Professional Documents
Culture Documents
Information Security
Information Security
Uploaded by
makangara220 ratings0% found this document useful (0 votes)
6 views16 pagesKey certificates are digitally signed documents that bind a public key to an entity's identity and are essential for public key infrastructure systems. They contain information about the certificate holder, their public key, and are issued and managed by a trusted third party certificate authority. Certificate authorities verify identities before issuing standard X.509 format certificates to ensure integrity. Certificates are used to secure communication and applications like SSL/TLS, email encryption, code signing, and VPNs.
Original Description:
Original Title
Information Security.ppt
Copyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentKey certificates are digitally signed documents that bind a public key to an entity's identity and are essential for public key infrastructure systems. They contain information about the certificate holder, their public key, and are issued and managed by a trusted third party certificate authority. Certificate authorities verify identities before issuing standard X.509 format certificates to ensure integrity. Certificates are used to secure communication and applications like SSL/TLS, email encryption, code signing, and VPNs.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
0 ratings0% found this document useful (0 votes)
6 views16 pagesInformation Security
Information Security
Uploaded by
makangara22Key certificates are digitally signed documents that bind a public key to an entity's identity and are essential for public key infrastructure systems. They contain information about the certificate holder, their public key, and are issued and managed by a trusted third party certificate authority. Certificate authorities verify identities before issuing standard X.509 format certificates to ensure integrity. Certificates are used to secure communication and applications like SSL/TLS, email encryption, code signing, and VPNs.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
You are on page 1of 16
KEY CERTIFICATES
Key certificates, also known as digital
certificates or public key certificates, are
an essential component of public key
infrastructure (PKI) systems. They play a
INTRODUCT crucial role in securing online
ION communication, verifying the
authenticity of public keys, and
establishing trust between parties.
Here's a more detailed exploration of
key certificates
A key certificate is a digitally signed
document that binds a public key to a
particular entity's identity. It contains
information about the certificate holder
DEFINITION (such as their name or organization), the
public key itself, the issuing certificate
authority (CA), and additional metadata.
Certificate Authority(CA)
A CA is a trusted third-party
organization responsible for issuing and
managing key certificates. CAs verify the
CERTIFICAT identity of certificate applicants before
issuing certificates to ensure the
E integrity of the PKI system
AUTHORITY
Certificate format
AND
Key certificates are typically encoded
FORMAT
using standard formats such as X.509.
This format defines the structure and
fields within a certificate, facilitating
interoperability between different
systems and applications.
Digital certificate contain the following
valuable information
User’s name
Company or department of user
IP address or serial number of user
INFORMATI
ON Copy of the public key from the certified
holder
Duration of time the certificate is valid
for
Domain certificate is authorized to
present
Secure Sockets Layer/Transport Layer
Security (SSL/TLS).
APPLICATIO Email Encryption and Digital Signatures
NS Code Signing
Virtual Private Networks (VPNs)
Digital Signature
The authenticity of many legal, financial,
and other documents is determined by
the presence or absence of an
authorized handwritten signature.
Various methods have been devised to
INTRODUCT solve this problem, but the use of digital
signature’ is definitely the best solution
ION amongst them.
A digital signature is nothing but an
attachment to any piece of electronic
information, which represents the
content of the document and the
identity of the originator of that
document uniquely.
: A digital signature is a mathematical
scheme that involves the use of
WHAT IS cryptographic algorithms to sign digital
DIGITAL data. It provides a way to ensure that
SIGNATUR the data has not been altered or
tampered with since the signature was
E applied and that the signer cannot
deny their involvement.
Private Key
The private key is one which is accessible
only to the signer. It is used to generate
PRIVATE AND the digital signature which is then
PUBLIC KEY attached to the message.
Public Key
The public key is made available to all
those who receive the signed messages
from the sender. It is used for verification
of the received message.
PURPOSE Authentication
OF DIGITAL Non-repudiation
SIGNATURE
Integrity
Electronic Mail
APPLICATIONS Data storage
Electronic funds transfer
Software Distribution
Email security is a crucial
aspect of safeguarding
electronic communication
EMAIL from unauthorized access,
SECURITY interception, and malicious
activities. Here are some
key points related to email
security
Encryption
Secure Protocols
EMAIL Digital Signatures
SECURITY Phishing and Spam Protection
MEASURES Strong Passwords and Authentication
Email Filtering
Email Backup and Recovery
Thank you
You might also like
- PKI Interview QuestionsDocument18 pagesPKI Interview QuestionsVinay Kumar Yerra80% (5)
- SIEM&XDR Demo Guide v1.2 February2023Document26 pagesSIEM&XDR Demo Guide v1.2 February2023Zied BERRIMANo ratings yet
- PKI Interview QuestionsDocument18 pagesPKI Interview QuestionsSouthpaw Conor McGregor100% (3)
- Microsoft PKIDocument16 pagesMicrosoft PKIRam JiNo ratings yet
- Assignment 1 INFORMATION SECURITYDocument7 pagesAssignment 1 INFORMATION SECURITYmakangara22No ratings yet
- CSE Digital SignatureDocument20 pagesCSE Digital SignatureNadar SudhaNo ratings yet
- Digital SignatureDocument15 pagesDigital Signaturemahera KhatoonNo ratings yet
- Digital CertificatesDocument34 pagesDigital CertificatesSheetal VermaNo ratings yet
- Digital Certificate...Document33 pagesDigital Certificate...SwapnilPazareNo ratings yet
- Digital Signature Seminar ReportDocument15 pagesDigital Signature Seminar ReportAshish RajNo ratings yet
- Chapt 5Document11 pagesChapt 5ZoroNo ratings yet
- Law & Emerging Technologies: TH THDocument19 pagesLaw & Emerging Technologies: TH THAnuj Singh RaghuvanshiNo ratings yet
- DefinitionsDocument3 pagesDefinitionsSubhajit KunduNo ratings yet
- Digital Signature 8736 RPGXHVGDocument20 pagesDigital Signature 8736 RPGXHVGthasneem khanum 596No ratings yet
- Digital SignatureDocument21 pagesDigital SignatureAvneet KaurNo ratings yet
- Charu Gupta B.Tech CS 3 Yr Roll No. 0821510020Document27 pagesCharu Gupta B.Tech CS 3 Yr Roll No. 0821510020Charu GuptaNo ratings yet
- 2020BCS 076 IT CryptographyDocument27 pages2020BCS 076 IT CryptographyPavan KumarNo ratings yet
- Digital CertificatesDocument37 pagesDigital CertificatesRabiaNo ratings yet
- Public Key Infrastructure (PKIDocument16 pagesPublic Key Infrastructure (PKIhamza iliyas100% (1)
- Digital SignatureDocument31 pagesDigital SignatureAnupam BaliNo ratings yet
- Digital Signatures and Authentication ProtocolsDocument19 pagesDigital Signatures and Authentication ProtocolsMerryl Lorraine GonzagaNo ratings yet
- FM 6 Notes - Digital SignatureDocument4 pagesFM 6 Notes - Digital SignatureCHRISTINE JADUCANANo ratings yet
- Electronic & Digital SignatureDocument2 pagesElectronic & Digital Signatureprathyush.jainNo ratings yet
- Unit 4Document11 pagesUnit 4SAKSHI SHINDENo ratings yet
- Unit2 Law and Emerging TechnologyDocument9 pagesUnit2 Law and Emerging Technologygarima424582638No ratings yet
- Digital SignatureDocument31 pagesDigital SignatureVipin KumarNo ratings yet
- Building Managing Pki Solution Small Medium Size BusinessDocument24 pagesBuilding Managing Pki Solution Small Medium Size Businessderic soonNo ratings yet
- Improving The Security of Workflow-Based System Using Multiple XML Digital SignaturesDocument5 pagesImproving The Security of Workflow-Based System Using Multiple XML Digital SignatureserpublicationNo ratings yet
- SSL Protocol: SSL Objectives and ArchitectureDocument6 pagesSSL Protocol: SSL Objectives and Architecturemuntaha_ahmedNo ratings yet
- Digtal Signature 19mco014Document2 pagesDigtal Signature 19mco014emmanual cheeranNo ratings yet
- Digital Signatures 2Document49 pagesDigital Signatures 2nilesh2050No ratings yet
- The Web's Security BlanketDocument31 pagesThe Web's Security BlanketMd BilalNo ratings yet
- Digital Signature: Presented by K.ANITHA (19065) T.DIVYA (19074) T.PAVAN (19082) P.Venu Gopal Reddy (19104)Document19 pagesDigital Signature: Presented by K.ANITHA (19065) T.DIVYA (19074) T.PAVAN (19082) P.Venu Gopal Reddy (19104)Divya TammineediNo ratings yet
- 1 Pnpki - IntroductionDocument27 pages1 Pnpki - IntroductiongilNo ratings yet
- Authenticity & Integrity of CertificateDocument9 pagesAuthenticity & Integrity of CertificatesurajNo ratings yet
- Basics of Digital Signatures and PKI SDocument4 pagesBasics of Digital Signatures and PKI SPramedicaPerdanaPutraNo ratings yet
- Web Service SecureDocument67 pagesWeb Service SecureMessaraNo ratings yet
- "Digital Signatures Under Information Technology Act 2000 ": Project ReportDocument15 pages"Digital Signatures Under Information Technology Act 2000 ": Project ReportkartikNo ratings yet
- Digital Signature 2Document10 pagesDigital Signature 2vikasNo ratings yet
- PKI is the backbone of many organizations that value cybersecurity resiliency because it enables organizations to automate the process of enforcing data security policies and procedures using digital certificates and public key encryptionDocument1 pagePKI is the backbone of many organizations that value cybersecurity resiliency because it enables organizations to automate the process of enforcing data security policies and procedures using digital certificates and public key encryptionImran AshrafNo ratings yet
- It 4Document4 pagesIt 4nishi jainNo ratings yet
- Department of Electronics and Communication Engineering: Project Phase I PresentationDocument18 pagesDepartment of Electronics and Communication Engineering: Project Phase I PresentationArun ManojNo ratings yet
- Network Security Unit 2Document45 pagesNetwork Security Unit 2Satyam PandeyNo ratings yet
- What Is A Digital SignatureDocument5 pagesWhat Is A Digital SignatureDhruv JainNo ratings yet
- DigitalDocument4 pagesDigitaljithin604No ratings yet
- Digital SignatureDocument13 pagesDigital Signatureradha ramaswamyNo ratings yet
- Information Security Assignement: Public Key InfrastructureDocument5 pagesInformation Security Assignement: Public Key InfrastructureJoel J JoyNo ratings yet
- CHapter - 3netwrokDocument9 pagesCHapter - 3netwrokQusay IsmailNo ratings yet
- Digital Signature: Submitted By: Shrinkhla Sinha-1js17is066 Shivani Beldale-1js17is063 Trishala Kumari-1js17is082Document25 pagesDigital Signature: Submitted By: Shrinkhla Sinha-1js17is066 Shivani Beldale-1js17is063 Trishala Kumari-1js17is082Trishala KumariNo ratings yet
- 000how Digital Signatures Work - DocuSignDocument6 pages000how Digital Signatures Work - DocuSignomar pagliottoNo ratings yet
- Proxykey BrochureDocument4 pagesProxykey BrochureAnvesh JallapallyNo ratings yet
- HCI711s Week 3Document21 pagesHCI711s Week 3gabrieljohannes233No ratings yet
- Acs5 Top6 PaperDocument10 pagesAcs5 Top6 PaperhelloNo ratings yet
- Message Authentication Code and Digital Signatures - Technical ReportDocument33 pagesMessage Authentication Code and Digital Signatures - Technical ReportRam KrishnaNo ratings yet
- Digital SignatureDocument13 pagesDigital Signaturevart1992No ratings yet
- PKI and Digital SignaturesWA.1Document10 pagesPKI and Digital SignaturesWA.1wasirifieNo ratings yet
- Digital Certificates in FortiGate SSL Inspection 1715726898Document102 pagesDigital Certificates in FortiGate SSL Inspection 1715726898Bhishmaraj ThapaliyaNo ratings yet
- Web Services Security and IntegrationDocument13 pagesWeb Services Security and Integrationlaibazahid862No ratings yet
- Securing Email Communication: How to Protect Your Correspondence from Wiretapping Using Free ToolsFrom EverandSecuring Email Communication: How to Protect Your Correspondence from Wiretapping Using Free ToolsNo ratings yet
- Securing .NET Web Services with SSL: How to Protect “Data in Transit” between Client and Remote ServerFrom EverandSecuring .NET Web Services with SSL: How to Protect “Data in Transit” between Client and Remote ServerNo ratings yet
- The Concise Guide to SSL/TLS for DevOpsFrom EverandThe Concise Guide to SSL/TLS for DevOpsRating: 4.5 out of 5 stars4.5/5 (2)
- Group 03 SecurityDocument9 pagesGroup 03 Securitymakangara22No ratings yet
- Group 8 Ism&csnDocument10 pagesGroup 8 Ism&csnmakangara22No ratings yet
- Information System SecurityDocument10 pagesInformation System Securitymakangara22No ratings yet
- Assignment 1 INFORMATION SECURITYDocument7 pagesAssignment 1 INFORMATION SECURITYmakangara22No ratings yet
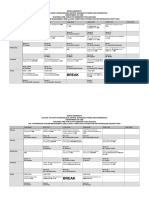
- Timetable V3Document3 pagesTimetable V3makangara22No ratings yet
- Security PresentationDocument12 pagesSecurity Presentationmakangara22No ratings yet
- Lecture4 AccessControlDocument13 pagesLecture4 AccessControlmakangara22No ratings yet
- Lecture3 AutheticationDocument28 pagesLecture3 Autheticationmakangara22No ratings yet
- Lecture 1Document26 pagesLecture 1makangara22No ratings yet
- M4Document105 pagesM4Usama SabirNo ratings yet
- DevLabs Alliance Java For SDETDocument135 pagesDevLabs Alliance Java For SDETShefali SaxenaNo ratings yet
- Annexure - I: - Core Network Deployment - UTRAN Network VT Setup - UTRAN Protocol and Connectivity DiagramDocument5 pagesAnnexure - I: - Core Network Deployment - UTRAN Network VT Setup - UTRAN Protocol and Connectivity DiagramsumitgoraiNo ratings yet
- Capstone Project Proposal Final Student Fillable 1Document5 pagesCapstone Project Proposal Final Student Fillable 1api-665459076No ratings yet
- Process: Add Menu Item Master, Definition, Price: Step ActionDocument7 pagesProcess: Add Menu Item Master, Definition, Price: Step ActionPrince HakimNo ratings yet
- EDITED Introduction To Human Computer InteractionDocument127 pagesEDITED Introduction To Human Computer Interactioncharl calderonNo ratings yet
- TSSN4 - VERSA SD-WAN and SASE OfferingDocument29 pagesTSSN4 - VERSA SD-WAN and SASE OfferingCristian ReyesNo ratings yet
- Long Division With No Remainders Activity Sheets Ver 4Document4 pagesLong Division With No Remainders Activity Sheets Ver 4FonNo ratings yet
- Chapter 2 - Mobile ComputingDocument38 pagesChapter 2 - Mobile ComputingJONAS J JONASNo ratings yet
- Tableau T8UDocument2 pagesTableau T8UvikrantNo ratings yet
- Processor DP ControlDocument44 pagesProcessor DP ControlNonex IstantNo ratings yet
- Module-1: Review Questions: Automata Theory and Computability - 15CS54Document4 pagesModule-1: Review Questions: Automata Theory and Computability - 15CS54ZuviNo ratings yet
- Young Computer Professional: Why Shafay?Document1 pageYoung Computer Professional: Why Shafay?Muhammad ShafayNo ratings yet
- K9N6Sgm-V / K9N6Pgm-Fi / K9N6Pgm-F: Bios DriverDocument4 pagesK9N6Sgm-V / K9N6Pgm-Fi / K9N6Pgm-F: Bios Driverganteliz.23.gaNo ratings yet
- CCSP Exam Cram DOMAIN 3 HandoutDocument139 pagesCCSP Exam Cram DOMAIN 3 HandouttrojanbayaNo ratings yet
- Realize and Design An 8 Bit Serial in and Serial Out Shift Register Using Two 4 Bit Shift RegisterDocument5 pagesRealize and Design An 8 Bit Serial in and Serial Out Shift Register Using Two 4 Bit Shift Registerneha yarrapothuNo ratings yet
- Matrix WMS CORE+ Release Notes 7.1.0Document11 pagesMatrix WMS CORE+ Release Notes 7.1.0marialuz1517No ratings yet
- Nikto SheetsDocument1 pageNikto Sheetselephone P2000No ratings yet
- Goals of Software Design: Design Faces Many Challenges To Produce A Good Product, E.G. Shifting RequirementsDocument51 pagesGoals of Software Design: Design Faces Many Challenges To Produce A Good Product, E.G. Shifting Requirementsrdx4cs1No ratings yet
- Operating System OS Compiled Notes 06CS53Document160 pagesOperating System OS Compiled Notes 06CS53Srinath Gm G MNo ratings yet
- 1.3 Future Scaling: Where Systems and Technology Meet: 25 Digest of Technical PapersDocument5 pages1.3 Future Scaling: Where Systems and Technology Meet: 25 Digest of Technical Papersck maitiNo ratings yet
- Service Manual: Sigma Air Manager 16/8Document192 pagesService Manual: Sigma Air Manager 16/8Evandro Jva compressoresNo ratings yet
- 1Z0-100 Oracle: Number: 1Z0-100 Passing Score: 800 Time Limit: 120 MinDocument22 pages1Z0-100 Oracle: Number: 1Z0-100 Passing Score: 800 Time Limit: 120 MinFabio Steve Gutierrez LealNo ratings yet
- AZ 304 QuestionsDocument6 pagesAZ 304 QuestionsUdit DharniNo ratings yet
- MCADDocument24 pagesMCADAyushi SavaniNo ratings yet
- DWH MCQ 2015 Chap-1to4Document3 pagesDWH MCQ 2015 Chap-1to4John DevisNo ratings yet
- SDLCDocument11 pagesSDLCRAVITEJA TELUGARANo ratings yet
- Class 4 Sample Questions: International Informatics Olympiad - IIO 2019Document1 pageClass 4 Sample Questions: International Informatics Olympiad - IIO 2019Reyansh JainNo ratings yet
- Technology - CrosswordsDocument2 pagesTechnology - CrosswordsRcl MonteiroNo ratings yet