Professional Documents
Culture Documents
Ch22 Firewalls
Ch22 Firewalls
Uploaded by
DuttaUdayaVenkataChegondi0 ratings0% found this document useful (0 votes)
7 views27 pagesFirewalls act as a choke point between networks, restricting unauthorized traffic and monitoring activity. They include packet filters that examine IP packets, stateful filters that track session context, application proxies that validate requests, and circuit gateways that relay TCP connections. Firewalls can be implemented as host-based software, personal firewalls for individual devices, or network firewalls using bastion hosts and various topology configurations including DMZs, VPNs, and distributed setups.
Original Description:
Copyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentFirewalls act as a choke point between networks, restricting unauthorized traffic and monitoring activity. They include packet filters that examine IP packets, stateful filters that track session context, application proxies that validate requests, and circuit gateways that relay TCP connections. Firewalls can be implemented as host-based software, personal firewalls for individual devices, or network firewalls using bastion hosts and various topology configurations including DMZs, VPNs, and distributed setups.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
0 ratings0% found this document useful (0 votes)
7 views27 pagesCh22 Firewalls
Ch22 Firewalls
Uploaded by
DuttaUdayaVenkataChegondiFirewalls act as a choke point between networks, restricting unauthorized traffic and monitoring activity. They include packet filters that examine IP packets, stateful filters that track session context, application proxies that validate requests, and circuit gateways that relay TCP connections. Firewalls can be implemented as host-based software, personal firewalls for individual devices, or network firewalls using bastion hosts and various topology configurations including DMZs, VPNs, and distributed setups.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
You are on page 1of 27
Cryptography and
Network Security
Chapter 22
Fifth Edition
by William Stallings
Lecture slides by Lawrie Brown
Chapter 20 – Firewalls
The function of a strong position is to make
the forces holding it practically
unassailable
—On War, Carl Von Clausewitz
Introduction
seen evolution of information systems
now everyone want to be on the Internet
and to interconnect networks
has persistent security concerns
can’t easily secure every system in org
typically use a Firewall
to provide perimeter defence
as part of comprehensive security strategy
What is a Firewall?
a choke point of control and monitoring
interconnects networks with differing trust
imposes restrictions on network services
only authorized traffic is allowed
auditing and controlling access
can implement alarms for abnormal behavior
provideNAT & usage monitoring
implement VPNs using IPSec
must be immune to penetration
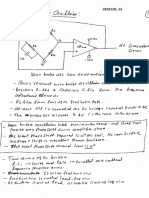
What is a Firewall?
Firewall Limitations
cannot protect from attacks bypassing it
e.g., sneaker net, utility modems, trusted
organisations, trusted services (eg SSL/SSH)
cannot protect against internal threats
e.g., disgruntled or colluding employees
cannot protect against access via WLAN
if improperly secured against external use
cannot protect against malware imported
via laptop, PDA, storage infected outside
Firewalls – Packet Filters
simplest, fastest firewall component
foundation of any firewall system
examine each IP packet (no context) and
permit or deny according to rules
hence restrict access to services (ports)
possible default policies
that not expressly permitted is prohibited
that not expressly prohibited is permitted
Firewalls – Packet Filters
Firewalls – Packet Filters
Attacks on Packet Filters
IP address spoofing
fake source address to be trusted
add filters on router to block
source routing attacks
attacker sets a route other than default
block source routed packets
tiny fragment attacks
split header info over several tiny packets
either discard or reassemble before check
Firewalls – Stateful Packet Filters
traditional
packet filters do not examine
higher layer context
ie matching return packets with outgoing flow
stateful
packet filters address this need
they examine each IP packet in context
keep track of client-server sessions
check each packet validly belongs to one
hence are better able to detect bogus
packets out of context
may even inspect limited application data
Firewalls - Application Level
Gateway (or Proxy)
have application specific gateway / proxy
has full access to protocol
user requests service from proxy
proxy validates request as legal
then actions request and returns result to user
can log / audit traffic at application level
need separate proxies for each service
some services naturally support proxying
others are more problematic
Firewalls - Application Level
Gateway (or Proxy)
Firewalls - Circuit Level Gateway
relays two TCP connections
imposes security by limiting which such
connections are allowed
once created usually relays traffic without
examining contents
typically used when trust internal users by
allowing general outbound connections
SOCKS is commonly used
Firewalls - Circuit Level Gateway
Bastion Host
highly secure host system
runs circuit / application level gateways
or provides externally accessible services
potentially exposed to "hostile" elements
hence is secured to withstand this
hardened O/S, essential services, extra auth
proxies small, secure, independent, non-privileged
may support 2 or more net connections
may be trusted to enforce policy of trusted
separation between these net connections
Host-Based Firewalls
s/w module used to secure individual host
available in many operating systems
or can be provided as an add-on package
oftenused on servers
advantages:
can tailor filtering rules to host environment
protection is provided independent of topology
provides an additional layer of protection
Personal Firewalls
controls traffic between PC/workstation
and Internet or enterprise network
a software module on personal computer
or in home/office DSL/cable/ISP router
typically much less complex than other
firewall types
primary role to deny unauthorized remote
access to the computer
and monitor outgoing activity for malware
Personal Firewalls
Firewall Configurations
Firewall Configurations
Firewall Configurations
DMZ
Networks
Virtual Private Networks
Distributed
Firewalls
Summary of Firewall
Locations and Topologies
host-resident firewall
screening router
single bastion inline
single bastion T
double bastion inline
double bastion T
distributed firewall configuration
Summary
have considered:
firewalls
types of firewalls
• packet-filter, stateful inspection, application proxy,
circuit-level
basing
• bastion, host, personal
location and configurations
• DMZ, VPN, distributed, topologies
You might also like
- Expert Proficiency Audioscripts PDFDocument30 pagesExpert Proficiency Audioscripts PDFAna María Hupan100% (5)
- VLSM Work BookDocument89 pagesVLSM Work BookBruna VieiraNo ratings yet
- CH 22Document27 pagesCH 22Vipul PurohitNo ratings yet
- Network Security Essentials: Fourth Edition by William StallingsDocument27 pagesNetwork Security Essentials: Fourth Edition by William StallingsXozanNo ratings yet
- FirewallsDocument21 pagesFirewallsSmily TheresaNo ratings yet
- Chapter # 06 Security TechnologyDocument33 pagesChapter # 06 Security Technologysadam hussainNo ratings yet
- FirewallsDocument26 pagesFirewallsDuttaUdayaVenkataChegondiNo ratings yet
- What Is FirewallDocument4 pagesWhat Is Firewallahmedtehseem0062No ratings yet
- Network Security FirewallsDocument21 pagesNetwork Security FirewallsÏñtïsãm ÄhmãdNo ratings yet
- Firewalls: Laura Mcfall Depaul University School of Computing and Digital MediaDocument84 pagesFirewalls: Laura Mcfall Depaul University School of Computing and Digital MediasuderNo ratings yet
- Why Do We Need Firewalls?Document18 pagesWhy Do We Need Firewalls?Raveendra Babu PonnuruNo ratings yet
- FirewallsDocument38 pagesFirewallsdeecodes13No ratings yet
- Firewalls: Security TechnologiesDocument63 pagesFirewalls: Security TechnologiespiyushNo ratings yet
- Unit-2: Network Defense ToolsDocument24 pagesUnit-2: Network Defense ToolsSandip MouryaNo ratings yet
- WQD7010 Network & Security: Dr. Saaidal Razalli Bin AzzuhriDocument40 pagesWQD7010 Network & Security: Dr. Saaidal Razalli Bin AzzuhriAbu Aisyah Yat SaaidalNo ratings yet
- A Firewall Is An ApplianceDocument4 pagesA Firewall Is An ApplianceTripathi VinaNo ratings yet
- Firewall and TypesDocument6 pagesFirewall and TypesJeremy KipgenNo ratings yet
- A Firewall Is An ApplianceDocument4 pagesA Firewall Is An ApplianceEbihuxiyowNo ratings yet
- Firewall: By: Amit Mahajan Btech 7 SemDocument20 pagesFirewall: By: Amit Mahajan Btech 7 Semamit mahajan100% (1)
- Network Firewall 4Document8 pagesNetwork Firewall 4earl bagainNo ratings yet
- FireDocument61 pagesFireAnuj SinghNo ratings yet
- Unit 4 Network SecurityDocument11 pagesUnit 4 Network SecuritySachin MaruNo ratings yet
- 83 10 41 PDFDocument7 pages83 10 41 PDFPhillipNo ratings yet
- Firewalls: (Tool For InformationDocument24 pagesFirewalls: (Tool For Informationdhruvvinayak100% (1)
- w6 FirewallsDocument59 pagesw6 FirewallshajerpcNo ratings yet
- Data Security On Local Network Using Distributed FirewallDocument22 pagesData Security On Local Network Using Distributed Firewallprabint100% (1)
- Cryptography and Network SecurityDocument30 pagesCryptography and Network SecurityAnonymous 1ioUBbNNo ratings yet
- FirewallDocument63 pagesFirewallLorie Jane ReyesNo ratings yet
- Computer SecurityDocument15 pagesComputer Securitymakangara22No ratings yet
- FirewallDocument4 pagesFirewallitinfoparkNo ratings yet
- Netwok CDocument36 pagesNetwok CMohammad Jakirul IslamNo ratings yet
- Presented By:: Geet Goel Gaurav RustogiDocument14 pagesPresented By:: Geet Goel Gaurav RustogiGaurav KumarNo ratings yet
- 2-Firewall TechnologyDocument10 pages2-Firewall TechnologyConstantin SanduNo ratings yet
- Firewall 86 SlidesDocument86 pagesFirewall 86 SlidesHarneet Singh ChuggaNo ratings yet
- Unit 4Document23 pagesUnit 4agasyabutoliaNo ratings yet
- Firewalls: The Function of A Strong Position Is To Make The Forces Holding It Practically UnassailableDocument26 pagesFirewalls: The Function of A Strong Position Is To Make The Forces Holding It Practically UnassailableVishnu Prasad GoranthalaNo ratings yet
- On Firewall ReportDocument12 pagesOn Firewall ReportPrincess Yashika0% (1)
- Design and Implementation of Firewall Security Policies Using Linux Iptables, UFW, FirewalldDocument11 pagesDesign and Implementation of Firewall Security Policies Using Linux Iptables, UFW, FirewalldUjjwal pandeyNo ratings yet
- Chapter6 Review Question&ExercisesDocument6 pagesChapter6 Review Question&ExercisesZenric Jr ClareteNo ratings yet
- Assignment 12: Data and Network Security Using Firewall: - Soham SalviDocument3 pagesAssignment 12: Data and Network Security Using Firewall: - Soham Salvisamy02No ratings yet
- 5 SecurityDocument38 pages5 SecurityHiwot TadesseNo ratings yet
- Guidelines in Firewalls and Firewall Policies: Recommendation of The National Institute of Standards and Technology Released On 2009Document5 pagesGuidelines in Firewalls and Firewall Policies: Recommendation of The National Institute of Standards and Technology Released On 2009mo3awia2099No ratings yet
- CH 20Document29 pagesCH 20Sukhanya AyappanNo ratings yet
- FirewallDocument3 pagesFirewallrahulpaswan8307No ratings yet
- Assignment - 1 Cryptography R177219017Document9 pagesAssignment - 1 Cryptography R177219017singhal9549akashNo ratings yet
- DCE Chapter 6 - IIDocument19 pagesDCE Chapter 6 - IIPurvaNo ratings yet
- FirewallsDocument16 pagesFirewallsshashwat2010No ratings yet
- Firewalls and Network SecurityDocument22 pagesFirewalls and Network SecurityHiruni AyodyaNo ratings yet
- CH 09Document24 pagesCH 09jahou NoelNo ratings yet
- Types of FirewallDocument5 pagesTypes of FirewallChandra Babu100% (1)
- CCNA Security Interview QuestionsDocument14 pagesCCNA Security Interview QuestionsKrishnaBandhaviramam'sNo ratings yet
- QuestionsDocument43 pagesQuestionssukeerthi bmeNo ratings yet
- Unit VDocument53 pagesUnit Vjayaraj2024No ratings yet
- 08-CH09-CompSec2e-ver02 Firewalls PDFDocument33 pages08-CH09-CompSec2e-ver02 Firewalls PDFNikunj PatelNo ratings yet
- A Firewall Is A Set of Related ProgramsDocument11 pagesA Firewall Is A Set of Related ProgramsDeep RandhawaNo ratings yet
- week13-FIREWALL IPTABLESDocument54 pagesweek13-FIREWALL IPTABLESПашаNo ratings yet
- What Is A Firewall?: Network-Level FirewallsDocument3 pagesWhat Is A Firewall?: Network-Level Firewallsgaurav sharmaNo ratings yet
- Unit 5Document14 pagesUnit 5kaavya shruthiNo ratings yet
- Firrewall and Intrusion Prevention SystemDocument23 pagesFirrewall and Intrusion Prevention Systemfatima gullNo ratings yet
- Fire WallsDocument16 pagesFire Wallspipatec675No ratings yet
- Cryptography and Data Security Book 1: Proper Guide to Data Security in Communication Networks. Cryptography and Data Security in PracticeFrom EverandCryptography and Data Security Book 1: Proper Guide to Data Security in Communication Networks. Cryptography and Data Security in PracticeNo ratings yet
- CJJV: U ( L, - (JC.P EjDocument21 pagesCJJV: U ( L, - (JC.P EjDuttaUdayaVenkataChegondiNo ratings yet
- B HWJ,) Cy H': SH/FF-'Document16 pagesB HWJ,) Cy H': SH/FF-'DuttaUdayaVenkataChegondiNo ratings yet
- EC0421-lab Manual-Odd-2012-2013 (New)Document83 pagesEC0421-lab Manual-Odd-2012-2013 (New)DuttaUdayaVenkataChegondiNo ratings yet
- Input and Output ResistanceDocument7 pagesInput and Output ResistanceDuttaUdayaVenkataChegondiNo ratings yet
- S 17feedback AmplifierDocument24 pagesS 17feedback AmplifierDuttaUdayaVenkataChegondiNo ratings yet
- Secure Hashing AlgorithmDocument16 pagesSecure Hashing AlgorithmDuttaUdayaVenkataChegondiNo ratings yet
- G.K.mythel-Feed Back AmplifierDocument39 pagesG.K.mythel-Feed Back AmplifierDuttaUdayaVenkataChegondiNo ratings yet
- Secure Electronic Transaction: SMU CSE 5349/7349Document33 pagesSecure Electronic Transaction: SMU CSE 5349/7349DuttaUdayaVenkataChegondiNo ratings yet
- Feedback Amplifier1Document12 pagesFeedback Amplifier1DuttaUdayaVenkataChegondiNo ratings yet
- Hill CipherDocument17 pagesHill CipherDuttaUdayaVenkataChegondiNo ratings yet
- IPSecDocument22 pagesIPSecDuttaUdayaVenkataChegondiNo ratings yet
- MD5 AlgorithmDocument13 pagesMD5 AlgorithmDuttaUdayaVenkataChegondiNo ratings yet
- CH 02Document39 pagesCH 02Eli PriyatnaNo ratings yet
- Overview of IPSecDocument42 pagesOverview of IPSecDuttaUdayaVenkataChegondiNo ratings yet
- FirewallsDocument26 pagesFirewallsDuttaUdayaVenkataChegondiNo ratings yet
- 14 HashFunctionsDocument42 pages14 HashFunctionsDuttaUdayaVenkataChegondiNo ratings yet
- MD 5Document27 pagesMD 5DuttaUdayaVenkataChegondiNo ratings yet
- CH 11Document23 pagesCH 11DuttaUdayaVenkataChegondiNo ratings yet
- ch19 IPDocument27 pagesch19 IPDuttaUdayaVenkataChegondiNo ratings yet
- Data Encryption Standard (Des)Document17 pagesData Encryption Standard (Des)DuttaUdayaVenkataChegondiNo ratings yet
- Ec0015 Mobile ComputingDocument1 pageEc0015 Mobile ComputingDuttaUdayaVenkataChegondiNo ratings yet
- DiffieDocument24 pagesDiffieDuttaUdayaVenkataChegondiNo ratings yet
- E-Commerce Ink House ReportDocument10 pagesE-Commerce Ink House ReportHafsaNo ratings yet
- AirPrime EM75XX AT Command Reference r2 PDFDocument140 pagesAirPrime EM75XX AT Command Reference r2 PDFjacobbowserNo ratings yet
- Frontier (2016 TV Series)Document3 pagesFrontier (2016 TV Series)ezlynxNo ratings yet
- CL SP Mib Clabdef I07 080306Document16 pagesCL SP Mib Clabdef I07 080306Estefany GaleanoNo ratings yet
- Storage scv3000 - Deployment Guide - en Us PDFDocument109 pagesStorage scv3000 - Deployment Guide - en Us PDFIvo MayerNo ratings yet
- Welcome!: Congratulations!Document15 pagesWelcome!: Congratulations!Brandy CrawfordNo ratings yet
- HTTP TunnelDocument6 pagesHTTP TunnelDarkWolf_TrueNo ratings yet
- Crimdeflawyersaddendum PDFDocument48 pagesCrimdeflawyersaddendum PDFmary engNo ratings yet
- Epistles From Pap: Letters From The Man Known As 'The Will Rogers of Indiana' by Durham, Andrew Everett, 1882-1954Document167 pagesEpistles From Pap: Letters From The Man Known As 'The Will Rogers of Indiana' by Durham, Andrew Everett, 1882-1954Gutenberg.orgNo ratings yet
- Resume 234Document8 pagesResume 234vijay dharmavaramNo ratings yet
- Finalcomp PDFDocument60 pagesFinalcomp PDFJitendra Singh RauthanNo ratings yet
- Tax Account DeterminationDocument26 pagesTax Account DeterminationAnupa Wijesinghe100% (17)
- Resume Professional Writers Announce They Have Successfully Ensured Job Interviews For A Million Candidates WorldwideDocument4 pagesResume Professional Writers Announce They Have Successfully Ensured Job Interviews For A Million Candidates WorldwidePR.comNo ratings yet
- Abis Optimizer Data SheetDocument4 pagesAbis Optimizer Data SheetjoeorcoNo ratings yet
- Government of Uttar Pradesh: Traveller Registration ConfirmationDocument1 pageGovernment of Uttar Pradesh: Traveller Registration ConfirmationpraveensinghNo ratings yet
- Socket Programming: 15-441 Computer Networks, Spring 2008 Xi LiuDocument39 pagesSocket Programming: 15-441 Computer Networks, Spring 2008 Xi Liubad boyNo ratings yet
- C.V. Noel Ayllón InglésDocument2 pagesC.V. Noel Ayllón InglésNoel Ayllón RíosNo ratings yet
- Yealink-Sip-T20p Phone SetupguideDocument9 pagesYealink-Sip-T20p Phone SetupguideperiNo ratings yet
- Smart WaterDocument55 pagesSmart WaterAshraf AhmedNo ratings yet
- 10.1.4.4 Packet Tracer A - Identify MAC and IP Addresses InstructionsDocument3 pages10.1.4.4 Packet Tracer A - Identify MAC and IP Addresses InstructionsGlennOpleAvendañoNo ratings yet
- (HDFC Ergo) - (Community) Pitch Deck v1.2Document90 pages(HDFC Ergo) - (Community) Pitch Deck v1.2Hemali GoriNo ratings yet
- List of Countries by Average Elevation - WikipediaDocument8 pagesList of Countries by Average Elevation - Wikipediamalaparte127No ratings yet
- Purposive Communication Unit 5-6Document8 pagesPurposive Communication Unit 5-6emat mendozaNo ratings yet
- SSL R&D Workshop Raleigh, NC - Sandhi Bhide (02!03!16)Document20 pagesSSL R&D Workshop Raleigh, NC - Sandhi Bhide (02!03!16)Sandhi BhideNo ratings yet
- Configuring and Testing Your NetworkDocument56 pagesConfiguring and Testing Your NetworkCahaya PenyayangNo ratings yet
- Computer Security Management Class WorkDocument67 pagesComputer Security Management Class WorkShan MayaNo ratings yet
- Week 2 - VLANsDocument24 pagesWeek 2 - VLANsQiu LeNo ratings yet
- Introduction To Video Conferencing PDFDocument8 pagesIntroduction To Video Conferencing PDFanenejeNo ratings yet