all updates to
the database since the last backup.
Catalog/Data Dictionary
• Contains information describing the database
– Schema for the database
– Characteristic for each field
– Possible values for each field
– Description of the data
– Relationships
– Description of the programs
• Data Dictionary is same as catalog but may
contain wider set of information than catalog
You might also like
- SAP-Adv ABAP-2Document237 pagesSAP-Adv ABAP-2Tejaswi paritala100% (1)
- DbmsDocument16 pagesDbmsDEVANSH VERMANo ratings yet
- DBMS Functions Data, Storage, Retrieval, and UpdateDocument14 pagesDBMS Functions Data, Storage, Retrieval, and UpdatescribddinnieNo ratings yet
- DMA Chapter No5Document15 pagesDMA Chapter No5Kiran KshirsagarNo ratings yet
- Mis - Data Files and DatabasesDocument40 pagesMis - Data Files and DatabasesSaikatiNo ratings yet
- School of Future Studies and Planning (Davv Indore) Presentation On: "Database Management System"Document15 pagesSchool of Future Studies and Planning (Davv Indore) Presentation On: "Database Management System"h_toshi11No ratings yet
- Tybca Recent Trends in It Chpter 1Document16 pagesTybca Recent Trends in It Chpter 1aishwarya sajiNo ratings yet
- Dbms Unit-1 - Important PointsDocument58 pagesDbms Unit-1 - Important PointsSathwika DoddarapuNo ratings yet
- RDBMS 1Document37 pagesRDBMS 1Sreeram VijapurapuNo ratings yet
- Intro To Database Systems & DBMSDocument17 pagesIntro To Database Systems & DBMSgurungeNo ratings yet
- Unit 4 - MDocument40 pagesUnit 4 - Mriyan hussainNo ratings yet
- Chapter 1Document39 pagesChapter 1YasukeNo ratings yet
- Management Information System I LECTURE 7 (Week 7) Data OrganisationDocument34 pagesManagement Information System I LECTURE 7 (Week 7) Data OrganisationMichael Affum OseikohNo ratings yet
- 02.advantages of Database ApproachDocument14 pages02.advantages of Database ApproachMadhuNo ratings yet
- Database Management Systems (DBMS) Course-KCS-501: Lec 1 - R. S. KohliDocument13 pagesDatabase Management Systems (DBMS) Course-KCS-501: Lec 1 - R. S. KohliRS kohliNo ratings yet
- Chapter 2: Information System & I.T. FundamentalsDocument182 pagesChapter 2: Information System & I.T. FundamentalsAnkx Gagan JaitewaliaNo ratings yet
- DBMS SlidesDocument127 pagesDBMS SlidesAmit KushwahaNo ratings yet
- Lesson 3 - Transactions - TheoryDocument26 pagesLesson 3 - Transactions - Theoryshania nkusiNo ratings yet
- Database Systems MISDocument22 pagesDatabase Systems MISYonse Epic StoriesNo ratings yet
- DBMS ch1Document25 pagesDBMS ch1SonalS NaikNo ratings yet
- DBMS Unit 1Document47 pagesDBMS Unit 1Faisal Nazir (ANDY)No ratings yet
- Database FundamentalsDocument36 pagesDatabase Fundamentalsjhon cardonaNo ratings yet
- 1-INTRODocument49 pages1-INTROshreztha3565No ratings yet
- Unit 1Document35 pagesUnit 1ssNo ratings yet
- Unit1 - FinalDocument71 pagesUnit1 - FinalRoshan ChoudharyNo ratings yet
- ER and NormalizationDocument158 pagesER and NormalizationTulipNo ratings yet
- Flat File SystemDocument18 pagesFlat File SystemSushil Kumar GoelNo ratings yet
- DBE Unit 1Document175 pagesDBE Unit 1gully boyNo ratings yet
- Introduction To Database Management SystemDocument50 pagesIntroduction To Database Management SystemDependra SinghNo ratings yet
- Module 1Document111 pagesModule 1Ronit ReddyNo ratings yet
- DBMSDocument10 pagesDBMSHarish AynapurNo ratings yet
- Security, Backup, Recovery, Tuning, Testing of Data Mining and WarehousingDocument16 pagesSecurity, Backup, Recovery, Tuning, Testing of Data Mining and Warehousingdeepika2804No ratings yet
- DBMSDocument52 pagesDBMSjjs17No ratings yet
- 9-Database System ArchitectureDocument37 pages9-Database System ArchitectureAdwaithAdwaithDNo ratings yet
- DBE Unit 1Document175 pagesDBE Unit 1Siddharth PatilNo ratings yet
- Relational Database Management Systems: UNIT-1Document120 pagesRelational Database Management Systems: UNIT-1Srinivas KanakalaNo ratings yet
- Presentation1 DatabaseDocument49 pagesPresentation1 DatabaseSameedNo ratings yet
- Unit 1.1 IntroductionDocument21 pagesUnit 1.1 Introductionranaji181223No ratings yet
- Midterm Exam FDS PDFDocument35 pagesMidterm Exam FDS PDFAlthea ManlapazNo ratings yet
- Unit 6 Advanced DatabasesDocument108 pagesUnit 6 Advanced DatabasesOmkarNo ratings yet
- Distributed File Systems (DFS) : A Resource Management Component of A Distributed Operating SystemDocument16 pagesDistributed File Systems (DFS) : A Resource Management Component of A Distributed Operating SystemVasu DevanNo ratings yet
- Database Systems Concepts and Architecture: Dheeba. J/SCOPEDocument27 pagesDatabase Systems Concepts and Architecture: Dheeba. J/SCOPEPuneet PurohitNo ratings yet
- Module 1 SudhaDocument129 pagesModule 1 SudhaRupith Kumar .NNo ratings yet
- 1002DB CH1Document16 pages1002DB CH1Ahmad TamimiNo ratings yet
- Advantages of ObjectDocument11 pagesAdvantages of ObjectAman KukarNo ratings yet
- AE 110 Module 2Document6 pagesAE 110 Module 2Karen GuimbaoanNo ratings yet
- DBMSDocument61 pagesDBMSsangiwenmoyoNo ratings yet
- Database Management System: Dr. G. Jasmine Beulah, Dept. Computer Science Kristu Jayanti College, BengaluruDocument49 pagesDatabase Management System: Dr. G. Jasmine Beulah, Dept. Computer Science Kristu Jayanti College, BengaluruRaj KundraNo ratings yet
- 03 Etl 081028 2055Document46 pages03 Etl 081028 2055Mahesh SharmaNo ratings yet
- DBMSDocument61 pagesDBMSShubham MehtaNo ratings yet
- DBMSDocument61 pagesDBMSvikrant kumarNo ratings yet
- Introduction To Database Management SystemDocument47 pagesIntroduction To Database Management SystemjisskuruvillaNo ratings yet
- The Database EnvironmentDocument16 pagesThe Database EnvironmentWahab MansoorNo ratings yet
- DBMS Lectures CompileDocument183 pagesDBMS Lectures CompileAvinash KrishnaNo ratings yet
- Unit 1: Databases and Database UsersDocument25 pagesUnit 1: Databases and Database UsersVarun RameshNo ratings yet
- DBMS 1Document12 pagesDBMS 1Varun NNo ratings yet
- DBMS - CH1Document39 pagesDBMS - CH1Divit wadhwaniNo ratings yet
- DBMS - Chapter 1Document45 pagesDBMS - Chapter 1Harapriya MohantaNo ratings yet
- DBMSDocument373 pagesDBMSTushar PatelNo ratings yet
- 1 Introduction To Database SystemsDocument50 pages1 Introduction To Database SystemsMiya SamaNo ratings yet
- International Journal of Computer Science & Information SecurityDocument92 pagesInternational Journal of Computer Science & Information SecurityDhinaNo ratings yet
- Training Institute LibraryDocument2 pagesTraining Institute LibraryKannamaniNo ratings yet
- Unit 1 Mod 1 Structuring The Use Case ModelDocument28 pagesUnit 1 Mod 1 Structuring The Use Case ModelElias MetsingNo ratings yet
- Dbms IntroDocument36 pagesDbms IntroayanbaratNo ratings yet
- Next Generation Business Analytics Technology TrendsDocument17 pagesNext Generation Business Analytics Technology TrendsLightship Partners100% (3)
- Veritas Netbackup Cheat Sheet PDFDocument4 pagesVeritas Netbackup Cheat Sheet PDFAnvesh ReddyNo ratings yet
- Cambridge ICT Year 9 Topic 1 SlidesDocument31 pagesCambridge ICT Year 9 Topic 1 SlidesIce SyahNo ratings yet
- Enterprise Resource PlanningDocument11 pagesEnterprise Resource PlanningTanzil HaqueNo ratings yet
- Django 'Mahmoud Ahmed+Document342 pagesDjango 'Mahmoud Ahmed+yusufshabanNo ratings yet
- UDP - User Datagram ProtocolDocument7 pagesUDP - User Datagram ProtocolPeter R. Egli100% (2)
- System Administrator With DevOps Skills Questions - Set1Document2 pagesSystem Administrator With DevOps Skills Questions - Set1Ponnaya VaandaiyarNo ratings yet
- Cloud Computing Notes For BSC and BCADocument48 pagesCloud Computing Notes For BSC and BCAPvlsowjanya100% (4)
- 1as 1st Term Examthe InternetDocument2 pages1as 1st Term Examthe InternetJira GhNo ratings yet
- Hosts - Mas de 2000 SitiosDocument280 pagesHosts - Mas de 2000 Sitiosyiscar murilloNo ratings yet
- BPO CultureDocument2 pagesBPO Cultureshashi1810No ratings yet
- Introduction To ComputersDocument6 pagesIntroduction To ComputersFredalyn Joy VelaqueNo ratings yet
- IT Administrator - Cloud Job - DSV Shared Services Manila (ROHQ) - 10008009 - JobStreetDocument1 pageIT Administrator - Cloud Job - DSV Shared Services Manila (ROHQ) - 10008009 - JobStreetMarco ClerigoNo ratings yet
- DesignDocument5 pagesDesignjethin.aNo ratings yet
- R Lect1 IntroductionDocument16 pagesR Lect1 IntroductionAakash RajNo ratings yet
- Exam KasperskyDocument9 pagesExam Kasperskyrakyat mataramNo ratings yet
- Rudrajeet Singh: Professional SummaryDocument3 pagesRudrajeet Singh: Professional SummaryRudrajeet SinghNo ratings yet
- VC ProspectDocument11 pagesVC ProspectShrutiMarwahNo ratings yet
- Data Modeling EnglishDocument6 pagesData Modeling EnglishTrung Dang100% (1)
- Avaya Call Reporting Offer Definition 07april2020Document40 pagesAvaya Call Reporting Offer Definition 07april2020Miner ChidoteNo ratings yet
- Top 10 Benchmarking MisconceptionsDocument8 pagesTop 10 Benchmarking Misconceptionslaurio0No ratings yet
- Info HQ HL7 Specification RevF (732037-00F)Document54 pagesInfo HQ HL7 Specification RevF (732037-00F)pinheiromarcelinoNo ratings yet
- PB5514Document2 pagesPB5514parrastevens930No ratings yet
- M247 Cloud BrochureDocument7 pagesM247 Cloud BrochureBogdan GavrilutaNo ratings yet
- NPrinting and Qlikview PublisherDocument1 pageNPrinting and Qlikview PublisherMinuteq SharmaNo ratings yet