Professional Documents
Culture Documents
Information Systems
Information Systems
Uploaded by
sabam9760 ratings0% found this document useful (0 votes)
3 views15 pagesThe document discusses security issues related to information systems. It covers areas like vulnerabilities in information systems from malware and hacking, tools to safeguard information like firewalls and encryption, and the importance of security and controls for businesses. Specific topics covered include types of malware, hacking methods, security controls at different levels, and the value of computer forensics for legal purposes.
Original Description:
Copyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentThe document discusses security issues related to information systems. It covers areas like vulnerabilities in information systems from malware and hacking, tools to safeguard information like firewalls and encryption, and the importance of security and controls for businesses. Specific topics covered include types of malware, hacking methods, security controls at different levels, and the value of computer forensics for legal purposes.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
0 ratings0% found this document useful (0 votes)
3 views15 pagesInformation Systems
Information Systems
Uploaded by
sabam976The document discusses security issues related to information systems. It covers areas like vulnerabilities in information systems from malware and hacking, tools to safeguard information like firewalls and encryption, and the importance of security and controls for businesses. Specific topics covered include types of malware, hacking methods, security controls at different levels, and the value of computer forensics for legal purposes.
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
You are on page 1of 15
Faculty of Computing and Informatics
Business Management Information Systems –
BMC511S
Lesson 4 – Securing information Systems, Ethical & Social issues in
Information Systems
03 May 2021
Faculty of Computing and Informatics
Security of information systems
1. An introduction to the security of information systems
2. Areas of vulnerabilities in information systems
3. Hackers and computer crime
4. Information systems controls
5. Tools and technologies for safeguarding information
resources
6. The business value of security and control in IS
Faculty of Computing and Informatics
An introduction to the security of information systems
• Security – the policies, procedures and technical measures used to
prevent unauthorized access, alteration, theft or physical damage to
information systems
• Controls are the methods, policies and organisational procedures that
ensure the safety of an organisation’s assets, the accuracy and
reliability of its records and operational adherence to management
standards
Faculty of Computing and Informatics
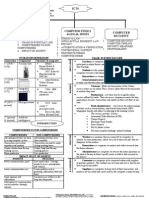
Areas of vulnerabilities in IS – malicious software
• Malware – Malicious software programs, e.g. computer viruses, worms,
Trojan horses
• Computer virus – rogue software that attaches itself to other software
programs or data files in order to be executed, e.g. display message, destroy
data, clog computer
• Worms – computer programs that copy themselves from one computer to
other computers over the network. They don’t attack other programs, but
destroy data and programs to halt operations
• Trojan horse – software program that does not replicate like the virus but
opens the way for malicious code to be introduced e.g. steal login details
Faculty of Computing and Informatics
Other areas of vulnerabilities in information systems
• Internet vulnerability – Hackers can intercept conversations, flood servers with bogus
traffic
• Wireless security challenges – e.g. radio frequency bands are easy to scan; hackers
use tools to detect and monitor unprotected networks
• SQL injection attacks – take advantage of vulnerabilities in poorly-coded web
application software to introduce malicious programs
• Ransomware – takes control of computers and users have to pay to regain access
• Spyware – software installs themselves on computers to monitor web surfing activity
• Keyloggers – records every keystroke made on a computer to steal passwords,
personal information, etc
Faculty of Computing and Informatics
Hackers and computer crime
• A hacker is an individual who intends to gain unauthorized access to a computer
system by finding weaknesses in the security of the system
• Spoofing: Hackers hide their true identity by using fake email addresses or
masquerading as someone else, e.g. direct customers to fake web sites
• Sniffer: a type of eavesdropping program that monitors information travelling over a
network.
• Denial-of-service-attacks: hackers flood a server with requests for services/email that
crash the network
• Computer crime – any violations of criminal law that involve a knowledge of
computer technology for perpetration, investigation or prosecution
Faculty of Computing and Informatics
Hackers and computer crime
• Identity theft: an impostor obtains key pieces of personal information such as ID,
driver’s license, credit card details
• Phishing: a form of spoofing involving setting up websites or sending email messages
that look like those of legitimate businesses to ask users for confidential personal
data
• Evil twins: wireless networks that pretend to offer trustworthy WiFi connections to
the internet, e.g. in airport lounges or hotels to capture passwords
• Pharming: redirects users to a bogus web page, even when the individual types the
correct web age address into their web browser
Faculty of Computing and Informatics
Hackers and computer crime
• Click fraud: when you click on an ad on a search engine, the click directs the
potential buyers to a company website. The company then pays the search
engine for the service. When the click occurs and the customer is not
directed to the company’s website, then the company pays the search engine
for nothing
• Cyber warfare: is a state-sponsored activity designed to cripple another state
or nation by penetrating its computers or networks for the purpose of
causing damage and disruption
• Internal threats from employees: employees have access to privileged
information; employees forget passwords or allow co-workers to use them;
Faculty of Computing and Informatics
Information systems controls
• General controls – the design, security and use of computer programs and
the security of data files throughout an organisation’s IT infrastructure
• Software controls – monitor the use of systems software and prevent
unauthorised access to software programs, systems software and computer
programs
• Hardware controls – ensure computer hardware is physically secure and
check for equipment malfunction
• Computer operations controls – programmed procedures are consistently
and correctly applied to the storage and processing of data, e.g. backup and
recovery procedures
Faculty of Computing and Informatics
Information systems controls
• Data security controls: ensure that valuable business data files are not
subject to unauthorized access , change or destruction while they are is use
or storage
• Implementation controls: Audit the systems development process at various
points to ensure that the process is properly controlled and managed
• Administrative controls: Formalise standards, rules, procedures and control
disciplines to ensure that the organisation’s general and application controls
are properly executed and enforced
Faculty of Computing and Informatics
Information systems controls – application controls
• Application controls are specific controls that are unique to each
computerized application
• Input controls – check data for accuracy and completeness when they enter
the system
• Processing controls – establish that the data are complete and accurate
during updating
• Output controls – ensure that the results of computer processing are
accurate, complete and properly distributed
Faculty of Computing and Informatics
Tools and technologies for safeguarding information resources
• Identity management and authentication – process of keeping track of all
users and their system privileges, assigning each user a unique digital identity
for accessing each system e.g. password, biometric identification, smart card
• Firewalls – prevent unauthorized users from accessing private networks. It is
a combination of hardware and software that controls the flow of incoming
and outgoing network traffic
• Intrusion detection systems – full-time monitoring tools are placed at the
most vulnerable points of networks to detect and deter intruders – sends an
alarm if it finds a suspicious event
Faculty of Computing and Informatics
Tools and technologies for safeguarding information resources
• Anti-virus and anti-spyware software – prevents, detects and removes
malware, including viruses, worms, Trojan horses, spyware
• Unified Threat Management (UTM) – a single appliance of various security
tools including firewalls , virtual private networks (VPNs), intrusion-detection
systems and web filtering and anti-spam software
• Encryption – transforming text or data into cipher text that cannot be read by
anyone other than the sender and receiver. Data is encrypted using an
encryption key
Faculty of Computing and Informatics
The business value of security and control in IS
• There is valuable information assets to protect, e.g. confidential information
about taxes, medical records and financial assets
• Inadequate security and control may result in serious legal liability and costly
litigation
• Computer forensics is the scientific collection, examination, authentication,
preservation and analysis of data held on or retrieved from computer storage
media in such a way that the information is used as evidence in a court of law
13 Storch Street T: +264 61 207 2258
Private Bag 13388 F: +264 61 207 9258
Windhoek E: fci@nust.na
NAMIBIA W: www.nust.na
Faculty of Computing and Informatics
Thank You.
You might also like
- 8.securing Information SystemsDocument25 pages8.securing Information SystemsAli AslamNo ratings yet
- Internet and Security Final Term IT EraDocument62 pagesInternet and Security Final Term IT EraMark joseph Tapere100% (1)
- Unit VDocument36 pagesUnit VBijay PoudelNo ratings yet
- Security of Information SystemDocument30 pagesSecurity of Information SystemVishal PatelNo ratings yet
- Security and Ethical Challenges: UNIT-5Document53 pagesSecurity and Ethical Challenges: UNIT-5Ram KumarNo ratings yet
- Security & Ethical ChallengesDocument4 pagesSecurity & Ethical ChallengesParvind AgarwalNo ratings yet
- Ch11 DropboxDocument19 pagesCh11 DropboxJanes VuNo ratings yet
- Security and Control MISDocument20 pagesSecurity and Control MISJaipuneet Arora0% (1)
- Chapter 3 Komputer Masyarakat Dan Etika Profesi English PDFDocument47 pagesChapter 3 Komputer Masyarakat Dan Etika Profesi English PDFElly JongNo ratings yet
- MIS-Unit 5Document48 pagesMIS-Unit 5ghimirebob1998No ratings yet
- Securing Information Systems Securing Information SystemsDocument45 pagesSecuring Information Systems Securing Information SystemsHenry MagdayNo ratings yet
- Protecting Information ResourcesDocument44 pagesProtecting Information ResourceshtethtethlaingNo ratings yet
- Network Security FUndamentalsDocument22 pagesNetwork Security FUndamentalspetercoolish108No ratings yet
- Unit1 PDFDocument49 pagesUnit1 PDFSandeep PotnuruNo ratings yet
- MIS Assignmnet by Rakibul IslamDocument15 pagesMIS Assignmnet by Rakibul IslamMD Arafat RahmanNo ratings yet
- Chapter 8Document13 pagesChapter 8Olympus IncNo ratings yet
- Chapter 4 ISDocument2 pagesChapter 4 ISmalena muloniaNo ratings yet
- Presentation MISDocument32 pagesPresentation MISMuhammad AdzikriNo ratings yet
- Unit 5Document58 pagesUnit 5KRISHNA TEJANo ratings yet
- Module 5 Information SecurityDocument54 pagesModule 5 Information SecurityzaphneathpeneahNo ratings yet
- Computer and Internet CrimeDocument51 pagesComputer and Internet CrimeClara PanggabeanNo ratings yet
- Mis Chap 8: Securing Information SystemDocument36 pagesMis Chap 8: Securing Information SystemDr Roy ChingNo ratings yet
- Lesson 8Document33 pagesLesson 8Aida NatashaNo ratings yet
- Chap 1Document3 pagesChap 1mx2209No ratings yet
- Securing Information SystemsDocument52 pagesSecuring Information SystemsrajavikramarkaNo ratings yet
- It Security Procedures and Guidelines: Adrija SenDocument33 pagesIt Security Procedures and Guidelines: Adrija SenSaket AgarwalNo ratings yet
- L3 Computer Crime and Computer Crime ActDocument47 pagesL3 Computer Crime and Computer Crime ActLing Siong TeckNo ratings yet
- Lesson 3 Privacy and SecurityDocument31 pagesLesson 3 Privacy and SecurityrltmorenoNo ratings yet
- Dersnot 2458 1709926898Document41 pagesDersnot 2458 1709926898sudenur77ozcanNo ratings yet
- Itm Mod6Document17 pagesItm Mod6atisbhai.6969No ratings yet
- Unit 2 Security For E-BusinessDocument38 pagesUnit 2 Security For E-BusinessKavitha PalaniNo ratings yet
- Information Security1Document39 pagesInformation Security1Harshad SawantNo ratings yet
- Unit1 - Introduction and Unit 7 Information SecurityDocument150 pagesUnit1 - Introduction and Unit 7 Information Securityprototypes6341No ratings yet
- Introduction To Computer Security-1Document41 pagesIntroduction To Computer Security-1severinmsangiNo ratings yet
- 3 PPT - CopyDocument26 pages3 PPT - CopyDurga Prasad SmartNo ratings yet
- Establishing A Framework For Security and ControlDocument34 pagesEstablishing A Framework For Security and ControlNoppon SETTASATIENNo ratings yet
- Submitted By:: Brijesh Patel Roll No 19Document11 pagesSubmitted By:: Brijesh Patel Roll No 19Primal PatelNo ratings yet
- Unit 7Document19 pagesUnit 7Kshitiz OjhaNo ratings yet
- Unit 1 Introduction To Computer Security: COSC 4035Document47 pagesUnit 1 Introduction To Computer Security: COSC 4035shifaratesfayeNo ratings yet
- Securing Information SystemsDocument42 pagesSecuring Information SystemsAziz AziziNo ratings yet
- ICS Lecture 8Document29 pagesICS Lecture 8MINI DHABANo ratings yet
- Software Security: Komal BasharatDocument27 pagesSoftware Security: Komal BasharatAlina PariNo ratings yet
- Security in MISDocument23 pagesSecurity in MIShimanshuNo ratings yet
- Security, Privacy, and Ethical Issues in Information SystemsDocument16 pagesSecurity, Privacy, and Ethical Issues in Information SystemsAntonyNo ratings yet
- SCI4201 Lecture 1 - OverviewDocument65 pagesSCI4201 Lecture 1 - Overviewn02019697mNo ratings yet
- Unit 5 CSDocument44 pagesUnit 5 CSprathamesh.pagale.aids.2021No ratings yet
- Securing Information SystemsDocument26 pagesSecuring Information SystemsArnold DsouzaNo ratings yet
- Lect 7Document67 pagesLect 7shirto cubherNo ratings yet
- Unit NineDocument59 pagesUnit NineManag LimbuNo ratings yet
- COSC 6301 - Computer Security Threats - and - VulnerabilitiesDocument52 pagesCOSC 6301 - Computer Security Threats - and - VulnerabilitiesmailtosiscoNo ratings yet
- Cyber SequrityDocument14 pagesCyber SequrityMd AadilNo ratings yet
- Security and Ethical Issues in MIS (Done)Document24 pagesSecurity and Ethical Issues in MIS (Done)Maham TariqNo ratings yet
- Unit-3 Cyber Security PrabhuDocument106 pagesUnit-3 Cyber Security PrabhuNivedhithaNo ratings yet
- Towards Safe and Secure CyberspaceDocument25 pagesTowards Safe and Secure Cyberspacearihant6087No ratings yet
- It Application Tools in Business: ITEC 5 - Lecture 1Document19 pagesIt Application Tools in Business: ITEC 5 - Lecture 1JabonJohnKennethNo ratings yet
- Summary Chapter 8 Securing Informatin SystemDocument6 pagesSummary Chapter 8 Securing Informatin SystemTasha NurafifahNo ratings yet
- Ais ReportDocument5 pagesAis ReportJoyce EguiaNo ratings yet
- SecurityDocument6 pagesSecurityHoodFigaNo ratings yet
- SPGUNIT1Document59 pagesSPGUNIT1DINESH GAWANDENo ratings yet
- Cybersecurity and Ethical Hacking: Exploring the Dark Art of Ethical Hacking and Penetration TestingFrom EverandCybersecurity and Ethical Hacking: Exploring the Dark Art of Ethical Hacking and Penetration TestingNo ratings yet
- Routledge International Handbook of PartDocument1 pageRoutledge International Handbook of Partsabam976No ratings yet
- Schultz Et Al 2015 Adaptive Governance Ecosystem Management and Natural CapitalDocument6 pagesSchultz Et Al 2015 Adaptive Governance Ecosystem Management and Natural Capitalsabam976No ratings yet
- Sustainability 03 00937Document18 pagesSustainability 03 00937sabam976No ratings yet
- Evaluating PGIS McCall NRMDocument18 pagesEvaluating PGIS McCall NRMsabam976No ratings yet
- Natural Eco-Information Management System Using GIS in Kang-WhaDocument8 pagesNatural Eco-Information Management System Using GIS in Kang-Whasabam976No ratings yet
- ORCID Poster - LinksDocument1 pageORCID Poster - Linkssabam976No ratings yet
- Business Intelligence, Analytics, and Data ScienceDocument53 pagesBusiness Intelligence, Analytics, and Data Sciencesabam976No ratings yet
- JdlmsDocument12 pagesJdlmschristianNo ratings yet
- AdewDocument5 pagesAdewJordy RiansyahNo ratings yet
- R2023 Sem 2Document81 pagesR2023 Sem 2Krish ShivaNo ratings yet
- Cloud Whitebook Cloud White BookDocument60 pagesCloud Whitebook Cloud White BookeevengNo ratings yet
- Cirriculum Vittae KanchanaDocument5 pagesCirriculum Vittae Kanchanaraaman100% (1)
- VDP User Manual PublicDocument10 pagesVDP User Manual PublicFiza. MNorNo ratings yet
- Distributed Multimedia SystemsDocument38 pagesDistributed Multimedia SystemsMr.T.Vijayakumar Assistant ProfessorNo ratings yet
- DCA6101-Unit 12-Operating System ConceptsDocument19 pagesDCA6101-Unit 12-Operating System ConceptsJust SaaNo ratings yet
- Notes DFDocument18 pagesNotes DFJayesh PatilNo ratings yet
- The Data Whisperer Master Data As The Foundation of Digital TransformationDocument40 pagesThe Data Whisperer Master Data As The Foundation of Digital Transformationcsv92No ratings yet
- Configuring Kafka For High ThroughputDocument11 pagesConfiguring Kafka For High Throughputnilesh86378No ratings yet
- Bug Spotter (AutoRecovered)Document68 pagesBug Spotter (AutoRecovered)My AllNo ratings yet
- WS1 IOS PlatformDocument103 pagesWS1 IOS PlatformChaima MedhioubNo ratings yet
- FRC Best Practice ProcessDocument43 pagesFRC Best Practice ProcessbilalghaznaviNo ratings yet
- IBM Common Data ProviderDocument44 pagesIBM Common Data ProviderBurhan MalikNo ratings yet
- Developer: Introduction To HTML, CSS, and JavascriptDocument42 pagesDeveloper: Introduction To HTML, CSS, and JavascriptFadhlan HidayatulllahNo ratings yet
- EIM in Digital MediaDocument16 pagesEIM in Digital MediashamikchakNo ratings yet
- Software/System Basic Uses Advantage/S Disadvantage/S: 1. Project Management Software (PMS)Document2 pagesSoftware/System Basic Uses Advantage/S Disadvantage/S: 1. Project Management Software (PMS)Clarise JimenezNo ratings yet
- SAS 9.2 Companion For UNIX EnvironmentsDocument518 pagesSAS 9.2 Companion For UNIX EnvironmentsPuli SreenivasuluNo ratings yet
- Building An Intrusion Detection System Using A FilterDocument3 pagesBuilding An Intrusion Detection System Using A FilterChetan RajuNo ratings yet
- CRNM - The International Supply of Tertiary Education and Services Trade Negotiations: Implications For CARICOMDocument118 pagesCRNM - The International Supply of Tertiary Education and Services Trade Negotiations: Implications For CARICOMOffice of Trade Negotiations (OTN), CARICOM SecretariatNo ratings yet
- Robert Smith: Information Security Engineer/ManagerDocument3 pagesRobert Smith: Information Security Engineer/ManagerKumaranNo ratings yet
- CCVP BK C7053373 00 CVP-SRNDDocument198 pagesCCVP BK C7053373 00 CVP-SRNDAhmed SabekNo ratings yet
- Presantation TopicDocument6 pagesPresantation TopicYadvendra BediNo ratings yet
- NTRCA ICT College SyllabusDocument8 pagesNTRCA ICT College SyllabusibnhasibNo ratings yet
- Akshara Dhanala - Guidewire - VCDocument2 pagesAkshara Dhanala - Guidewire - VCRishu SrivastavaNo ratings yet
- Module - 3Document58 pagesModule - 3bldeepak2319No ratings yet
- AIS 2 Chapter 11Document26 pagesAIS 2 Chapter 11Good PersonNo ratings yet
- Oracle DBA Training in ChennaiDocument10 pagesOracle DBA Training in ChennaiTrain TNo ratings yet
- Nist ChecklistDocument30 pagesNist Checklisthakmoch hakmNo ratings yet