Professional Documents
Culture Documents
Basics in Number Theory
Basics in Number Theory
Uploaded by
lilac0 ratings0% found this document useful (0 votes)
18 views17 pagesThe document discusses the topics covered in the CSE 4003 CYBER SECURITY course. The 7 modules cover: 1) introduction to number theory including finite fields, modular arithmetic, and cryptographic techniques; 2) symmetric and asymmetric key cryptographic techniques; 3) integrity, authentication techniques like hash functions and digital signatures; 4) cybercrimes and offenses; 5) cyber threats, attacks and prevention; 6) cybersecurity policies and practices; and 7) recent trends.
Original Description:
Original Title
4. Basics in Number Theory
Copyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThe document discusses the topics covered in the CSE 4003 CYBER SECURITY course. The 7 modules cover: 1) introduction to number theory including finite fields, modular arithmetic, and cryptographic techniques; 2) symmetric and asymmetric key cryptographic techniques; 3) integrity, authentication techniques like hash functions and digital signatures; 4) cybercrimes and offenses; 5) cyber threats, attacks and prevention; 6) cybersecurity policies and practices; and 7) recent trends.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
0 ratings0% found this document useful (0 votes)
18 views17 pagesBasics in Number Theory
Basics in Number Theory
Uploaded by
lilacThe document discusses the topics covered in the CSE 4003 CYBER SECURITY course. The 7 modules cover: 1) introduction to number theory including finite fields, modular arithmetic, and cryptographic techniques; 2) symmetric and asymmetric key cryptographic techniques; 3) integrity, authentication techniques like hash functions and digital signatures; 4) cybercrimes and offenses; 5) cyber threats, attacks and prevention; 6) cybersecurity policies and practices; and 7) recent trends.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
You are on page 1of 17
CSE 4003 CYBER SECURITY
Module:1 Introduction to Number Theory
Finite Fields and Number Theory: Modular arithmetic, Euclidian Algorithm, Primality Testing: Fermats and
Eulers theorem, Chinese Reminder theorem, Discrete Logarithms
Module:2 Cryptographic Techniques
Symmetric key cryptographic techniques: Introduction to Stream cipher, Block cipher: DES, AES,IDEA
Asymmetric key cryptographic techniques: principles,RSA,ElGamal,Elliptic Curve cryptography, Key distribution
and Key exchange protocols.
Module:3 Integrity and Authentication
Hash functions,Secure Hash Algorithm (SHA)Message Authentication, Message Authentication Code (MAC),
Digital Signature Algorithm : RSA ElGamal based
Module:4 Cybercrimes and cyber offenses
Classification of cybercrimes, planning of attacks, social engineering:Human based, Computer based:
Cyberstalking, Cybercafe and Cybercrimes
Module:5 Cyber Threats, Attacks and Prevention
Phishing, Password cracking, Keyloggers and Spywares, DoS and DDoS attacks, SQL Injection Identity Theft (ID) :
Types of identity theft, Techniques of ID theft
Module:6 Cybersecurity Policies and Practices
What security policies are: determining the policy needs, writing security policies, Internet and email security
policies, Compliance and Enforcement of policies, Review
Module:7 Recent Trends
Basics in Number Theory
• Whole Number
• Natural Number
• Factor
• Prime Number
• Composite Number
• Greatest Common Divisor
• Co Prime
Whole Number
• A number without a decimal part and it has no
negatives.
• All Non Negative Integers
• 0,1,2,3,4,5,6,7………
What is a Natural Number
• Natural Number is an integer greater than 0
• It is a member of the set {1,2,3,4….}
• Natural Numbers are also known as counting
numbers.
Factor
• A factor is a number that divides another
number evenly with no reminder
• Factors are numbers you multiply to get other
numbers
Prime Numbers
• They have no other factors except for 1 and
the number itself
• A number that can only be factored as 1 times
itself is called "prime".
• 1 is not a prime number. It doesn’t have two
distinct factors.
• 2, 3, 5, 7, 11, 13, 17, 19, 23 ,29. ...
Composite Number
• Numbers that have more than 2 factors are
called as Composite numbers
• Positive Integers that have more than 2 factors
• Numbers that are divisible by more than two
numbers.
• 4, 6, 8, 9, 10, 12, 14, 15, 16, ...
Greatest Common Divisor
• GCD of two or more integers which are not
zero is the greatest positive integer that
divides each of the integers.
• GCD of two numbers is the greatest number
that divides both the numbers.
• GCD of 12 and 8 is 4
How to find GCD?
GCD by Division Method
• First take two of the given numbers , divide
the greater by the smaller number and then
divide the divisor by the reminder.
• The divisor which does not leave a reminder is
the GCD of the two numbers.
GCD by Division Method - Exercise
• Find the GCD of 30 and 45
• Find the GCD of 442 and 546
• Find the GCD of 442,546,424
Co Prime Number
• Set of numbers that have GCD as 1 are called as Co-Prime
Numbers
• For instance 7 and 8 are co-prime numbers
Properties of Co Prime Numbers
• 1 is coprime with every other number
• Prime numbers are co-prime to each other
• Any two successive numbers are always co-prime
• The sum of any two co-prime numbers is always co-prime with
their product
Identify the co-prime numbers
• 24, 36
• 20, 21
• 542, 446
Modular Arithmetic
Division Algorithm
Given any positive integer n and any
nonnegative integer a, if we divide a by n, we
get an integer quotient q and an integer
remainder r that obey the following relationship
a=qn+r 0<=r<n q=a/n
Example: 5&3
Divisor
• We say that a nonzero b divides a if a = mb for
some m, where a, b, and m are integers.
• That is, b divides a if there is no remainder on
division.
• The notation is commonly used to mean b
divides a. Also, if b|a, we say that b is a divisor
of a.
Properties of Divisor
• The following relations hold:
• If a|1, then a = ±1.
• Any b ≠ 0 divides 0.
• If b|g and b|h, then b|(mg + nh) for arbitrary
integers m and n.
You might also like
- Modern CryptographyDocument6 pagesModern Cryptographyprakash kumar katwal0% (1)
- GMAT Full Key NotesDocument8 pagesGMAT Full Key NotesRebecca Kuang91% (11)
- Quant Notes by Target 760Document11 pagesQuant Notes by Target 760kshitij_gaur13No ratings yet
- Stress-Free Math: A Visual Guide to Acing Math in Grades 4-9From EverandStress-Free Math: A Visual Guide to Acing Math in Grades 4-9No ratings yet
- Basic Concepts & Formulas of Number SystemDocument7 pagesBasic Concepts & Formulas of Number SystemShobhit MohtaNo ratings yet
- Group 2 Number Theory 2.5Document75 pagesGroup 2 Number Theory 2.5Rosa CarantoNo ratings yet
- MathDocument16 pagesMathhassan6936tNo ratings yet
- Math Report 1Document34 pagesMath Report 1balquinbesmonteNo ratings yet
- Algebra 1 2Document33 pagesAlgebra 1 2zyx xyzNo ratings yet
- Errors in Numerical ComputationDocument25 pagesErrors in Numerical ComputationFitriani HanipahNo ratings yet
- Grade 10 Session 1 Chapter 1 Reviewing Number ConceptsDocument31 pagesGrade 10 Session 1 Chapter 1 Reviewing Number ConceptsReham IbrahimNo ratings yet
- Number Theory and CryptographyDocument28 pagesNumber Theory and Cryptographypramod_bdvtNo ratings yet
- Worksheet U-WaterlooDocument8 pagesWorksheet U-WaterlooGideon Eka DirgantaraNo ratings yet
- Number Systems Cla.s 9 Notes CBSE Maths Chapter 1 (PDF)Document4 pagesNumber Systems Cla.s 9 Notes CBSE Maths Chapter 1 (PDF)Muhammad AsgharNo ratings yet
- Cambridge 11 Extension 1 - CH 2 - Numbers and SurdsDocument26 pagesCambridge 11 Extension 1 - CH 2 - Numbers and SurdsEsther CheungNo ratings yet
- UNIT 1 Lecture 1Document19 pagesUNIT 1 Lecture 1Peaceful SoulNo ratings yet
- Significant Figures Definition - Kelas 8Document8 pagesSignificant Figures Definition - Kelas 8Henry AndersonNo ratings yet
- Fundamental MathematicsDocument18 pagesFundamental MathematicsgileenNo ratings yet
- 09 Math Bootcamp, GRE Prep!Document23 pages09 Math Bootcamp, GRE Prep!Yush Khan100% (1)
- Me168 Chapter1 CompleteDocument44 pagesMe168 Chapter1 Completeprince agbekoNo ratings yet
- Lecture 1 IntroductionDocument22 pagesLecture 1 IntroductionvbweuhvbwNo ratings yet
- GMAT Club Math Book v3 - Jan-2-2013Document126 pagesGMAT Club Math Book v3 - Jan-2-2013barunbhattacharjee036No ratings yet
- Types of NumbersDocument2 pagesTypes of NumbersKenji LogieNo ratings yet
- Significant FiguresDocument17 pagesSignificant FiguresCatherine Joy BesanaNo ratings yet
- Number: SystemDocument6 pagesNumber: SystemAshutosh KumarNo ratings yet
- DS Lecture-10 Num THDocument34 pagesDS Lecture-10 Num THZaraNo ratings yet
- Digital Electronics: CT 304N Unit:1 Number Systems and CodesDocument172 pagesDigital Electronics: CT 304N Unit:1 Number Systems and CodesLiyanshu patelNo ratings yet
- Significant Figures and Scientific NotationDocument28 pagesSignificant Figures and Scientific NotationLance De VeraNo ratings yet
- Disc Week 12Document12 pagesDisc Week 12Huzaifa MughalNo ratings yet
- Number System, Simplification and ApproximationDocument58 pagesNumber System, Simplification and ApproximationKarthik RaviNo ratings yet
- Comparing NumbersDocument8 pagesComparing NumbersAlka100% (1)
- Classification of NumbersDocument19 pagesClassification of NumbersSoneNo ratings yet
- Asb Session 1Document76 pagesAsb Session 1Jay PatelNo ratings yet
- Cryptography and Network Security Self-Study: Submitted byDocument28 pagesCryptography and Network Security Self-Study: Submitted byHarryNo ratings yet
- Computer Programming For EngineersDocument41 pagesComputer Programming For EngineersBoss FabioNo ratings yet
- Significant FiguresDocument24 pagesSignificant FiguresJencel CruzNo ratings yet
- IBA BBA Math Lecture 01Document11 pagesIBA BBA Math Lecture 01abir157shantoNo ratings yet
- Data Representation in Computer SystemsDocument60 pagesData Representation in Computer Systemsdokumbaro30No ratings yet
- 02 G7 Division-IntegersDocument12 pages02 G7 Division-IntegersRicky DpusoyNo ratings yet
- Number Systems Groups of NumbersDocument10 pagesNumber Systems Groups of NumberswishabhijitNo ratings yet
- A - Scorm - INTRODUCTION TO NUMBER SYSTEM DIVISIBILITY RULES AND BODMASDocument19 pagesA - Scorm - INTRODUCTION TO NUMBER SYSTEM DIVISIBILITY RULES AND BODMASsonu sauravNo ratings yet
- Math BootcampDocument23 pagesMath BootcampKirankumar ReddyNo ratings yet
- GMAT Club Math Book v3 - Jan-2-2013Document126 pagesGMAT Club Math Book v3 - Jan-2-2013prabhakar0808No ratings yet
- GMAT Club Math Book June5Document95 pagesGMAT Club Math Book June5anilk12345No ratings yet
- Real Numbers PresentationDocument43 pagesReal Numbers PresentationitsankurzNo ratings yet
- ArithmeticDocument81 pagesArithmeticcherry agaNo ratings yet
- Number TheoryDocument10 pagesNumber Theorymotihama12No ratings yet
- Aptitude - 2: Sanju Abraham BinuDocument13 pagesAptitude - 2: Sanju Abraham BinuMrudul A ThakadiyelNo ratings yet
- Grade 5 MathematicsDocument71 pagesGrade 5 MathematicsLorena Seda-ClubNo ratings yet
- Master Fundamental Concepts of Math Olympiad: Maths, #1From EverandMaster Fundamental Concepts of Math Olympiad: Maths, #1No ratings yet
- Red TeamDocument10 pagesRed Teamrekibi.houssamNo ratings yet
- Cisco AnyConnect - SSL - VPN Hard Token User Guide v1.3Document10 pagesCisco AnyConnect - SSL - VPN Hard Token User Guide v1.3bharu2183No ratings yet
- Cyberoam CR 250i: Unified Threat ManagementDocument2 pagesCyberoam CR 250i: Unified Threat ManagementmdrhallyNo ratings yet
- Academic Individual Report: Network Penetration Test Case StudyDocument27 pagesAcademic Individual Report: Network Penetration Test Case StudyAudrey MwaleNo ratings yet
- Brkcol 2021Document152 pagesBrkcol 2021Mohammed Abdul HaseebNo ratings yet
- Login &logout OperationDocument8 pagesLogin &logout OperationChaitanyaNo ratings yet
- 6 Ways To Hack FTP Login PasswordDocument13 pages6 Ways To Hack FTP Login Passwordbla blaNo ratings yet
- Pixel: Multi-Signatures For ConsensusDocument19 pagesPixel: Multi-Signatures For ConsensusTaegyun KimNo ratings yet
- EC-Council: Exam Questions 312-38Document7 pagesEC-Council: Exam Questions 312-38kairatovdimash452No ratings yet
- OAG ExplorerUserguideDocument181 pagesOAG ExplorerUserguideMatiasNo ratings yet
- Barracuda Web Application Firewall DS US 1-6Document5 pagesBarracuda Web Application Firewall DS US 1-6mefot16939No ratings yet
- Computer and Internet CrimesDocument7 pagesComputer and Internet CrimesEjDungoNo ratings yet
- Introduction To Cyber Security Handbook PDFDocument104 pagesIntroduction To Cyber Security Handbook PDFVjay MadhamNo ratings yet
- Ethics MCQ 1Document52 pagesEthics MCQ 1ahmedamjed440No ratings yet
- Cryptography Algorithms Protocols - Zoubir MammeriDocument616 pagesCryptography Algorithms Protocols - Zoubir Mammeriabdulazizshamsa420No ratings yet
- Transport Layer Protection: Troy Hunt @troyhuntDocument11 pagesTransport Layer Protection: Troy Hunt @troyhuntnicolas ortizNo ratings yet
- SSL Server Test - MyntraDocument5 pagesSSL Server Test - MyntraAjay BhosaleNo ratings yet
- Cisco PVC300Document375 pagesCisco PVC300David VelasquezNo ratings yet
- Firewall - Sonicwall ModelsDocument2 pagesFirewall - Sonicwall Modelsrahulsai099No ratings yet
- Additive Cipher: Representation of Plaintext and Ciphertext Characters in ZDocument1 pageAdditive Cipher: Representation of Plaintext and Ciphertext Characters in ZMohamed MohamedNo ratings yet
- Exercise Meeting 5Document3 pagesExercise Meeting 5RanggaNo ratings yet
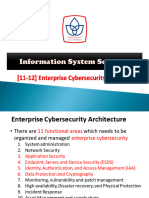
- PU Is Security - 12. Enterprise Cybersecurity ArchitectureDocument42 pagesPU Is Security - 12. Enterprise Cybersecurity ArchitecturealifaldindaNo ratings yet
- Temp 8655876524900479039Document10 pagesTemp 8655876524900479039ballerbell900No ratings yet
- PROTOCOLS FOR SECURE COMMUNICATIONS-reportingDocument4 pagesPROTOCOLS FOR SECURE COMMUNICATIONS-reportingJessica De ChavezNo ratings yet
- TrueCrack English PresentationDocument16 pagesTrueCrack English PresentationSviatoslav ChumakovNo ratings yet
- Ebook - A Complete Guide To CybersecurityDocument29 pagesEbook - A Complete Guide To CybersecuritydsaNo ratings yet
- Secret-Key Encryption LabDocument7 pagesSecret-Key Encryption LabReveng EngNo ratings yet
- Câu hỏiontapatttDocument117 pagesCâu hỏiontapatttnguyen toanNo ratings yet
- 646b7124add15 Cyber-SecurityDocument16 pages646b7124add15 Cyber-SecurityUsman AleeNo ratings yet