Professional Documents
Culture Documents
Forensic
Forensic
Uploaded by
Muhammad TalebCopyright
Available Formats
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCopyright:
Available Formats
Forensic
Forensic
Uploaded by
Muhammad TalebCopyright:
Available Formats
AMERICAN UNIVERSITY OF SCIENCE &
TECHNOLOGY
FACULTY OF ENGINEERING
DEPARTMENT OF COMPUTER SCIENCE AND
COMMUNICATIONS ENGINEERING
Windows Forensic
Image Case Study
MAY 2024
Presented by:
Anthony Debbas
Jamal El Jari
Mohamad Taleb
Submited to:
Dr. Elie Nassr
Copyright 2024 American University of Science and Technology
OUTLINE
Introduction
Objectives
Tools can be Used
Image Acquisition
Analysis of Evidence
Conclusion
Copyright 2024 American University of Science and Technology 1
INTRODUCTION
• In the digital age, understanding and effectively analyzing digital
evidence is paramount in numerous fields, from law
enforcement to cybersecurity. This project delves into the realm
of Windows forensic analysis, focusing on the examination of
digital artifacts within a Windows operating system to uncover
potential evidence relevant to an investigation.
Copyright 2024 American University of Science and Technology 2
Objective
• The primary objective of this project is to demonstrate proficiency in conducting forensic analysis on a
Windows system image. Through a systematic approach, we aim to extract, analyze, and interpret various
artifacts present within the system, shedding light on user activities, system events, and potential security
incidents.
Copyright 2024 American University of Science and Technology
3
Tools Can Be Used
Forensic Toolkit Imager (FTK)
FTK Imager, a free tool, ensures the integrity of digital evidence by analysing
drive images without modifying their original state. It supports all operating
systems, recovers deleted files, parses XFS files, and generates file hashes for
data integrity checks. Therefore, it is a crucial tool for forensic investigations .
Wireshark
Wireshark is the world’s most-used network protocol analysis tool, trusted by
governments, corporations, and academic institutions worldwide. It provides
microscopic-level visibility into network activity by capturing and analyzing network
traffic. With a user-friendly interface available on multiple operating systems,
Wireshark aids in detecting and investigating malicious activity. It supports various
data sources and allows exporting of output in multiple formats.
Autopsy
Autopsy is a modular and user-friendly digital forensics platform used by investigators to
assess computer and phone data. It offers timeline analysis, hash filtering, keyword search, web
artifact extraction, file recovery, and rapid identification of indicators of compromise.
Background jobs run in parallel, providing quick results for targeted keywords. Autopsy also
allows for creating a centralized repository and is an open-source solution. It is currently
available for Windows only.
Copyright 2024 American University of Science and Technology
4
Image Acquisation
FTK Imager is a powerful forensic imaging tool used to acquire disk images and perform various
forensic tasks. Here are the steps to create an image using FTK Imager:
Step2:
Step1: Choose Source
Choose Destination: Next,
Drive: In the "Select
you'll need to specify the
Source" window, choose
destination where you
the drive or device you
want to save the image
want to create an image
file. Click on the "Add"
of. This could be a
button to select the
physical disk, a partition,
destination folder and
or a logical drive.
provide a name for the
image file.
Copyright 2024 American University of Science and Technology
4
Image Acquisation
Step3:
Select Image Type: Choose Step4:
the type of image you want Evidence of information:
to create. FTK Imager offers give some evidence item
several options, including information like case
"Raw (dd)", "E01", and number, examiner and some
"SMART". Select the notes
appropriate type based on
your requirements. The E01
format is commonly used in
forensic investigations.
Copyright 2024 American University of Science and Technology
Image Acquisation
Step6:
Step7 :
Start Imaging: Once you've
Monitor Progress: You can
configured the settings, click
monitor the progress of the
on the "Start" button to begin
imaging process in the FTK
the imaging process. FTK
Imager interface. Depending on
Imager will start creating the
the size of the disk and the
disk image.
options you've selected, this
process may take some time.
Copyright 2024 American University of Science and Technology
Analysis Of Evidence
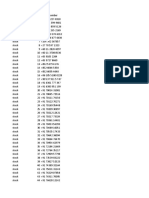
In this section, we'll display a list of all the software that has been downloaded and installed on this machine.
Registry Path:HKEY_LOCAL_MACHINE\SOFTWARE
Copyright 2024 American University of Science and Technology
5
Analysis Of Evidence
EXIF (Exchangeable Image File Format) metadata in Windows 7 refers to the additional information
embedded within image files captured by digital cameras or created by image editing software.
Copyright 2024 American University of Science and Technology
Analysis Of Evidence
In this section, we'll display all file sizes
Registry Path:HKEY_CURRENT_USER\Software\Microsoft\Windows\Shell\Bags\AllFolders
Copyright 2024 American University of Science and Technology
Analysis Of Evidence
Recycle Bin
Registry Path:HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\BitBucket
Copyright 2024 American University of Science and Technology
Analysis Of Evidence
This key contains information about USB controllers and hubs on the system. Each subkey represents a USB
controller or hub and may contain information about attached devices.
Registry Path: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Enum\USB
Copyright 2024 American University of Science and Technology
Analysis Of Evidence
Web browsers like Internet Explorer, Google Chrome, Mozilla Firefox, etc., may store cookies, passwords, and
other account-related information in their respective locations within the registry. These locations may vary
depending on the browser and its version.
Copyright 2024 American University of Science and Technology
Analysis Of Evidence
Web browsing history is primarily stored in the user's profile directory.
Registry Path: HKEY_CURRENT_USER\Software\Google\Chrome
Copyright 2024 American University of Science and Technology
Analysis Of Evidence
User account information, including user profiles, login credentials, and account settings, is stored in the
Windows Registry loction of the path.
Registry Path: Sam\Domains\Account\Users\Names
Copyright 2024 American University of Science and Technology
CONCLUSION
In summary, this Windows forensic project has provided valuable insights into the intricate world of digital
investigations within the Windows environment. Through meticulous analysis and examination of digital
artifacts, we've uncovered a wealth of evidence crucial for understanding past events and behaviors on the
system..
Copyright 2024 American University of Science and Technology
11
THANK YOU!
Copyright 2024 American University of Science and Technology
You might also like
- Forensic Analyses With FTK Imager PDFDocument8 pagesForensic Analyses With FTK Imager PDFGerben0% (1)
- Hands-On Assignment-Management of Word Documents-Student GuideDocument2 pagesHands-On Assignment-Management of Word Documents-Student Guidevictoire BadoNo ratings yet
- Assignment 2Document5 pagesAssignment 2aashishNo ratings yet
- Evidence Acquisition: Lab: Disk ImagingDocument7 pagesEvidence Acquisition: Lab: Disk Imagingalex limNo ratings yet
- Imaging Using FTK Imager - Shweta A. ChawlaDocument7 pagesImaging Using FTK Imager - Shweta A. ChawlaToan Phan ThanhNo ratings yet
- 15 BEST Digital Forensic Tools in 2020 (Free - Paid)Document9 pages15 BEST Digital Forensic Tools in 2020 (Free - Paid)Darmoni Laishram100% (1)
- CF Lab FileDocument27 pagesCF Lab FileArpit RNo ratings yet
- Current Computer Forensics ToolsDocument15 pagesCurrent Computer Forensics ToolsVediappan GaneshanNo ratings yet
- Digital Forensics Lab Manual-Converted-CompressedDocument44 pagesDigital Forensics Lab Manual-Converted-Compressednaman sethi100% (1)
- NDG Forensicsv2 Lab 01Document34 pagesNDG Forensicsv2 Lab 01fovov27364No ratings yet
- Technology in Forensic Acoounting InvestigationDocument12 pagesTechnology in Forensic Acoounting Investigationheretik_pNo ratings yet
- Digital Image ForensicsDocument6 pagesDigital Image ForensicsMUSA SAVAŞKANNo ratings yet
- CSF Unit 4Document21 pagesCSF Unit 4Yaswanth Kumar Karaka (Yash)No ratings yet
- Cyber Forensics - Lab ManualDocument36 pagesCyber Forensics - Lab Manualashutosh.bhattarao100% (2)
- Windows Forensic Investigations Using PowerForensics ToolDocument7 pagesWindows Forensic Investigations Using PowerForensics Toollissette0191No ratings yet
- Microsoft Windows Forensic InvestigationDocument7 pagesMicrosoft Windows Forensic InvestigationMaraNo ratings yet
- FTK Imager Eforensics Mag Rebranded FINAL Aug2014 PDFDocument109 pagesFTK Imager Eforensics Mag Rebranded FINAL Aug2014 PDFJulian David GrijalbaNo ratings yet
- Performance Evaluation of Open-Source Disk Imaging Tools For Collecting Digital EvidenceDocument9 pagesPerformance Evaluation of Open-Source Disk Imaging Tools For Collecting Digital EvidencefedoracoreuserNo ratings yet
- Digital Forensics Case Project SolutionDocument11 pagesDigital Forensics Case Project SolutionQomindawoNo ratings yet
- Eforensics 08 2014-2Document109 pagesEforensics 08 2014-2rmieringeominasNo ratings yet
- ForensicsDocument8 pagesForensicsAmri ThomsonNo ratings yet
- Digital Forensic Analysis Lab ExerciseDocument3 pagesDigital Forensic Analysis Lab Exercisealshdadyfhmy398100% (1)
- 1-Reference Material I Cse4004 Digital-Forensics Eth 1.1 47 Cse4004Document10 pages1-Reference Material I Cse4004 Digital-Forensics Eth 1.1 47 Cse4004Nigel JohnNo ratings yet
- DF FinalDocument24 pagesDF FinalIshika PatelNo ratings yet
- Most Used Digital Forensics ToolsDocument9 pagesMost Used Digital Forensics Toolsprathimapesaru7No ratings yet
- Sec535 PR PDFDocument23 pagesSec535 PR PDFFREDDY ALLAN PALACIOS GONZÁLEZNo ratings yet
- Cyber Security Da1 Name: Sreaya.V (21BIT0098) A1+TA1 Slot Cyber Forensics Workshop DAY 1 (12 April, 2024)Document19 pagesCyber Security Da1 Name: Sreaya.V (21BIT0098) A1+TA1 Slot Cyber Forensics Workshop DAY 1 (12 April, 2024)SreayaNo ratings yet
- Research PaperDocument8 pagesResearch PaperAnishNo ratings yet
- Design and Implementation of A Live-Analysis Digital Forensic SystemDocument5 pagesDesign and Implementation of A Live-Analysis Digital Forensic SystemmarcebrasilNo ratings yet
- Cyber Defense Forensic Analyst - Real World Hands-On ExamplesDocument17 pagesCyber Defense Forensic Analyst - Real World Hands-On ExamplesSandeep Kumar SeeramNo ratings yet
- Unit 4Document40 pagesUnit 4Om SinghNo ratings yet
- DF TeamDocument4 pagesDF Teamßrijesh PatelNo ratings yet
- Ef Free 01.12. TeaserDocument18 pagesEf Free 01.12. TeasereForensicsMag100% (1)
- Computer Forensic Investigation: Learnhacking - OnlineDocument14 pagesComputer Forensic Investigation: Learnhacking - OnlineDeep ChandrakarNo ratings yet
- Week 8 - Computer Forensics - AutopsyDocument56 pagesWeek 8 - Computer Forensics - Autopsykishor jha100% (1)
- 1 Krist Calvin 2020 BSDocument94 pages1 Krist Calvin 2020 BSFamara GueyeNo ratings yet
- A Machine Learning Technique To Detect MalwareDocument8 pagesA Machine Learning Technique To Detect MalwareIJRASETPublicationsNo ratings yet
- ForensicsDocument3 pagesForensicsJosiah MarcanoNo ratings yet
- Lab 5Document3 pagesLab 5DeepakNo ratings yet
- Live Memory Forensic AnalysisDocument4 pagesLive Memory Forensic AnalysisEditor IJRITCCNo ratings yet
- Computer Forensics Data Recovery Perspective Over Windows and UnixDocument3 pagesComputer Forensics Data Recovery Perspective Over Windows and UnixInternational Journal of Innovative Science and Research TechnologyNo ratings yet
- Tool ComparisonDocument8 pagesTool ComparisonAndresMenkerNo ratings yet
- Computer ForensicsDocument2 pagesComputer ForensicsKevin NeshNo ratings yet
- An Exploration of Artefacts of Remote Desktop Applications On WinDocument9 pagesAn Exploration of Artefacts of Remote Desktop Applications On Winasmm.rahamanNo ratings yet
- Digital Forensics: Tools & IdentificationDocument27 pagesDigital Forensics: Tools & IdentificationPoorna Chander GanjiNo ratings yet
- Digital Investigation: Jan CollieDocument11 pagesDigital Investigation: Jan CollieLeonardo WaingartenNo ratings yet
- Practical 9 ToolsDocument4 pagesPractical 9 ToolsTing Zhi Peng (Ethan)No ratings yet
- Information Security ManagementDocument12 pagesInformation Security ManagementARYA DUBEY 20BCE0908No ratings yet
- Helix Tool Use CaseDocument32 pagesHelix Tool Use CaseSantosh kumar beheraNo ratings yet
- 1 To 52Document256 pages1 To 52vijayalakshmi sNo ratings yet
- Study of Importance of Digital ForensicsDocument6 pagesStudy of Importance of Digital ForensicsMr Abdalla Mohamed AliNo ratings yet
- 3 - Investigating Cyber Crimes - Introduction To Cyber Forensic - 1Document5 pages3 - Investigating Cyber Crimes - Introduction To Cyber Forensic - 1SINGE JUDENo ratings yet
- Lab Manual Module 03Document30 pagesLab Manual Module 03Hiếu Nguyễn NgọcNo ratings yet
- Cyber Forensics ToolsDocument4 pagesCyber Forensics ToolsJeya Balasubramani100% (1)
- Malware Lab ConceptDocument44 pagesMalware Lab ConceptPrashanthArathiShineyNo ratings yet
- Learning Objectives of Memory Analysis: SEPTEMBER 27, 2020Document14 pagesLearning Objectives of Memory Analysis: SEPTEMBER 27, 2020simasiku.oliver99No ratings yet
- LaRon Walker - Computer Forensic ToolsDocument9 pagesLaRon Walker - Computer Forensic ToolsLaRon WalkerNo ratings yet
- FTK Complete Practical GuideDocument43 pagesFTK Complete Practical GuideRishi KaulNo ratings yet
- Digital Forensics Basics: A Practical Guide Using Windows OSFrom EverandDigital Forensics Basics: A Practical Guide Using Windows OSNo ratings yet
- Relative SizeDocument20 pagesRelative SizeMoh SaadNo ratings yet
- Api 653 Tank Inspection, Tank Maintenance, AND Causes of Tank FailureDocument43 pagesApi 653 Tank Inspection, Tank Maintenance, AND Causes of Tank FailureArif PriyadiNo ratings yet
- ISTQB CTAL TTA v4 - 0 Sample Exam Answers Set ADocument32 pagesISTQB CTAL TTA v4 - 0 Sample Exam Answers Set AAnand AzhagarNo ratings yet
- Handbook of Department of Civil Eng.25.08.14Document128 pagesHandbook of Department of Civil Eng.25.08.14Shanmuga SundaramNo ratings yet
- 23014359-1 23014359 Invoice 160220234Document1 page23014359-1 23014359 Invoice 160220234san_misusNo ratings yet
- How To Configure ElasticDocument25 pagesHow To Configure ElasticSkander GuermaziNo ratings yet
- AIX Training-D1P1Document39 pagesAIX Training-D1P1Akang Zaenal MasterMamayukeroNo ratings yet
- SPP-R310: Windows Driver ManualDocument39 pagesSPP-R310: Windows Driver ManualIbrahim AL-SORAIHINo ratings yet
- JavascriptDocument62 pagesJavascriptChristopherNo ratings yet
- 8I Heating and Cooling Multiple Choice TestDocument3 pages8I Heating and Cooling Multiple Choice Testapi-369814690% (10)
- Contoh Soal Materi Bab 2 BinggrisDocument5 pagesContoh Soal Materi Bab 2 Binggrisersa wahyu100% (1)
- LABORATORY-EXERCISE (2) Assemblying MultimeterDocument15 pagesLABORATORY-EXERCISE (2) Assemblying MultimeterAliah Joy JunioNo ratings yet
- CAT Oc Disc Item Type Maximo # Epc Contractor Tag NumberDocument16 pagesCAT Oc Disc Item Type Maximo # Epc Contractor Tag NumberMai Thế ToanNo ratings yet
- Effects of Internet Marketing On Consumers Behavior PPT FDDocument10 pagesEffects of Internet Marketing On Consumers Behavior PPT FDKirsten Jesah BuenaNo ratings yet
- New Microsoft Excel WorksheetDocument6 pagesNew Microsoft Excel WorksheetArvind HarikrishnanNo ratings yet
- Parts Catalogue: Passion PRODocument129 pagesParts Catalogue: Passion PROEdar Jhon Montenegro RimarachinNo ratings yet
- New Revised Esc101 Prutor All Labs and Quiz Problems by Sujal PDFDocument146 pagesNew Revised Esc101 Prutor All Labs and Quiz Problems by Sujal PDFRithwin KodumuriNo ratings yet
- Automated Excel DetailsDocument10 pagesAutomated Excel DetailsPrashant mhamunkarNo ratings yet
- Mod Menu Log - Com - Miniclip.eightballpoolDocument3 pagesMod Menu Log - Com - Miniclip.eightballpoolGalo casaNo ratings yet
- Teledentistry in Practice: Literature Review: Oral Medicine and DiagnosisDocument3 pagesTeledentistry in Practice: Literature Review: Oral Medicine and DiagnosisnadyaNo ratings yet
- Disk IO ErrorsDocument10 pagesDisk IO Errorsiftikhar ahmedNo ratings yet
- Behaviour of 3D-Panels For Structural Applications Under General Loading: A State-Of-The-ArtDocument10 pagesBehaviour of 3D-Panels For Structural Applications Under General Loading: A State-Of-The-ArtVirat DesaiNo ratings yet
- 5 Natiora MahagagaDocument13 pages5 Natiora MahagagaSafidiniaina Lahatra RasamoelinaNo ratings yet
- Best CAD NotesDocument122 pagesBest CAD Noteswubie bayeNo ratings yet
- MIS Chapter-7Document45 pagesMIS Chapter-7Lovely Ann De GuzmanNo ratings yet
- Power Optimization in 5G Networks: A Step Towards Green CommunicationDocument20 pagesPower Optimization in 5G Networks: A Step Towards Green CommunicationElmustafa Sayed Ali Ahmed100% (1)
- VerveDocument2 pagesVerveAtulNo ratings yet
- Service Manual: e-STUDIO5508A/6508A/7508A/ 8508ADocument1,328 pagesService Manual: e-STUDIO5508A/6508A/7508A/ 8508Athanh nguyendatthanh100% (2)
- Mastermind Notes - Stefan Georgi, Justin Goff - 2019Document11 pagesMastermind Notes - Stefan Georgi, Justin Goff - 2019Baraheen E Qaati'ahNo ratings yet