Professional Documents
Culture Documents
Ahsan Ullah - 21109109
Ahsan Ullah - 21109109
Uploaded by
Dr. Danish MehmoodCopyright:
Available Formats
You might also like
- Ceh Practical Exam QuestionsDocument4 pagesCeh Practical Exam QuestionsAnuj bhardwaj100% (2)
- Customer-Partners - WINDOW-POC GUIDE Harmony EndPoint EPM R81.10 - Step by Step Version FinalDocument39 pagesCustomer-Partners - WINDOW-POC GUIDE Harmony EndPoint EPM R81.10 - Step by Step Version Finalgarytj210% (1)
- Malware Detection and Classification Based On Extraction of API SequencesDocument6 pagesMalware Detection and Classification Based On Extraction of API SequencesYalew AdimassuNo ratings yet
- Deep Machine Learning Meets CybersecurityDocument14 pagesDeep Machine Learning Meets CybersecurityMILTON ENRIQUE CHINCHAY CELADANo ratings yet
- Malgene: Automatic Extraction of Malware Analysis Evasion SignatureDocument12 pagesMalgene: Automatic Extraction of Malware Analysis Evasion SignatureJuan Alfredo Salas SantillanaNo ratings yet
- Udayakumar 2017Document6 pagesUdayakumar 2017sayko3233No ratings yet
- Dynamic Malware AnalysisDocument6 pagesDynamic Malware AnalysisBik AshNo ratings yet
- Integrated Malware Analysis Using Machine Learning PDFDocument8 pagesIntegrated Malware Analysis Using Machine Learning PDFMike RomeoNo ratings yet
- Study of An Anti-Virus Framework: Ming Zhang and Wei ChenDocument4 pagesStudy of An Anti-Virus Framework: Ming Zhang and Wei Chenarceldavemanalo507No ratings yet
- MalwareAnalysis Report2S17Document15 pagesMalwareAnalysis Report2S17itcom068No ratings yet
- NovelIRS MIRAT PresentationDocument18 pagesNovelIRS MIRAT PresentationPt sinergi teknologi BersatuNo ratings yet
- Juniper Sky Advanced Threat Prevention - 1566462191Document6 pagesJuniper Sky Advanced Threat Prevention - 1566462191Andrew TargaryenNo ratings yet
- White Paper - EDR - Targeted Attack AnalyticsDocument7 pagesWhite Paper - EDR - Targeted Attack Analyticsahmed gaafarNo ratings yet
- Malware Classification Using Static Disassembly and Machine LearningDocument10 pagesMalware Classification Using Static Disassembly and Machine LearningeDu809No ratings yet
- Ultimate Threat Response With Powerful VisibilityDocument4 pagesUltimate Threat Response With Powerful Visibilityoof oNo ratings yet
- Malicious Behavior Detection Using Windows Audit Logs: Konstantin Berlin David Slater Joshua SaxeDocument10 pagesMalicious Behavior Detection Using Windows Audit Logs: Konstantin Berlin David Slater Joshua SaxeUmmeHaniAsifNo ratings yet
- A Comprehensive Survey On Machine Learning Techniques For Android Malware DetectionDocument12 pagesA Comprehensive Survey On Machine Learning Techniques For Android Malware DetectionAbhinandan BanikNo ratings yet
- Malware AnalysisDocument5 pagesMalware AnalysisRavi KumarNo ratings yet
- ICIISDocument6 pagesICIISdejuNo ratings yet
- Malware Detection and Classification Based On Graph Convolutional Networks and Function Call GraphsDocument11 pagesMalware Detection and Classification Based On Graph Convolutional Networks and Function Call Graphsanwarshahphd2021No ratings yet
- Article 7Document9 pagesArticle 7Canberk AkbaşNo ratings yet
- Malware Detection and Suppression Using Blockchain TechnologyDocument6 pagesMalware Detection and Suppression Using Blockchain TechnologyBVS NAGABABUNo ratings yet
- A Behavior-Based Approach For Malware DetectionDocument15 pagesA Behavior-Based Approach For Malware DetectionEsraa odatNo ratings yet
- Phase 1 Midterm Presentation Group ID CSE19-G58Document18 pagesPhase 1 Midterm Presentation Group ID CSE19-G58Kartikey SharmaNo ratings yet
- Cysemol Manual ShortDocument59 pagesCysemol Manual ShortSrikanth S.No ratings yet
- Research PaperDocument8 pagesResearch PaperAnishNo ratings yet
- Unit 54Document51 pagesUnit 54Arvind VishnubhatlaNo ratings yet
- The Curious Case of Machine Learning in Malware Detection: Sherif Saad, William Briguglio and Haytham ElmiligiDocument8 pagesThe Curious Case of Machine Learning in Malware Detection: Sherif Saad, William Briguglio and Haytham ElmiligiTuan Anh NguyenNo ratings yet
- Install Computer Software CbetDocument42 pagesInstall Computer Software Cbetawinorebeca92No ratings yet
- Splunk User Behavior AnalyticsDocument2 pagesSplunk User Behavior AnalyticsPrasad ThoratNo ratings yet
- Question Bank 1Document6 pagesQuestion Bank 1siri chandanaNo ratings yet
- Malware DetectionDocument17 pagesMalware DetectionSanjana.SNo ratings yet
- Feature Selection For AlgorithmDocument5 pagesFeature Selection For AlgorithmKishor MalikNo ratings yet
- Unsupervised Anomaly-Based Malware Detection Using Hardware FeaturesDocument12 pagesUnsupervised Anomaly-Based Malware Detection Using Hardware FeaturesSandro MeloNo ratings yet
- JSDC: A Hybrid Approach For Javascript Malware Detection and ClassificationDocument12 pagesJSDC: A Hybrid Approach For Javascript Malware Detection and ClassificationMauricio CabreraNo ratings yet
- IRJET Intrusion Detection System Using SDocument6 pagesIRJET Intrusion Detection System Using Sanand.dhawaleNo ratings yet
- AICSDocument42 pagesAICSsatyam.jhawarNo ratings yet
- Gunadarma Workshopsecurity 170310091703Document31 pagesGunadarma Workshopsecurity 170310091703Herdian NugrahaNo ratings yet
- A Malware Detection Approach Using Autoencoder in Deep LearningDocument11 pagesA Malware Detection Approach Using Autoencoder in Deep LearningAd AstraNo ratings yet
- Matlab Expo 2021 Deploying Ai On Plcs EdtDocument26 pagesMatlab Expo 2021 Deploying Ai On Plcs EdtZine eddine Hadj mokhnachrNo ratings yet
- Kaspersky Lab Whitepaper Machine LearningDocument17 pagesKaspersky Lab Whitepaper Machine LearningMochamad Beta AuditamaNo ratings yet
- Catch Them Alive: Malware DetectionDocument19 pagesCatch Them Alive: Malware DetectionYolgezer İsviçre'deNo ratings yet
- Ijwp 2020010101 PDFDocument11 pagesIjwp 2020010101 PDFWatthanasak JeamwatthanachaiNo ratings yet
- Multi Level Ransomware Detection FrameworkDocument8 pagesMulti Level Ransomware Detection FrameworkRyansNo ratings yet
- PDFDocument22 pagesPDFUmmeHaniAsifNo ratings yet
- STPA and Software Verification PDFDocument25 pagesSTPA and Software Verification PDFAsim AbdulkhaleqNo ratings yet
- Wildfire: Automatically Prevent Highly Evasive Zero-Day Exploits and MalwareDocument4 pagesWildfire: Automatically Prevent Highly Evasive Zero-Day Exploits and MalwarehelpdeskNo ratings yet
- Problem DomainDocument4 pagesProblem DomainmadhukedarNo ratings yet
- security-en-w6xh8-220404170950Document8 pagessecurity-en-w6xh8-220404170950Etnis IDNo ratings yet
- Ccs 21Document17 pagesCcs 21rkjadhav1453No ratings yet
- Kaspersky Lab Whitepaper Machine LearningDocument17 pagesKaspersky Lab Whitepaper Machine LearningCristian SalazarNo ratings yet
- Dissertation Proposal TemplateDocument9 pagesDissertation Proposal TemplateAswin KrishnanNo ratings yet
- Wildfire: Automatically Prevent Highly Evasive Zero-Day Exploits and MalwareDocument4 pagesWildfire: Automatically Prevent Highly Evasive Zero-Day Exploits and MalwareFelipe OlivieriNo ratings yet
- Ransomware Attack Detection Based On Pertinent System Calls Using Machine Learning TechniquesDocument23 pagesRansomware Attack Detection Based On Pertinent System Calls Using Machine Learning TechniquesAIRCC - IJCNCNo ratings yet
- Ransomware Attack Detection Based On Pertinent System Calls Using Machine Learning TechniquesDocument23 pagesRansomware Attack Detection Based On Pertinent System Calls Using Machine Learning TechniquesAIRCC - IJCNCNo ratings yet
- The Curious Case of Machine Learning in Malware Detection: Sherif Saad, William Briguglio and Haytham ElmiligiDocument9 pagesThe Curious Case of Machine Learning in Malware Detection: Sherif Saad, William Briguglio and Haytham ElmiligiTuan Anh NguyenNo ratings yet
- Analysis of Cyber Security Threats UsingDocument5 pagesAnalysis of Cyber Security Threats UsingJoramNo ratings yet
- Presentation Faisal Iqbal 01079Document13 pagesPresentation Faisal Iqbal 01079hamidNo ratings yet
- Digital Assignment 1Document7 pagesDigital Assignment 1FrankoNo ratings yet
- IBM Security QRadar SIEM DatasheetDocument6 pagesIBM Security QRadar SIEM DatasheetHitesh RahangdaleNo ratings yet
- Penetration Testing Fundamentals-2: Penetration Testing Study Guide To Breaking Into SystemsFrom EverandPenetration Testing Fundamentals-2: Penetration Testing Study Guide To Breaking Into SystemsNo ratings yet
- Irfan Nazir - 21109102Document1 pageIrfan Nazir - 21109102Dr. Danish MehmoodNo ratings yet
- Khairul Hayat 21109105 PDFDocument1 pageKhairul Hayat 21109105 PDFDr. Danish MehmoodNo ratings yet
- HamzaJaved 21109149Document1 pageHamzaJaved 21109149Dr. Danish MehmoodNo ratings yet
- Javariya Mufarrakh - 22110107 - MSBADocument1 pageJavariya Mufarrakh - 22110107 - MSBADr. Danish MehmoodNo ratings yet
- Khaliq Ur Rehman - 21109103 PSSGDocument1 pageKhaliq Ur Rehman - 21109103 PSSGDr. Danish MehmoodNo ratings yet
- MueedGulDurrani 21109156Document1 pageMueedGulDurrani 21109156Dr. Danish MehmoodNo ratings yet
- Osama QadeerDocument1 pageOsama QadeerDr. Danish MehmoodNo ratings yet
- COAL Lec01 IntroductionDocument19 pagesCOAL Lec01 IntroductionDr. Danish MehmoodNo ratings yet
- SleepingDogs-DE - x64+18Tr-LNG - v1.0 - INFODocument3 pagesSleepingDogs-DE - x64+18Tr-LNG - v1.0 - INFOAndri FitriansyahNo ratings yet
- Network Security v1.0 - Module 2Document52 pagesNetwork Security v1.0 - Module 2Ernesto Silverio FloresNo ratings yet
- A3-Static Malware Analysis To Identify Ransomware PropertiesDocument8 pagesA3-Static Malware Analysis To Identify Ransomware PropertiesAleja MoraNo ratings yet
- Online Access and Computer SecurityDocument17 pagesOnline Access and Computer Securitysagar salalNo ratings yet
- EVERYTHING LOST in A FEW CLICKS - Canadians Victims of International Online FraudDocument9 pagesEVERYTHING LOST in A FEW CLICKS - Canadians Victims of International Online FraudhyenadogNo ratings yet
- Computer VirusDocument5 pagesComputer Virussatudas149No ratings yet
- Azure Security Benchmark v3.0Document290 pagesAzure Security Benchmark v3.0Harish DasariNo ratings yet
- Computer Virus TypesDocument7 pagesComputer Virus TypesmohanakalaiselviNo ratings yet
- Text Mining in Cybersecurity A SystematicDocument36 pagesText Mining in Cybersecurity A SystematicRafael PaimNo ratings yet
- Ensilo/Fortiedr: Course DescriptionDocument2 pagesEnsilo/Fortiedr: Course DescriptionhoadiNo ratings yet
- Bca Ctis Sem-5 Digital Forensic InvestigationDocument20 pagesBca Ctis Sem-5 Digital Forensic InvestigationVikas SharmaNo ratings yet
- Kisi-Kisi CSCUDocument16 pagesKisi-Kisi CSCUHannaNo ratings yet
- English Project N1 Making A Job Application Booklet 2 AsDocument6 pagesEnglish Project N1 Making A Job Application Booklet 2 Askhkh100% (1)
- Red Team OperationsDocument15 pagesRed Team OperationsMarcelo JuniorNo ratings yet
- Chapter TwoDocument14 pagesChapter TwoGalatom YadetaNo ratings yet
- SurveillanceDocument26 pagesSurveillancesandhya vivekNo ratings yet
- Ebook - A Complete Guide To CybersecurityDocument29 pagesEbook - A Complete Guide To CybersecuritydsaNo ratings yet
- 840Dsl MD para Lists Man 1217 en-USDocument1,904 pages840Dsl MD para Lists Man 1217 en-USaaaaaaNo ratings yet
- Cyber Security and Cyber ThreatsDocument7 pagesCyber Security and Cyber ThreatsAnonymous CwJeBCAXpNo ratings yet
- MIS10E Testbank CH08Document20 pagesMIS10E Testbank CH08moath100% (3)
- Sophos EDR and XDR Use CasesDocument3 pagesSophos EDR and XDR Use Casesakram mabroukNo ratings yet
- Web Filter QuizDocument2 pagesWeb Filter Quizoviuap100% (1)
- Presentation Cyber SecurityDocument91 pagesPresentation Cyber SecurityReema Singh100% (2)
- Cisco IronPort Web Data Security and Data Loss Prevention OverviewDocument3 pagesCisco IronPort Web Data Security and Data Loss Prevention OverviewShaili SinghalNo ratings yet
- Cybersecurity Checklist 2018Document3 pagesCybersecurity Checklist 2018shellrootNo ratings yet
- Day 1 PCD CYBERSEC Cybersecurity Day 1Document186 pagesDay 1 PCD CYBERSEC Cybersecurity Day 1Gabriel OdunugaNo ratings yet
- Joe Sandbox Ultimate Feature SheetDocument2 pagesJoe Sandbox Ultimate Feature SheetdonoNo ratings yet
- Indusface WAS Premium - Advanced Systems Co. LTDDocument12 pagesIndusface WAS Premium - Advanced Systems Co. LTDshadab umairNo ratings yet
- Forcepoint Security Solutions Reference GuideDocument1 pageForcepoint Security Solutions Reference Guidehoangtruc.ptitNo ratings yet
Ahsan Ullah - 21109109
Ahsan Ullah - 21109109
Uploaded by
Dr. Danish MehmoodOriginal Description:
Original Title
Copyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Ahsan Ullah - 21109109
Ahsan Ullah - 21109109
Uploaded by
Dr. Danish MehmoodCopyright:
Available Formats
Shaheed Zulfiqar Ali Bhutto Institute of Science and Technology, Islamabad Campus
Faculty of Computing and Engineering Sciences
Static, Dynamic and Hybrid Techniques for Malware Analysis
Introduction
Static analysis systems (pre-execution analysis): Process malware without running it, and
Place
extract features to be used for malware detection and classification.
Dynamic analysis systems (post-execution analysis): It involves running the malware either in
Introductory
a physical or virtual environment, and searching for indicators of malicious activities
Hybrid Analysis Systems: The Static analysis and Dynamic analysis together called as Hybrid
Figure Here
Analysis. It is a file analysis approach that combines runtime data with memory dump analysis to
extract all possible execution pathways even for the most evasive malware. All data extracted from
the Hybrid Analysis engine is processed automatically and integrated into the malware analysis
reports.
Problem Statement
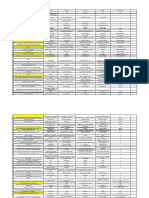
Top ten obfuscation techniques found in our dataset. | Top ten malware families in our collected dataset from VirusShare corpus.
Malware attacks cost billions of dollars annually.
65% of users feel effect of cyber crime.
28 days to resolve an average cybercrime.
90% of malware resists analysis.
Purpose and targeted audience
Malware analysis involves dissecting malware to
Discussions
understand how it works, and determine its Modern malware employs obfuscation, packing, encrypting, and
functionality, origin, and potential impact. other evading techniques to hide its malicious activities to bypass
antivirus software and advanced detection systems.
Malware analysis is essential for any business and
infrastructure that responds to cybersecurity incidents.
Proposed Model
Below are the Malware Analysis Techniques
Static Dynamic Hybrid Memory
API Call Function Call Combination of Process/Service
Static and Dynamic
CFG Function
Parameters DLL
Opcode Instruction Registry Keys
Traces
-
Network
N Gram Connections
Conclusion
Hybrid analysis technique analyze the signature of malware and
then combine it with behavioral pattern parameter but it only
analyzes the malware that is stored on the disk and the same
malware runs in the memory. Malware that sits and run in the
memory is either not checked or high probability that their
signature and behavioral pattern is not the same as the classic
malware that sits in the hard disk and run in the memory.
Ahsan Ullah(21109109)Fall 2022 MS Cyber Security
Malware Analysis
You might also like
- Ceh Practical Exam QuestionsDocument4 pagesCeh Practical Exam QuestionsAnuj bhardwaj100% (2)
- Customer-Partners - WINDOW-POC GUIDE Harmony EndPoint EPM R81.10 - Step by Step Version FinalDocument39 pagesCustomer-Partners - WINDOW-POC GUIDE Harmony EndPoint EPM R81.10 - Step by Step Version Finalgarytj210% (1)
- Malware Detection and Classification Based On Extraction of API SequencesDocument6 pagesMalware Detection and Classification Based On Extraction of API SequencesYalew AdimassuNo ratings yet
- Deep Machine Learning Meets CybersecurityDocument14 pagesDeep Machine Learning Meets CybersecurityMILTON ENRIQUE CHINCHAY CELADANo ratings yet
- Malgene: Automatic Extraction of Malware Analysis Evasion SignatureDocument12 pagesMalgene: Automatic Extraction of Malware Analysis Evasion SignatureJuan Alfredo Salas SantillanaNo ratings yet
- Udayakumar 2017Document6 pagesUdayakumar 2017sayko3233No ratings yet
- Dynamic Malware AnalysisDocument6 pagesDynamic Malware AnalysisBik AshNo ratings yet
- Integrated Malware Analysis Using Machine Learning PDFDocument8 pagesIntegrated Malware Analysis Using Machine Learning PDFMike RomeoNo ratings yet
- Study of An Anti-Virus Framework: Ming Zhang and Wei ChenDocument4 pagesStudy of An Anti-Virus Framework: Ming Zhang and Wei Chenarceldavemanalo507No ratings yet
- MalwareAnalysis Report2S17Document15 pagesMalwareAnalysis Report2S17itcom068No ratings yet
- NovelIRS MIRAT PresentationDocument18 pagesNovelIRS MIRAT PresentationPt sinergi teknologi BersatuNo ratings yet
- Juniper Sky Advanced Threat Prevention - 1566462191Document6 pagesJuniper Sky Advanced Threat Prevention - 1566462191Andrew TargaryenNo ratings yet
- White Paper - EDR - Targeted Attack AnalyticsDocument7 pagesWhite Paper - EDR - Targeted Attack Analyticsahmed gaafarNo ratings yet
- Malware Classification Using Static Disassembly and Machine LearningDocument10 pagesMalware Classification Using Static Disassembly and Machine LearningeDu809No ratings yet
- Ultimate Threat Response With Powerful VisibilityDocument4 pagesUltimate Threat Response With Powerful Visibilityoof oNo ratings yet
- Malicious Behavior Detection Using Windows Audit Logs: Konstantin Berlin David Slater Joshua SaxeDocument10 pagesMalicious Behavior Detection Using Windows Audit Logs: Konstantin Berlin David Slater Joshua SaxeUmmeHaniAsifNo ratings yet
- A Comprehensive Survey On Machine Learning Techniques For Android Malware DetectionDocument12 pagesA Comprehensive Survey On Machine Learning Techniques For Android Malware DetectionAbhinandan BanikNo ratings yet
- Malware AnalysisDocument5 pagesMalware AnalysisRavi KumarNo ratings yet
- ICIISDocument6 pagesICIISdejuNo ratings yet
- Malware Detection and Classification Based On Graph Convolutional Networks and Function Call GraphsDocument11 pagesMalware Detection and Classification Based On Graph Convolutional Networks and Function Call Graphsanwarshahphd2021No ratings yet
- Article 7Document9 pagesArticle 7Canberk AkbaşNo ratings yet
- Malware Detection and Suppression Using Blockchain TechnologyDocument6 pagesMalware Detection and Suppression Using Blockchain TechnologyBVS NAGABABUNo ratings yet
- A Behavior-Based Approach For Malware DetectionDocument15 pagesA Behavior-Based Approach For Malware DetectionEsraa odatNo ratings yet
- Phase 1 Midterm Presentation Group ID CSE19-G58Document18 pagesPhase 1 Midterm Presentation Group ID CSE19-G58Kartikey SharmaNo ratings yet
- Cysemol Manual ShortDocument59 pagesCysemol Manual ShortSrikanth S.No ratings yet
- Research PaperDocument8 pagesResearch PaperAnishNo ratings yet
- Unit 54Document51 pagesUnit 54Arvind VishnubhatlaNo ratings yet
- The Curious Case of Machine Learning in Malware Detection: Sherif Saad, William Briguglio and Haytham ElmiligiDocument8 pagesThe Curious Case of Machine Learning in Malware Detection: Sherif Saad, William Briguglio and Haytham ElmiligiTuan Anh NguyenNo ratings yet
- Install Computer Software CbetDocument42 pagesInstall Computer Software Cbetawinorebeca92No ratings yet
- Splunk User Behavior AnalyticsDocument2 pagesSplunk User Behavior AnalyticsPrasad ThoratNo ratings yet
- Question Bank 1Document6 pagesQuestion Bank 1siri chandanaNo ratings yet
- Malware DetectionDocument17 pagesMalware DetectionSanjana.SNo ratings yet
- Feature Selection For AlgorithmDocument5 pagesFeature Selection For AlgorithmKishor MalikNo ratings yet
- Unsupervised Anomaly-Based Malware Detection Using Hardware FeaturesDocument12 pagesUnsupervised Anomaly-Based Malware Detection Using Hardware FeaturesSandro MeloNo ratings yet
- JSDC: A Hybrid Approach For Javascript Malware Detection and ClassificationDocument12 pagesJSDC: A Hybrid Approach For Javascript Malware Detection and ClassificationMauricio CabreraNo ratings yet
- IRJET Intrusion Detection System Using SDocument6 pagesIRJET Intrusion Detection System Using Sanand.dhawaleNo ratings yet
- AICSDocument42 pagesAICSsatyam.jhawarNo ratings yet
- Gunadarma Workshopsecurity 170310091703Document31 pagesGunadarma Workshopsecurity 170310091703Herdian NugrahaNo ratings yet
- A Malware Detection Approach Using Autoencoder in Deep LearningDocument11 pagesA Malware Detection Approach Using Autoencoder in Deep LearningAd AstraNo ratings yet
- Matlab Expo 2021 Deploying Ai On Plcs EdtDocument26 pagesMatlab Expo 2021 Deploying Ai On Plcs EdtZine eddine Hadj mokhnachrNo ratings yet
- Kaspersky Lab Whitepaper Machine LearningDocument17 pagesKaspersky Lab Whitepaper Machine LearningMochamad Beta AuditamaNo ratings yet
- Catch Them Alive: Malware DetectionDocument19 pagesCatch Them Alive: Malware DetectionYolgezer İsviçre'deNo ratings yet
- Ijwp 2020010101 PDFDocument11 pagesIjwp 2020010101 PDFWatthanasak JeamwatthanachaiNo ratings yet
- Multi Level Ransomware Detection FrameworkDocument8 pagesMulti Level Ransomware Detection FrameworkRyansNo ratings yet
- PDFDocument22 pagesPDFUmmeHaniAsifNo ratings yet
- STPA and Software Verification PDFDocument25 pagesSTPA and Software Verification PDFAsim AbdulkhaleqNo ratings yet
- Wildfire: Automatically Prevent Highly Evasive Zero-Day Exploits and MalwareDocument4 pagesWildfire: Automatically Prevent Highly Evasive Zero-Day Exploits and MalwarehelpdeskNo ratings yet
- Problem DomainDocument4 pagesProblem DomainmadhukedarNo ratings yet
- security-en-w6xh8-220404170950Document8 pagessecurity-en-w6xh8-220404170950Etnis IDNo ratings yet
- Ccs 21Document17 pagesCcs 21rkjadhav1453No ratings yet
- Kaspersky Lab Whitepaper Machine LearningDocument17 pagesKaspersky Lab Whitepaper Machine LearningCristian SalazarNo ratings yet
- Dissertation Proposal TemplateDocument9 pagesDissertation Proposal TemplateAswin KrishnanNo ratings yet
- Wildfire: Automatically Prevent Highly Evasive Zero-Day Exploits and MalwareDocument4 pagesWildfire: Automatically Prevent Highly Evasive Zero-Day Exploits and MalwareFelipe OlivieriNo ratings yet
- Ransomware Attack Detection Based On Pertinent System Calls Using Machine Learning TechniquesDocument23 pagesRansomware Attack Detection Based On Pertinent System Calls Using Machine Learning TechniquesAIRCC - IJCNCNo ratings yet
- Ransomware Attack Detection Based On Pertinent System Calls Using Machine Learning TechniquesDocument23 pagesRansomware Attack Detection Based On Pertinent System Calls Using Machine Learning TechniquesAIRCC - IJCNCNo ratings yet
- The Curious Case of Machine Learning in Malware Detection: Sherif Saad, William Briguglio and Haytham ElmiligiDocument9 pagesThe Curious Case of Machine Learning in Malware Detection: Sherif Saad, William Briguglio and Haytham ElmiligiTuan Anh NguyenNo ratings yet
- Analysis of Cyber Security Threats UsingDocument5 pagesAnalysis of Cyber Security Threats UsingJoramNo ratings yet
- Presentation Faisal Iqbal 01079Document13 pagesPresentation Faisal Iqbal 01079hamidNo ratings yet
- Digital Assignment 1Document7 pagesDigital Assignment 1FrankoNo ratings yet
- IBM Security QRadar SIEM DatasheetDocument6 pagesIBM Security QRadar SIEM DatasheetHitesh RahangdaleNo ratings yet
- Penetration Testing Fundamentals-2: Penetration Testing Study Guide To Breaking Into SystemsFrom EverandPenetration Testing Fundamentals-2: Penetration Testing Study Guide To Breaking Into SystemsNo ratings yet
- Irfan Nazir - 21109102Document1 pageIrfan Nazir - 21109102Dr. Danish MehmoodNo ratings yet
- Khairul Hayat 21109105 PDFDocument1 pageKhairul Hayat 21109105 PDFDr. Danish MehmoodNo ratings yet
- HamzaJaved 21109149Document1 pageHamzaJaved 21109149Dr. Danish MehmoodNo ratings yet
- Javariya Mufarrakh - 22110107 - MSBADocument1 pageJavariya Mufarrakh - 22110107 - MSBADr. Danish MehmoodNo ratings yet
- Khaliq Ur Rehman - 21109103 PSSGDocument1 pageKhaliq Ur Rehman - 21109103 PSSGDr. Danish MehmoodNo ratings yet
- MueedGulDurrani 21109156Document1 pageMueedGulDurrani 21109156Dr. Danish MehmoodNo ratings yet
- Osama QadeerDocument1 pageOsama QadeerDr. Danish MehmoodNo ratings yet
- COAL Lec01 IntroductionDocument19 pagesCOAL Lec01 IntroductionDr. Danish MehmoodNo ratings yet
- SleepingDogs-DE - x64+18Tr-LNG - v1.0 - INFODocument3 pagesSleepingDogs-DE - x64+18Tr-LNG - v1.0 - INFOAndri FitriansyahNo ratings yet
- Network Security v1.0 - Module 2Document52 pagesNetwork Security v1.0 - Module 2Ernesto Silverio FloresNo ratings yet
- A3-Static Malware Analysis To Identify Ransomware PropertiesDocument8 pagesA3-Static Malware Analysis To Identify Ransomware PropertiesAleja MoraNo ratings yet
- Online Access and Computer SecurityDocument17 pagesOnline Access and Computer Securitysagar salalNo ratings yet
- EVERYTHING LOST in A FEW CLICKS - Canadians Victims of International Online FraudDocument9 pagesEVERYTHING LOST in A FEW CLICKS - Canadians Victims of International Online FraudhyenadogNo ratings yet
- Computer VirusDocument5 pagesComputer Virussatudas149No ratings yet
- Azure Security Benchmark v3.0Document290 pagesAzure Security Benchmark v3.0Harish DasariNo ratings yet
- Computer Virus TypesDocument7 pagesComputer Virus TypesmohanakalaiselviNo ratings yet
- Text Mining in Cybersecurity A SystematicDocument36 pagesText Mining in Cybersecurity A SystematicRafael PaimNo ratings yet
- Ensilo/Fortiedr: Course DescriptionDocument2 pagesEnsilo/Fortiedr: Course DescriptionhoadiNo ratings yet
- Bca Ctis Sem-5 Digital Forensic InvestigationDocument20 pagesBca Ctis Sem-5 Digital Forensic InvestigationVikas SharmaNo ratings yet
- Kisi-Kisi CSCUDocument16 pagesKisi-Kisi CSCUHannaNo ratings yet
- English Project N1 Making A Job Application Booklet 2 AsDocument6 pagesEnglish Project N1 Making A Job Application Booklet 2 Askhkh100% (1)
- Red Team OperationsDocument15 pagesRed Team OperationsMarcelo JuniorNo ratings yet
- Chapter TwoDocument14 pagesChapter TwoGalatom YadetaNo ratings yet
- SurveillanceDocument26 pagesSurveillancesandhya vivekNo ratings yet
- Ebook - A Complete Guide To CybersecurityDocument29 pagesEbook - A Complete Guide To CybersecuritydsaNo ratings yet
- 840Dsl MD para Lists Man 1217 en-USDocument1,904 pages840Dsl MD para Lists Man 1217 en-USaaaaaaNo ratings yet
- Cyber Security and Cyber ThreatsDocument7 pagesCyber Security and Cyber ThreatsAnonymous CwJeBCAXpNo ratings yet
- MIS10E Testbank CH08Document20 pagesMIS10E Testbank CH08moath100% (3)
- Sophos EDR and XDR Use CasesDocument3 pagesSophos EDR and XDR Use Casesakram mabroukNo ratings yet
- Web Filter QuizDocument2 pagesWeb Filter Quizoviuap100% (1)
- Presentation Cyber SecurityDocument91 pagesPresentation Cyber SecurityReema Singh100% (2)
- Cisco IronPort Web Data Security and Data Loss Prevention OverviewDocument3 pagesCisco IronPort Web Data Security and Data Loss Prevention OverviewShaili SinghalNo ratings yet
- Cybersecurity Checklist 2018Document3 pagesCybersecurity Checklist 2018shellrootNo ratings yet
- Day 1 PCD CYBERSEC Cybersecurity Day 1Document186 pagesDay 1 PCD CYBERSEC Cybersecurity Day 1Gabriel OdunugaNo ratings yet
- Joe Sandbox Ultimate Feature SheetDocument2 pagesJoe Sandbox Ultimate Feature SheetdonoNo ratings yet
- Indusface WAS Premium - Advanced Systems Co. LTDDocument12 pagesIndusface WAS Premium - Advanced Systems Co. LTDshadab umairNo ratings yet
- Forcepoint Security Solutions Reference GuideDocument1 pageForcepoint Security Solutions Reference Guidehoangtruc.ptitNo ratings yet