Professional Documents
Culture Documents
Security_Concepts_Introduction
Security_Concepts_Introduction
Uploaded by
bala raman0 ratings0% found this document useful (0 votes)
3 views20 pagesCNS
Material
Copyright
© © All Rights Reserved
Available Formats
PPTX, PDF, TXT or read online from Scribd
Share this document
Did you find this document useful?
Is this content inappropriate?
Report this DocumentCNS
Material
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
0 ratings0% found this document useful (0 votes)
3 views20 pagesSecurity_Concepts_Introduction
Security_Concepts_Introduction
Uploaded by
bala ramanCNS
Material
Copyright:
© All Rights Reserved
Available Formats
Download as PPTX, PDF, TXT or read online from Scribd
Download as pptx, pdf, or txt
You are on page 1of 20
Security Concepts: Introduction
Understanding the Basics of
Cybersecurity
[Your Name]
[Date]
Agenda
• • The Need for Security
• • Security Approaches
• • Principles of Security
• • Types of Security Attacks
• • Security Services
• • Security Mechanisms
• • A Model for Network Security
• • Cryptography Concepts and Techniques
• - Introduction
The Need for Security
• Increasing Cyber Threats
• Protection of Sensitive Information
• Prevention of Unauthorized Access
• Ensuring Data Integrity and Availability
Security Approaches
• Preventive Measures
• Detective Measures
• Corrective Measures
Principles of Security
• Confidentiality
• Integrity
• Availability
• Authentication
• Non-repudiation
Types of Security Attacks
• Malware (Viruses, Worms, Trojans)
• Phishing
• Ransomware
• Denial of Service (DoS) Attacks
• Man-in-the-Middle Attacks
Security Services
• Authentication
• Access Control
• Data Confidentiality
• Data Integrity
• Non-repudiation
Security Mechanisms
• Cryptographic Techniques
• Digital Signatures
• Access Controls
• Firewalls
• Intrusion Detection Systems (IDS)
A Model for Network Security
• Layers of Network Security
• Security Policies
• Security Technologies
• Security Management
Cryptography Concepts and
Techniques: Introduction
• Definition and Purpose of Cryptography
• Historical Context
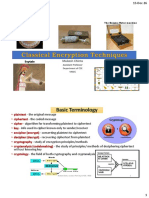
Plaintext and Ciphertext
• Explanation of Plaintext
• Explanation of Ciphertext
• Conversion Process
Substitution Techniques
• Caesar Cipher
• Monoalphabetic Cipher
• Polyalphabetic Cipher
Transposition Techniques
• Rail Fence Cipher
• Columnar Transposition Cipher
Encryption and Decryption
• Definition and Process of Encryption
• Definition and Process of Decryption
• Examples
Symmetric and Asymmetric Key
Cryptography
• Symmetric Key Cryptography (Single Key)
• Asymmetric Key Cryptography (Public and
Private Keys)
• Differences and Use Cases
Steganography
• Definition and Techniques
• Uses and Examples
Key Range and Key Size
• Importance of Key Size
• Key Range Explanation
• Impact on Security
Possible Types of Attacks
• Brute Force Attacks
• Cryptanalysis
• Side-channel Attacks
Conclusion
• Summary of Key Points
• Importance of Ongoing Security Education
• Encouragement to Stay Informed
Q&A
• Open the floor for questions
• Provide contact information for further
inquiries
You might also like
- Information Security Management Concepts and PracticeDocument870 pagesInformation Security Management Concepts and PracticeHILTON CESPEDES RIVERO100% (1)
- Problems Chaptr 1 PDFDocument4 pagesProblems Chaptr 1 PDFcaught inNo ratings yet
- 09 - SRX - Ipsec VPNDocument64 pages09 - SRX - Ipsec VPNLuc TranNo ratings yet
- Week 1 Lecture 1 Information SecurityDocument28 pagesWeek 1 Lecture 1 Information SecurityZulkifl HasanNo ratings yet
- IS Lecture 02 - Basics and Domains (1)Document29 pagesIS Lecture 02 - Basics and Domains (1)Abdullah LïllãNo ratings yet
- Instructor: DR - Maaz Bin Ahmad. 0333-5264960: Maaz@pafkiet - Edu.pkDocument54 pagesInstructor: DR - Maaz Bin Ahmad. 0333-5264960: Maaz@pafkiet - Edu.pkSubhan50No ratings yet
- new trainingDocument2 pagesnew training2111cs040096No ratings yet
- Network Security, Lecture 1Document10 pagesNetwork Security, Lecture 1Saher KhalilNo ratings yet
- Cryptography: MS Information SecurityDocument44 pagesCryptography: MS Information SecuritymudassaruetNo ratings yet
- Cybersecurity Professional Training PDFDocument2 pagesCybersecurity Professional Training PDFTester MaheNo ratings yet
- Lecture 1Document9 pagesLecture 1Muhammad NadeemNo ratings yet
- 01.1 - Ethical HackingDocument21 pages01.1 - Ethical HackingHACKER HACKERNo ratings yet
- Network Security & Cryptography: - Lecture# 1 - Dr. Syed Irfan Ullah - Asst. Professor - Abasyn University PeshawarDocument37 pagesNetwork Security & Cryptography: - Lecture# 1 - Dr. Syed Irfan Ullah - Asst. Professor - Abasyn University Peshawarnazer100% (1)
- IS336 Lecture 0Document3 pagesIS336 Lecture 0j art ,education,and lifestyleNo ratings yet
- 07 PENDIENTE ECSS-brochure-2023Document14 pages07 PENDIENTE ECSS-brochure-2023enrique prats perezNo ratings yet
- 1 Introduction Network Security CryptographyDocument76 pages1 Introduction Network Security CryptographyPulkit RanjanNo ratings yet
- 2 Security AttacksDocument37 pages2 Security Attackssasanaravi2020No ratings yet
- Cyber Security Course ContentDocument8 pagesCyber Security Course ContentPaviNo ratings yet
- NSP-background 2024Document51 pagesNSP-background 2024ASHNA ANo ratings yet
- CISSPDocument2 pagesCISSPzollian.fxNo ratings yet
- LEC TwoDocument19 pagesLEC TwoDavis PunjilaNo ratings yet
- Cryptography: Securing The Information Age: Presented By: Aniruddha SanyalDocument10 pagesCryptography: Securing The Information Age: Presented By: Aniruddha SanyalAmitrajdan SinghNo ratings yet
- Cyber SecurityDocument178 pagesCyber SecurityRenGoku0% (1)
- Cyber Security Course ContentDocument6 pagesCyber Security Course ContentTristanNo ratings yet
- Cybersecurity Professional TrainingDocument2 pagesCybersecurity Professional TrainingKHALIDNo ratings yet
- IS73 Information Security - IntroductionDocument16 pagesIS73 Information Security - IntroductionArya KumariNo ratings yet
- Network Security Postgraduate CourseDocument34 pagesNetwork Security Postgraduate CourseMohammed Al-RadwanNo ratings yet
- Cryptography and Network Security - Module - 1Document51 pagesCryptography and Network Security - Module - 1srujana hulkoduNo ratings yet
- Cns-Unit-1 Part 1Document44 pagesCns-Unit-1 Part 1Free FireNo ratings yet
- CRYPTOGRAPHY & NETWORK SECURITY (Autosaved)Document82 pagesCRYPTOGRAPHY & NETWORK SECURITY (Autosaved)asjadzaki2021No ratings yet
- Network Security Postgraduate CourseDocument34 pagesNetwork Security Postgraduate CourseMohammed Al-RadwanNo ratings yet
- CH 1introduction and Classical CipherDocument143 pagesCH 1introduction and Classical Cipherkrisha GotiNo ratings yet
- Lecture2 Intro (Part-II)Document42 pagesLecture2 Intro (Part-II)Love GatesNo ratings yet
- Isc2 Cisssp: Certification TrainingDocument15 pagesIsc2 Cisssp: Certification TrainingArifur RahmanNo ratings yet
- Data Security and Encryption CS465Document12 pagesData Security and Encryption CS465waqas jaanNo ratings yet
- International Journal On Cryptography and Information Security IJCISDocument2 pagesInternational Journal On Cryptography and Information Security IJCISijcisjournalNo ratings yet
- The Awareness of Cybersecurity: Cybersecurity Lecturer: Jumana KhwailehDocument173 pagesThe Awareness of Cybersecurity: Cybersecurity Lecturer: Jumana Khwailehdavidachieng80No ratings yet
- Security and ProtectionDocument17 pagesSecurity and ProtectionWestore AcidNo ratings yet
- IANS Unit 1 Part1Document26 pagesIANS Unit 1 Part1Amrin MulaniNo ratings yet
- Cloud SecurityDocument4 pagesCloud SecurityPrince Kumar BhatiaNo ratings yet
- Network+ Short Course - Week 4 PDFDocument67 pagesNetwork+ Short Course - Week 4 PDFMurad sulemanNo ratings yet
- Cryptography and NSDocument68 pagesCryptography and NSWONDYE DESTANo ratings yet
- Gráfo "Write") Is The Study of Message Secrecy. in Modern Times, It Has Become A Branch ofDocument76 pagesGráfo "Write") Is The Study of Message Secrecy. in Modern Times, It Has Become A Branch ofnazerNo ratings yet
- Certified Ethical Hacker: Course SpecificationsDocument6 pagesCertified Ethical Hacker: Course SpecificationsvarpaliaNo ratings yet
- Lecture 01Document16 pagesLecture 01nedal.mo7ammad10531No ratings yet
- Cybersecurity EssentialsDocument6 pagesCybersecurity EssentialsHelloMukamaNo ratings yet
- Cybersecurity Professional TrainingDocument2 pagesCybersecurity Professional TrainingDeeq HuseenNo ratings yet
- Seguridad P1Document54 pagesSeguridad P1Andres CandoNo ratings yet
- EC-Council Certified Ethical Hacker (CEH) v10.0: Target AudienceDocument6 pagesEC-Council Certified Ethical Hacker (CEH) v10.0: Target AudienceMila IrisNo ratings yet
- Unit1 Securitymodel 1Document27 pagesUnit1 Securitymodel 1Amrin MulaniNo ratings yet
- Cryptography: Securing The Information Age: Made By: Mansi SharmaDocument17 pagesCryptography: Securing The Information Age: Made By: Mansi SharmaMansi SharmaNo ratings yet
- Chapter 1-4Document135 pagesChapter 1-4WONDYE DESTANo ratings yet
- Network SecurityDocument14 pagesNetwork Securitytushar63No ratings yet
- Let'S Discuss Security !!: Louma Makkouk, Cybersecurity. Omar Rajab, CybersecurityDocument24 pagesLet'S Discuss Security !!: Louma Makkouk, Cybersecurity. Omar Rajab, Cybersecurityomar rajabNo ratings yet
- Simple Security PrinciplesDocument29 pagesSimple Security PrinciplesPanos KoukiosNo ratings yet
- CH 1Document36 pagesCH 1aya mohamedNo ratings yet
- NS 1Document96 pagesNS 1elitejoker622No ratings yet
- Slide 1Document17 pagesSlide 1Junaid KhanNo ratings yet
- Cryptography Overview and TerminologiesDocument17 pagesCryptography Overview and TerminologiesMir Jaffar Ali KhanNo ratings yet
- Intro To Cyber 1Document21 pagesIntro To Cyber 1Michael WagxyNo ratings yet
- CC Certified in Cybersecurity The Complete ISC2 Certification Study GuideFrom EverandCC Certified in Cybersecurity The Complete ISC2 Certification Study GuideNo ratings yet
- Steganography With RC4 and Pixel Shuffling Encryption AlgorithmsDocument5 pagesSteganography With RC4 and Pixel Shuffling Encryption AlgorithmsesrNo ratings yet
- Classsical Encryption Techniques MukeshDocument13 pagesClasssical Encryption Techniques MukeshMukeshNo ratings yet
- How To Configure A Service Provider - ABAP ConnectivityDocument9 pagesHow To Configure A Service Provider - ABAP ConnectivitywilliammgcNo ratings yet
- 09 - LECTURE Security Testing For Mobile and Web AppsDocument36 pages09 - LECTURE Security Testing For Mobile and Web AppsTeng Jun tehNo ratings yet
- Cryptography: Seminar ReportDocument17 pagesCryptography: Seminar ReportAyush WagdreNo ratings yet
- OT Cybersecurity Competency Framework - V5Document113 pagesOT Cybersecurity Competency Framework - V5Claudio Osvaldo Vargas Farfan100% (1)
- ET15 Sophos Central Enpoint and Server Engineer v2Document16 pagesET15 Sophos Central Enpoint and Server Engineer v2rodrigoezepyNo ratings yet
- Substitution TechniquesDocument17 pagesSubstitution TechniquesChetan ChauhanNo ratings yet
- Cryptography - Lecture2Document38 pagesCryptography - Lecture2AbhijeetNo ratings yet
- Authentication and Authorization Week 6Document26 pagesAuthentication and Authorization Week 6zenkaevaaiymNo ratings yet
- Windows Server 2022 Security GuideDocument44 pagesWindows Server 2022 Security GuideSivasakti MarimuthuNo ratings yet
- EC-Council Certified Ethical Hacker (CEH) v.12 Courses - New HorizonsDocument7 pagesEC-Council Certified Ethical Hacker (CEH) v.12 Courses - New Horizonsdaliodsouza1019No ratings yet
- The Biometric Passport Standard - Mrtd-cs08prtDocument88 pagesThe Biometric Passport Standard - Mrtd-cs08prtaichbergerNo ratings yet
- Computer Security Presentation ScriptDocument6 pagesComputer Security Presentation ScriptAaron CouchNo ratings yet
- ISO 27001 MetricsDocument2 pagesISO 27001 MetricsJustina MoncadaNo ratings yet
- WEB Security: Data and Networks SecurityDocument21 pagesWEB Security: Data and Networks SecurityasadNo ratings yet
- Cript 123 InfoDocument7 pagesCript 123 InfoChirri CorpNo ratings yet
- Network Security Principles & Practices: by Saadat Malik Cisco Press 2003Document9 pagesNetwork Security Principles & Practices: by Saadat Malik Cisco Press 2003XozanNo ratings yet
- Certificate Detection ScaleconfcoDocument25 pagesCertificate Detection ScaleconfcodarthdavidNo ratings yet
- Cyber Security Essay 2Document4 pagesCyber Security Essay 2Super FlyNo ratings yet
- 01 Introduction To Web Application SecurityDocument11 pages01 Introduction To Web Application SecurityJoshuaNo ratings yet
- 100 Cyber ThreatsDocument103 pages100 Cyber ThreatsAyaz Ahmed RajNo ratings yet
- Management 22509Document14 pagesManagement 22509sagarpatil03012No ratings yet
- Bluetooth Security Considerations: Seminar by Anoop AravindDocument21 pagesBluetooth Security Considerations: Seminar by Anoop Aravindka03No ratings yet
- Kaspersky Web Traffic Security: The Benefits and Strategic Importance ofDocument4 pagesKaspersky Web Traffic Security: The Benefits and Strategic Importance ofhappy girlNo ratings yet
- Academic CatalogDocument3 pagesAcademic CatalogSuman GhimireNo ratings yet
- Configuring Macsec Encryption: Macsec and Cisco Trustsec OverviewDocument17 pagesConfiguring Macsec Encryption: Macsec and Cisco Trustsec Overviewgarmahis79No ratings yet