Professional Documents
Culture Documents
Chapter 9 New
Chapter 9 New
Uploaded by
Mr. Omesh Wadhwani0 ratings0% found this document useful (0 votes)
53 views16 pagesThe document discusses various techniques for analyzing digital evidence, including capturing memory and hard drive images using forensic imaging tools. It also describes analyzing RAM and hard drives using tools like Volatility and WinHex, investigating file systems and artifacts using Autopsy, and tracing emails. The role of the forensic analyst is to acquire evidence, perform analysis following standard procedures, and prepare a report of their examination and conclusions.
Original Description:
Original Title
Chapter_9_new
Copyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThe document discusses various techniques for analyzing digital evidence, including capturing memory and hard drive images using forensic imaging tools. It also describes analyzing RAM and hard drives using tools like Volatility and WinHex, investigating file systems and artifacts using Autopsy, and tracing emails. The role of the forensic analyst is to acquire evidence, perform analysis following standard procedures, and prepare a report of their examination and conclusions.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
0 ratings0% found this document useful (0 votes)
53 views16 pagesChapter 9 New
Chapter 9 New
Uploaded by
Mr. Omesh WadhwaniThe document discusses various techniques for analyzing digital evidence, including capturing memory and hard drive images using forensic imaging tools. It also describes analyzing RAM and hard drives using tools like Volatility and WinHex, investigating file systems and artifacts using Autopsy, and tracing emails. The role of the forensic analyst is to acquire evidence, perform analysis following standard procedures, and prepare a report of their examination and conclusions.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
You are on page 1of 16
Cyber Forensics
Dejey| Murugan
© Oxford University Press 2018. All rights reserved.
Chapter 9
Analysis of Digital Evidence
© Oxford University Press 2018. All rights reserved.
Outline
• Introduction to Analysis of Digital Evidence
• Capturing of Forensic Copy of Memory and Hard
Drive with Toolkit Forensic Imager
• RAM Analysis with Volatility
• Analysing Hard Drive with WinHex
• Working with Autopsy
• Email Tracking and Tracing
• Role of Forensic Analyst in Analysis
© Oxford University Press 2018. All rights reserved.
Introduction to Analysis of Digital
Evidence
• Analysis of Digital Evidence: Identifying, preserving,
interpreting, and documenting the evidence
recovered for presentation in a civil or criminal court.
© Oxford University Press 2018. All rights reserved.
Capturing of Forensic Copy of Memory
and Hard Drive with Toolkit Forensic
Imager
• Capturing Main Memory using FTK Imager
• Capturing Hard Drive
• Acquiring memory dump
• Acquiring memdump.mem in D:
• Acquiring pagefile.sys in D:
• Acquiring memory in D:
• Image Summary
• Acquiring forensic copy of hard drive in E:
• Image summary shown by FTK Imager as directory listing
© Oxford University Press 2018. All rights reserved.
RAM Analysis with Volatility
• imageinfo
• pslist
• pstree
• malfind
• malfind plugin
• cmdscan
• netscan
© Oxford University Press 2018. All rights reserved.
Analysing Hard Drive with
WinHex
Acquiring Forensic Copy of Drive
• Open disk from Tools menu
• Selecting drive to obtain forensic copy
• Choosing Create Disk Image from File menu
• Specifying file format of forensic copy and
destination
Computing Hash
• Selecting Compute Hash
• Computing hash value for the drive
© Oxford University Press 2018. All rights reserved.
Analysing Hard Drive with
WinHex (Cont…)
Analysing Hard Disk
• Selecting Open Disk
• Choosing drive to be analysed
Analysing Slack Space and Free Space
• Selecting the Slack Space location
• Selecting the Gather Free Space
File Carving
• Selecting the Tools menu
• Choosing Disk Tools and then File Recovery by Type
from the pop-up menu.
• Files types that can be carved will be listed.
© Oxford University Press 2018. All rights reserved.
Working with Autopsy
• Adding a data source (image, local disk, logical files)
• Creating a case
• Adding a data source
• Ingest modules
• Analysis basics
• Ingest inbox
• Timeline (beta)
• Reporting
© Oxford University Press 2018. All rights reserved.
Working with Autopsy (Cont…)
Example Use Cases
• Web artifacts
• Known bad hash files
• Media – images and videos
Analysis of Deleted Files with Autopsy
• Creating new case
• Entering new case information
• Entering additional information
• Selecting type of data source to add
© Oxford University Press 2018. All rights reserved.
Working with Autopsy (Cont…)
• Selecting data source
• Configuring ingest modules
• Adding data source
• Display of logical disk in table
• Status of add data source
• Listing of deleted files
© Oxford University Press 2018. All rights reserved.
Email Tracking and Tracing
Email Tracking
• Adding Mail Tracker to Gmail account
• Composing email for recipient
• Tracking Status
• Sent email status
• Number of times mail read
Email Tracing
• Selecting Show Original to acquire email header
© Oxford University Press 2018. All rights reserved.
Email Tracking and Tracing
(Cont…)
• Email Tracking with emailTracker Pro
• Clicking the Trace Headers option.
• The radio button Trace an Email I have Received is chosen.
• The email header is copy–pasted.
• Then the Trace button is clicked. The result of Trace
Header is shown.
• If the radio button Look Up Network Responsible for an
Email Address is chosen, an email address is given and the
resultant network addresses are displayed.
© Oxford University Press 2018. All rights reserved.
Email Tracking and Tracing
(Cont…)
• Email Tracing with Online EMailTracer
• Email header of the recipient is copied and pasted.
• Clicking the Start Tracing button.
© Oxford University Press 2018. All rights reserved.
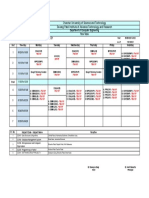
Role of Forensic Analyst in
Analysis
Format of requisition sent to forensic lab for analysis
© Oxford University Press 2018. All rights reserved.
Role of Forensic Analyst in
Analysis (Cont…)
Role of Forensic Analyst
• Acquire a forensic copy of the suspected storage media.
• Compute hash.
• Perform live forensics.
• Examine slack space/free space.
• Check for deleted files.
• Look for artifacts.
• Trace email.
• Prepare the report of the forensic examination.
• Represents opinions.
• Draws a conclusion of the case.
© Oxford University Press 2018. All rights reserved.
You might also like
- Project Report On Virtual Assistant SubmDocument28 pagesProject Report On Virtual Assistant SubmParmod Yadav100% (1)
- Winidea Build 9.17.172.0.109652 Test Report: Renesas Rh850Document2 pagesWinidea Build 9.17.172.0.109652 Test Report: Renesas Rh850mohammedNo ratings yet
- LO - 2 - Data Capture and Memory ForensicsDocument51 pagesLO - 2 - Data Capture and Memory ForensicsisraaNo ratings yet
- Lecture 13 - Comprehensive Guide On Autopsy Tool (Windows)Document47 pagesLecture 13 - Comprehensive Guide On Autopsy Tool (Windows)htoothit781No ratings yet
- 6 Analysis & Validation Xid-10936710 2Document34 pages6 Analysis & Validation Xid-10936710 2Zoey TanNo ratings yet
- Data AcquisitionDocument29 pagesData Acquisitionيُ يَNo ratings yet
- Cyber ForensicsDocument29 pagesCyber ForensicsunnamedNo ratings yet
- Module 2 Webinar Slides - PowerpointDocument24 pagesModule 2 Webinar Slides - PowerpointEmmanuelNo ratings yet
- 3 Data Acquisition - Xid-10710319 - 2Document32 pages3 Data Acquisition - Xid-10710319 - 2Zoey TanNo ratings yet
- Dr. Phil Nyoni: Digital Forensics Lecture 2: Acquiring Digital Evidence July 2021Document56 pagesDr. Phil Nyoni: Digital Forensics Lecture 2: Acquiring Digital Evidence July 2021QomindawoNo ratings yet
- Practical No 01 Title: Working With Windows Forensic Toolkit (Accessdata FTK) TheoryDocument14 pagesPractical No 01 Title: Working With Windows Forensic Toolkit (Accessdata FTK) TheoryyatharthNo ratings yet
- Understanding Computer InvestigationsDocument64 pagesUnderstanding Computer InvestigationsLillian KobusingyeNo ratings yet
- Guide To Computer Forensics and Investigations Fourth EditionDocument56 pagesGuide To Computer Forensics and Investigations Fourth EditionMD HOSSAINNo ratings yet
- CF Unit 3Document151 pagesCF Unit 3saket bntuNo ratings yet
- 04-OS and Multimedia ForensicsDocument189 pages04-OS and Multimedia ForensicsMohammed Lajam100% (1)
- Guide To Computer Forensics and Investigations Fourth EditionDocument58 pagesGuide To Computer Forensics and Investigations Fourth EditionMr J Briso Beclay Bell ITNo ratings yet
- Identity Management SystemDocument53 pagesIdentity Management SystemSanthosh Kumar PNo ratings yet
- Data AcquisitionDocument31 pagesData AcquisitionexcitekarthikNo ratings yet
- Common Forensics ToolsDocument10 pagesCommon Forensics ToolsNermani RajakulendramNo ratings yet
- Computer Security Professionals and IT PersonnelDocument20 pagesComputer Security Professionals and IT PersonnelFaim HasanNo ratings yet
- CH 02 I CDocument68 pagesCH 02 I Cbalajinaik07No ratings yet
- Computer Forensic Investigation: Learnhacking - OnlineDocument14 pagesComputer Forensic Investigation: Learnhacking - OnlineDeep ChandrakarNo ratings yet
- CH 04 I CDocument93 pagesCH 04 I Cbalajinaik07No ratings yet
- Lec 2Document23 pagesLec 2aldd63502No ratings yet
- Digital Forensic Analysis Lab ExerciseDocument3 pagesDigital Forensic Analysis Lab Exercisealshdadyfhmy398100% (1)
- Akuisisi Data: Forensic ComputerDocument76 pagesAkuisisi Data: Forensic ComputerDarmaNo ratings yet
- DF Unit 2 My NotesDocument18 pagesDF Unit 2 My NotesRachit AnandNo ratings yet
- Full SlidesDocument86 pagesFull SlidessilNo ratings yet
- 03 Data AcquisitionDocument91 pages03 Data AcquisitionMohammed LajamNo ratings yet
- 39 - Physical Memory ForensicsDocument53 pages39 - Physical Memory Forensicssmithm007No ratings yet
- Memory Forensic in Incident ResponseDocument74 pagesMemory Forensic in Incident ResponseSunidhi Jain100% (1)
- EHDF Ut2Document12 pagesEHDF Ut2Faizal KhanNo ratings yet
- CH 09Document56 pagesCH 09debbytaNo ratings yet
- A Presentation ON: Forensics ToolDocument31 pagesA Presentation ON: Forensics ToolFabián MirandaNo ratings yet
- Lecture 5Document21 pagesLecture 5omardshycNo ratings yet
- Guide To Computer Forensics and Investigations Fourth EditionDocument67 pagesGuide To Computer Forensics and Investigations Fourth EditionSanthosh Kumar PNo ratings yet
- Antivirus Scan Effects On Last Accessed Times: Charles Yarbrough CERT Coordination Center January 28, 2011Document23 pagesAntivirus Scan Effects On Last Accessed Times: Charles Yarbrough CERT Coordination Center January 28, 2011Chuck YarbroughNo ratings yet
- File System Forensics: Dr. N.B. VenkateswarluDocument42 pagesFile System Forensics: Dr. N.B. Venkateswarluvenkat_ritchNo ratings yet
- EnCase Portable Brochure 9-11-13-WebreadyDocument6 pagesEnCase Portable Brochure 9-11-13-WebreadydiegoNo ratings yet
- Memory ForensicsDocument61 pagesMemory ForensicsaaaaNo ratings yet
- Keamanan Jaringan Komputer Pertemuan 2 - Information GatheringDocument33 pagesKeamanan Jaringan Komputer Pertemuan 2 - Information GatheringAditya Wahyu SNo ratings yet
- Lecture 9 Data Analysis and ValidationDocument30 pagesLecture 9 Data Analysis and Validationku.hariamuNo ratings yet
- Chapter 2Document30 pagesChapter 2Dr. Myat Mon KyawNo ratings yet
- Forensics ExamDocument5 pagesForensics ExamzaphneathpeneahNo ratings yet
- Sec C DFDocument38 pagesSec C DFoffsechouseNo ratings yet
- Forensic Secrets SampleDocument28 pagesForensic Secrets Samplerj3301a0% (2)
- Chapter 2 Intro To Digital ForensicsDocument25 pagesChapter 2 Intro To Digital ForensicsKrishn kumarNo ratings yet
- BFC ProjectDocument18 pagesBFC Projectsudha gilmoreNo ratings yet
- Dr. Phil Nyoni: Digital Forensics Lecture 6: Forensics Tools July 2021Document40 pagesDr. Phil Nyoni: Digital Forensics Lecture 6: Forensics Tools July 2021QomindawoNo ratings yet
- Computer Forensics - Lesson 02Document30 pagesComputer Forensics - Lesson 02Muisyo JamesNo ratings yet
- DSP Cat 1Document107 pagesDSP Cat 1R B SHARANNo ratings yet
- Current Computer Forensics ToolsDocument65 pagesCurrent Computer Forensics Toolsjaya prasannaNo ratings yet
- Digital Forensics (Data Acquisition and Hashing)Document48 pagesDigital Forensics (Data Acquisition and Hashing)Dipenker Dey100% (1)
- EEE2139 Lecture 5Document26 pagesEEE2139 Lecture 5Ali UmaliNo ratings yet
- CP4P Week3 Course Preview TopicsDocument33 pagesCP4P Week3 Course Preview TopicsPresiNo ratings yet
- Internet Forensics and Cyber Security: Unit 3Document55 pagesInternet Forensics and Cyber Security: Unit 3rawabi majdiNo ratings yet
- 03-Csirt Operation FirstDocument77 pages03-Csirt Operation FirstPredrag SkundricNo ratings yet
- Foss Digital ForensicsDocument33 pagesFoss Digital ForensicstheamitannaNo ratings yet
- Mark McKinnon - Plug Me in Renzik, Autopsy Plugins Now and in The FutureDocument45 pagesMark McKinnon - Plug Me in Renzik, Autopsy Plugins Now and in The FutureAndres PardalNo ratings yet
- SCI4201 Lecture 7 - Forensics ToolsDocument53 pagesSCI4201 Lecture 7 - Forensics Toolsonele mabhenaNo ratings yet
- CH 04Document13 pagesCH 04balajinaik07No ratings yet
- Q1V3Document3 pagesQ1V3Marwan HelalNo ratings yet
- Summary of Steps To Setup SQL Server Lab Environment - Mac - v1Document5 pagesSummary of Steps To Setup SQL Server Lab Environment - Mac - v1Chizzyen ShadedNo ratings yet
- Ap1200 User GuideDocument14 pagesAp1200 User GuideLaur IriNo ratings yet
- IPU OS Unit 2 NotesDocument123 pagesIPU OS Unit 2 NotesMikasa AckermanNo ratings yet
- Namiq's ResumeDocument1 pageNamiq's ResumeNamig IsmayilovNo ratings yet
- Radar System Overview: Specialists in Defence & Aerospace SystemsDocument27 pagesRadar System Overview: Specialists in Defence & Aerospace SystemsGMVSrinivasaNo ratings yet
- Questions: Practice SetDocument4 pagesQuestions: Practice SetharshithaNo ratings yet
- 1346346Document10 pages1346346Neil KhanNo ratings yet
- Charotar University of Science and Technology Devang Patel Institute of Advance Technology and ResearchDocument1 pageCharotar University of Science and Technology Devang Patel Institute of Advance Technology and ResearchNaman GhevariyaNo ratings yet
- Problem Statement SubhanDocument5 pagesProblem Statement SubhanTech UniverseNo ratings yet
- AWS Technical Essentials: Course DescriptionDocument3 pagesAWS Technical Essentials: Course DescriptionEriNo ratings yet
- Epson EcoTank L3210 - L3250Document2 pagesEpson EcoTank L3210 - L3250Maret AriksNo ratings yet
- Micron 4 - 8Gb DDR3L 240pinDocument18 pagesMicron 4 - 8Gb DDR3L 240pinxogini3958No ratings yet
- MDM-SGG Business User Guide v2 2 0 2Document185 pagesMDM-SGG Business User Guide v2 2 0 2Aditya DasNo ratings yet
- Iot Questions For AssignmentsDocument1 pageIot Questions For AssignmentsKumar ChaitanyaNo ratings yet
- Abap NW7 0Document6 pagesAbap NW7 0Amit VermaNo ratings yet
- Data Types, Variables, Type Conversion and Casting, ArraysDocument38 pagesData Types, Variables, Type Conversion and Casting, ArraysGanesh NelluriNo ratings yet
- Class 12 (IP) PT. 01 Answer Key2024-25Document3 pagesClass 12 (IP) PT. 01 Answer Key2024-25kumbharkedar777No ratings yet
- Ats Test Taker Guide India 2022-23Document10 pagesAts Test Taker Guide India 2022-23krishnabijuNo ratings yet
- ACS380, 0.37 To 22 KW: ABB Drives For CranesDocument2 pagesACS380, 0.37 To 22 KW: ABB Drives For CranesDev ShahNo ratings yet
- iGW Brochure 2021Document4 pagesiGW Brochure 2021Lâm Trần HữuNo ratings yet
- 2016 Book SecondaryAnalysisOfElectronicH PDFDocument435 pages2016 Book SecondaryAnalysisOfElectronicH PDFSharon DhillonNo ratings yet
- TSG SystemDocument26 pagesTSG SystemNouraldin OwdaNo ratings yet
- OSI Model & TCP IP ModelDocument18 pagesOSI Model & TCP IP ModelAravind SNo ratings yet
- VAES17 02 Ethernet-Journey-JLR Bath ShindeDocument20 pagesVAES17 02 Ethernet-Journey-JLR Bath ShindeAbii JiThNo ratings yet
- Harmony iPC - HMIPWC7D0E01Document6 pagesHarmony iPC - HMIPWC7D0E01Elvis SilvaNo ratings yet
- DIR-2150 ManualDocument153 pagesDIR-2150 ManualGuleBamseNo ratings yet
- RRU5258 Hardware Description (15) (PDF) - ENDocument41 pagesRRU5258 Hardware Description (15) (PDF) - ENkuzdubaev rustamNo ratings yet