DocumentRemote Code Executionuploaded by
DocumentRemote Code Executionuploaded by Kika Arteaga F
Kika Arteaga F DocumentReverse DNSuploaded by
DocumentReverse DNSuploaded by Kika Arteaga F
Kika Arteaga F DocumentEN - Security management for weblogic 8uploaded by
DocumentEN - Security management for weblogic 8uploaded by Kika Arteaga F
Kika Arteaga F DocumentEN - Time based blind SQL Injection using heavy queriesuploaded by
DocumentEN - Time based blind SQL Injection using heavy queriesuploaded by Kika Arteaga F
Kika Arteaga F DocumentEN - BlackHat US 2011 DotDotPwn directory traversal fuzzeruploaded by
DocumentEN - BlackHat US 2011 DotDotPwn directory traversal fuzzeruploaded by Kika Arteaga F
Kika Arteaga F DocumentEN - Bypassing URL authentication and authorization with HTTP verb tamperinguploaded by
DocumentEN - Bypassing URL authentication and authorization with HTTP verb tamperinguploaded by Kika Arteaga F
Kika Arteaga F DocumentStuxnet Malware Analysis.pdfuploaded by
DocumentStuxnet Malware Analysis.pdfuploaded by Kika Arteaga F
Kika Arteaga F Documentarticulo_metodos_de_cifrado_en_windows.pdfuploaded by
Documentarticulo_metodos_de_cifrado_en_windows.pdfuploaded by Kika Arteaga F
Kika Arteaga F Documentalgoritmos de estagnografiauploaded by
Documentalgoritmos de estagnografiauploaded by Kika Arteaga F
Kika Arteaga F DocumentRedes Telefonicas Inteligentesuploaded by
DocumentRedes Telefonicas Inteligentesuploaded by Kika Arteaga F
Kika Arteaga F Documenttelecomunicaciones canal asociado r2uploaded by
Documenttelecomunicaciones canal asociado r2uploaded by Kika Arteaga F
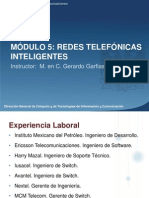
Kika Arteaga F DocumentModulo Redes Telefonicas Inteligentesuploaded by
DocumentModulo Redes Telefonicas Inteligentesuploaded by Kika Arteaga F
Kika Arteaga F Documentsenalizacion R2uploaded by
Documentsenalizacion R2uploaded by Kika Arteaga F
Kika Arteaga F DocumentForerense en linuxuploaded by
DocumentForerense en linuxuploaded by Kika Arteaga F
Kika Arteaga F Documentpractica de criptografiauploaded by
Documentpractica de criptografiauploaded by Kika Arteaga F
Kika Arteaga F DocumentHacking For Beginners.pdfuploaded by
DocumentHacking For Beginners.pdfuploaded by Kika Arteaga F
Kika Arteaga F Documentcriptovirulogiauploaded by
Documentcriptovirulogiauploaded by Kika Arteaga F
Kika Arteaga F DocumentCrypto Virologyuploaded by
DocumentCrypto Virologyuploaded by Kika Arteaga F
Kika Arteaga F DocumentManual de instalación NESSUSuploaded by
DocumentManual de instalación NESSUSuploaded by Kika Arteaga F
Kika Arteaga F DocumentLinux_07_08_2009_ESuploaded by
DocumentLinux_07_08_2009_ESuploaded by Kika Arteaga F
Kika Arteaga F DocumentCriptografiauploaded by
DocumentCriptografiauploaded by Kika Arteaga F
Kika Arteaga F DocumentManual Practico Sq luploaded by
DocumentManual Practico Sq luploaded by Kika Arteaga F
Kika Arteaga F
Professional Documents
Culture Documents